
When building or consuming APIs, the security of how users authenticate themselves is paramount. It's not just about preventing unauthorized access; it's about ensuring data integrity, maintaining user trust, and complying with regulations. Often, the clarity and accuracy of this authentication process are directly tied to the quality of the documentation provided. If developers can't easily understand how to authenticate, they might resort to insecure workarounds or abandon the API altogether.
My own experiences have shown that well-documented authentication mechanisms are the bedrock of secure API integrations. Conversely, vague or incomplete documentation can lead to significant vulnerabilities. This is why focusing on detailed, understandable api security authentication documentation is not just a good practice, it's a necessity for any robust API strategy.
Table of Contents
Understanding the Basics of API Authentication
At its core, API authentication is the process of verifying the identity of a user or client attempting to access an API. This ensures that only legitimate parties can interact with your resources. Without proper authentication, anyone could potentially read, modify, or delete sensitive data, leading to breaches and operational chaos.
Key Authentication Concepts
Several fundamental concepts underpin API authentication. These include credentials (like API keys, tokens, or usernames/passwords), authentication schemes (the protocols used to present credentials), and authorization (the process of determining what authenticated users are allowed to do). Understanding these elements is the first step toward securing your API effectively.
Common Authentication Methods Explained

The landscape of API authentication is diverse, with various methods suited for different use cases. Each method has its own set of strengths, weaknesses, and implementation details that must be clearly communicated.
API Keys
API keys are perhaps the simplest form of authentication. They are unique identifiers assigned to users or applications to grant access. While easy to implement, they can be less secure if not managed properly. Documentation should detail how to obtain, manage, and securely transmit these keys, emphasizing that they should be treated like passwords.
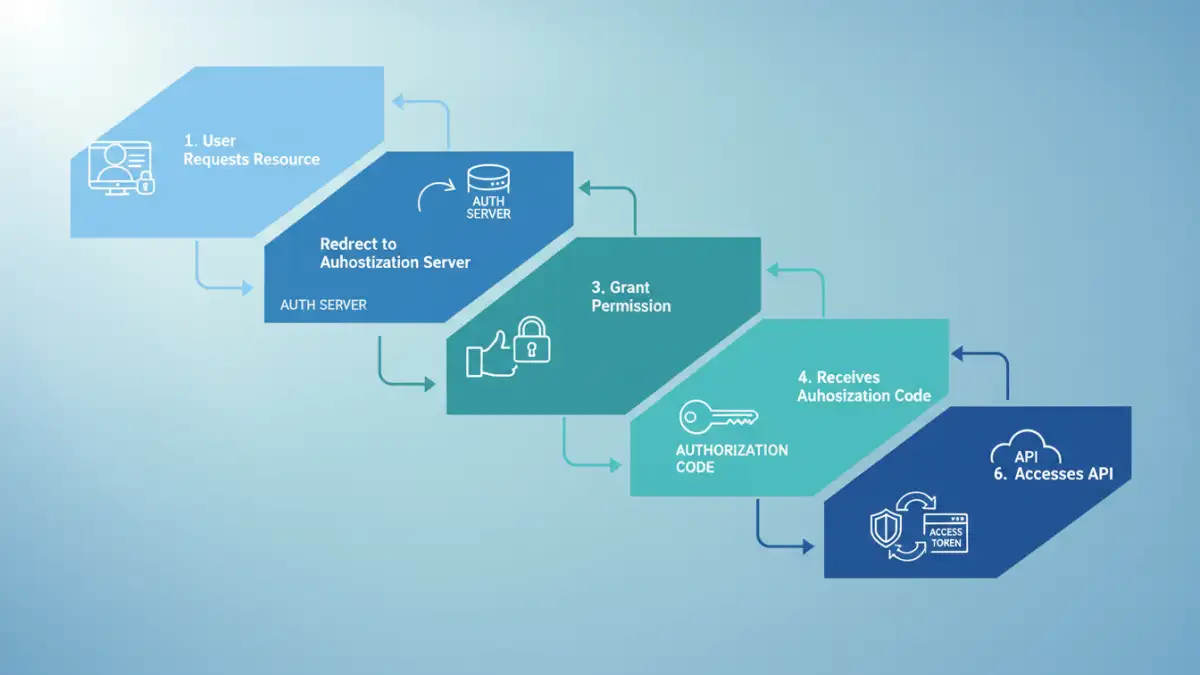
OAuth 2.0 and OpenID Connect
For more complex scenarios, especially those involving user delegation or third-party access, OAuth 2.0 and OpenID Connect are industry standards. OAuth 2.0 is an authorization framework that allows users to grant third-party applications access to their resources without sharing their credentials directly. OpenID Connect builds on OAuth 2.0 to provide authentication. Documenting these protocols requires explaining flows like Authorization Code, Implicit, and Client Credentials, along with scopes and token management.
