
Just last week, a colleague came to me, frustrated. He had an important project brief, encrypted for security, but the client needed it in a different format, and the original encryption tool wasn't playing nice. This isn't an uncommon scenario. In our line of work, we constantly deal with sensitive information that needs robust protection, often across various file types and platforms. Ensuring that a document remains secure, whether it's a PDF, a Word document, or a spreadsheet, is paramount, and handling these different formats with consistent security can be a real headache.
Securing information effectively means understanding how to apply robust password encryption standards, regardless of the file's native format. This article will guide you through the best practices for achieving seamless and strong security across your diverse document landscape.
Table of Contents
Understanding the Challenge of Multi-Format Security
Protecting sensitive data involves more than just slapping a password on a file. The real challenge emerges when you need that protection to be consistent and effective across different document types – PDFs, Word documents, Excel spreadsheets, ZIP archives, and more. Each format often comes with its own native security mechanisms, which can be inconsistent or incompatible.
My experience has shown that a lack of a unified approach to cross format file password application can lead to vulnerabilities, making it difficult to maintain robust security policies across an organization. It's about finding a balance between strong protection and practical accessibility for authorized users.
Why Cross-Format Encryption Matters
Data breaches are increasingly common, and sensitive information can reside in a multitude of file types. Relying solely on the security of a single application or format is often insufficient. A comprehensive strategy ensures that an attacker cannot simply convert a file to bypass its protection.
Consistent encryption standards across all formats are vital for regulatory compliance and maintaining client trust. It minimizes the attack surface and simplifies the security posture for your organization.
Common File Formats and Their Native Protection
Many popular applications offer built-in encryption features. Microsoft Office documents (Word, Excel, PowerPoint) allow password protection, often using strong AES-256 encryption. PDFs can also be secured with passwords for opening and for restricting permissions like printing or editing.
While these native protections are useful, they often require the recipient to have the same software, and managing passwords for each individual file can become cumbersome. Archiving tools like 7-Zip or WinRAR provide a more universal approach by encrypting entire folders or groups of files into a single, password-protected archive.
Core Principles of Secure File Encryption
At the heart of any effective file encryption strategy lies a set of fundamental principles. Understanding these helps in making informed decisions about which tools and methods to employ, ensuring that your data is genuinely protected from unauthorized access.
It’s not just about turning on a feature; it’s about understanding the underlying mechanisms and choosing wisely to meet specific security requirements. This includes both the technical aspects of encryption and the human element of password creation and management.
Choosing Strong Encryption Algorithms
The strength of your file encryption depends heavily on the underlying algorithm. Modern password encryption standards typically rely on symmetric encryption algorithms like Advanced Encryption Standard (AES) with a key length of 256 bits (AES-256). This is considered highly secure and is widely adopted by governments and security experts.
When selecting software or tools, always verify that they use industry-standard, strong algorithms. Avoid older, weaker algorithms like DES or RC4, which are susceptible to modern attacks.
The Role of Robust Passwords
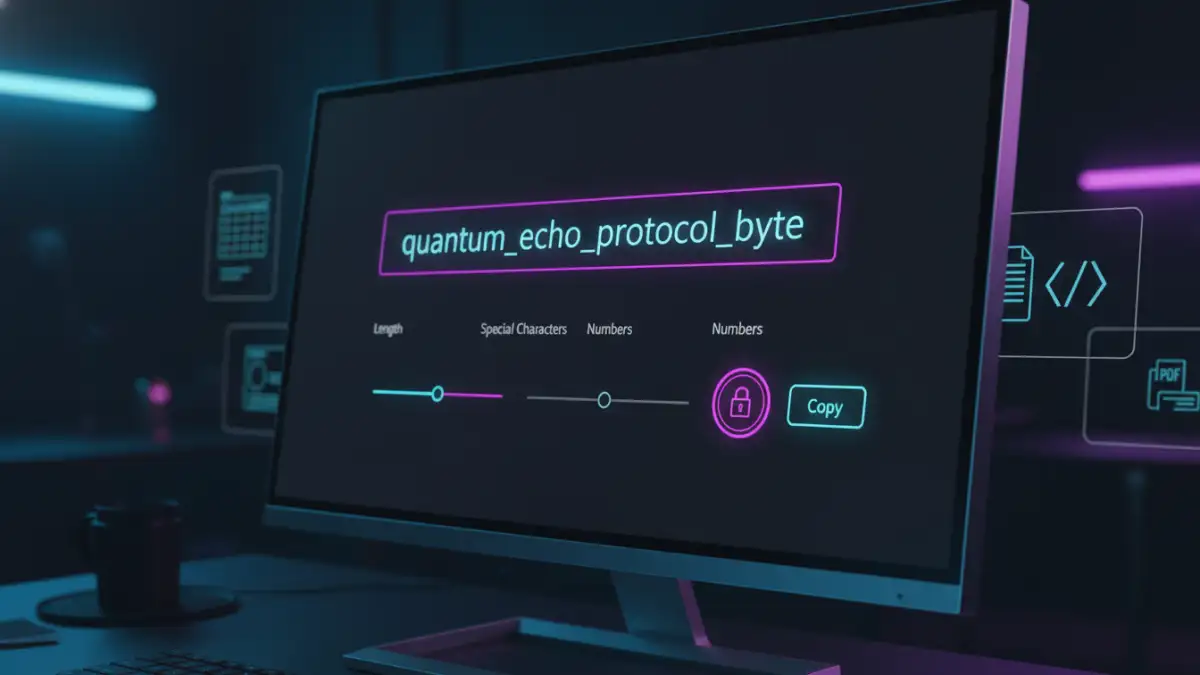
Even the strongest encryption algorithm is useless if the password protecting it is weak. A robust password should be long (ideally 12+ characters), complex (mixing uppercase, lowercase, numbers, and symbols), and unique (never reused).
I always advise clients to use passphrases – a sequence of unrelated words – as they are easier to remember but much harder to guess or brute-force than short, complex passwords. Password managers are indispensable tools for generating and storing these strong, unique credentials.
Practical Methods for Cross-Format Protection
When it comes to putting theory into practice, there are several reliable methods to secure your documents across different formats. The choice often depends on the specific file types, the recipient's capabilities, and your organization's existing infrastructure.
From built-in application features to dedicated encryption software, each approach has its strengths and ideal use cases. My experience has taught me that a layered approach often provides the most comprehensive security.
Leveraging Built-in Application Features
For individual files, using the native encryption features of applications like Microsoft Office or Adobe Acrobat is a straightforward first step. In Microsoft Word or Excel, you can go to File > Info > Protect Document/Workbook > Encrypt with Password. For PDFs, Adobe Acrobat allows you to set open passwords and permission passwords under File > Properties > Security.
While convenient, remember these methods are format-specific. If you need to send a Word document and a PDF to the same person, you'll be managing two separate passwords.
Archiving Tools for Universal Encryption
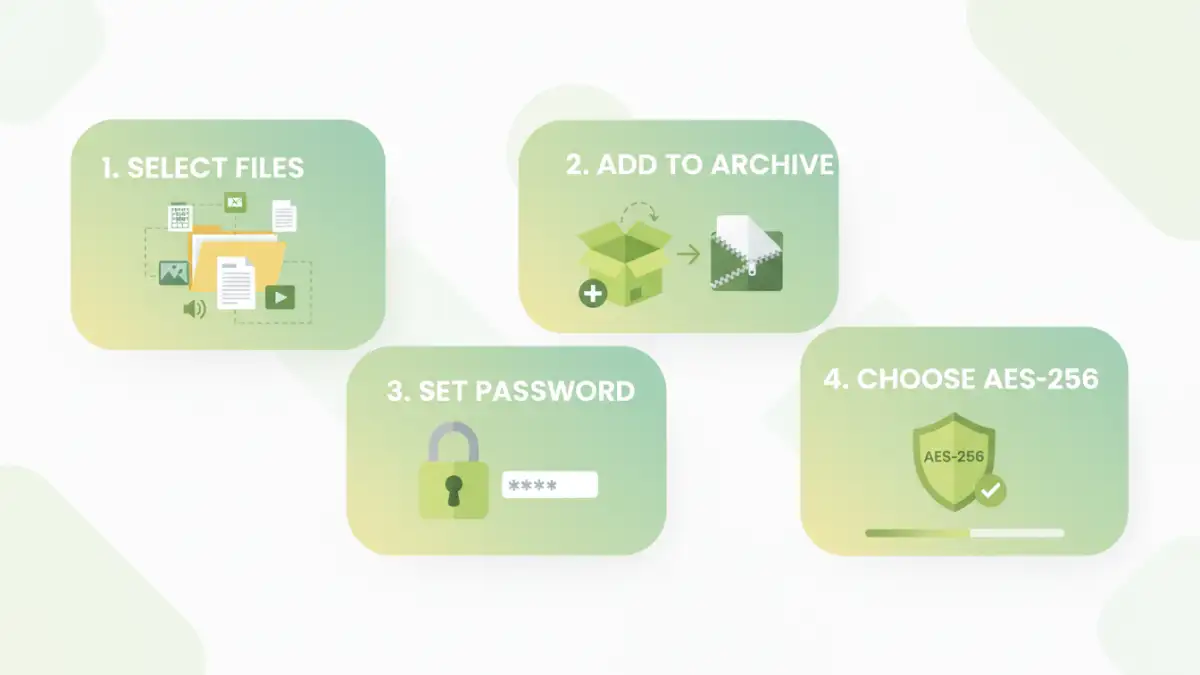
For encrypting multiple files of different formats together, archiving tools like 7-Zip (free and open-source) or WinRAR are excellent. You can compress a folder containing various documents (Word, Excel, PDF, images) into a single ZIP or 7z archive and apply a strong password using AES-256 encryption.
This method simplifies secure file sharing, as the recipient only needs the archive password and a common decompression tool, which is usually built into operating systems or easily downloadable.
Dedicated Document Security Solutions
For enterprise-level secure file sharing and more granular control, dedicated document security solutions often come into play. These tools can apply persistent encryption to documents, regardless of their format, and often include features like rights management, expiry dates, and audit trails.
While these solutions can involve a higher cost and complexity, they provide a robust framework for managing sensitive information across large organizations and diverse workflows.