JSON Web Tokens (JWT)
JWTs are a popular method for securely transmitting information between parties as a JSON object. They are often used in conjunction with token-based authentication. A JWT consists of three parts: a header, a payload, and a signature. The documentation must explain how to generate, validate, and refresh these tokens, as well as the importance of signing them correctly to prevent tampering.
Strategies for Documenting Authentication
Effective documentation goes beyond simply listing authentication methods. It needs to provide a clear, actionable guide for developers. This includes providing code examples, defining required headers, and explaining error responses.
Code Examples and Snippets
Developers learn best by seeing. Providing practical code snippets in multiple popular programming languages (e.g., Python, JavaScript, Java) for each authentication method significantly lowers the barrier to entry. These examples should demonstrate how to include credentials, make a basic request, and handle responses.
Error Handling and Troubleshooting
When authentication fails, clear error messages are crucial. Documentation should detail common authentication error codes (e.g., 401 Unauthorized, 403 Forbidden) and explain their specific meanings. It should also offer troubleshooting tips for common issues developers might encounter, such as expired tokens or incorrect key formats.
Best Practices for API Auth Docs
To ensure your api security authentication documentation is truly effective, adhering to certain best practices is essential. These practices focus on clarity, security, and developer experience.
Keep it Concise and Clear
Avoid jargon where possible. Use simple language and break down complex processes into manageable steps. A developer should be able to understand how to authenticate within minutes of reading the relevant section.
Emphasize Security
Continuously remind developers about security best practices. This includes advice on not hardcoding credentials, using HTTPS, storing secrets securely, and rotating API keys or tokens regularly. Highlighting the consequences of insecure authentication practices can reinforce their importance.
Advanced Security Considerations
Beyond basic authentication, APIs often require more sophisticated security measures. Documenting these clearly is vital for maintaining a high level of security.
Rate Limiting and Throttling
To prevent abuse and ensure service availability, APIs often implement rate limiting. Documentation should clearly state the rate limits, how they are enforced (e.g., per user, per IP address), and what happens when limits are exceeded (e.g., 429 Too Many Requests error).
IP Whitelisting and Access Control
For highly sensitive APIs, restricting access to specific IP addresses or network ranges can add an extra layer of security. If implemented, the documentation must explain how to request IP whitelisting and the process for managing these access controls.
Comparison of Authentication Document Clarity
| Documentation Aspect | Clear Documentation | Unclear Documentation | Impact |
|---|---|---|---|
| Method Explanation | Detailed description of each method (API Keys, OAuth, JWT) with use cases. | Vague descriptions, missing use cases. | Developer confusion, incorrect implementation. |
| Code Examples | Provided in multiple languages, easy to copy-paste. | Missing, outdated, or incorrect examples. | Increased development time, frustration. |
| Error Handling | Clear explanation of error codes and troubleshooting steps. | Generic error messages, no guidance. | Difficulty debugging, prolonged integration issues. |
| Security Emphasis | Highlights best practices for credential management and secure transmission. | Lacks security advice or downplays risks. | Increased vulnerability to attacks. |
| Scope/Permissions | Clearly defines available scopes and their implications. | Ambiguous or undocumented scopes. | Potential for over-privileged access. |