Implementing Best Practices for Ongoing Security
Encryption is not a one-time task; it's an ongoing commitment to data security. Adopting a set of best practices ensures that your efforts in securing cross format file password protection remain effective and resilient against evolving threats.
From managing the passwords themselves to keeping your systems updated, these practices form the backbone of a strong security posture. I've seen firsthand how neglecting any of these can undermine even the most sophisticated encryption.
Secure Password Management and Sharing
Never share passwords via insecure channels like email or instant messaging. Instead, use a secure password manager that supports encrypted sharing or communicate passwords verbally over a secured line. Implement a policy for regular password rotation and immediate revocation if a password is compromised.
For highly sensitive data, consider out-of-band password delivery, where the password is sent separately from the encrypted file, perhaps through a different communication method or channel.
Regular Audits and Updates
Keep all your operating systems, applications, and encryption tools updated to their latest versions. Software updates often include critical security patches that address newly discovered vulnerabilities. Regularly audit your encrypted files and access logs to ensure compliance and detect any suspicious activity.
Periodically review your encryption policies and practices to ensure they align with current password encryption standards and industry best practices. This proactive approach is crucial in a rapidly changing threat landscape.
Considering Cloud and Collaboration Security
When using cloud storage or collaboration platforms, understand their security features and how they handle encryption. Many platforms offer server-side encryption, but for maximum control, encrypt your files locally before uploading them to the cloud.
Ensure that any shared links are password-protected and time-limited. Educate users on the importance of not sharing direct links to sensitive unencrypted files, even within trusted cloud environments.
Method Comparison: Pros and Cons of Different Approaches
| Method | Key Features | Security Level | Best Use Case |
|---|---|---|---|
| Native App Encryption (e.g., MS Office, Adobe) | Built-in, format-specific, permission controls | High (if using strong password) | Single file, specific format protection |
| Archiving Tools (e.g., 7-Zip, WinRAR) | Multi-file/multi-format, AES-256 encryption, widely compatible | Very High (with strong password) | Bundling multiple files for secure sharing |
| Dedicated Encryption Software | Persistent encryption, rights management, audit trails, policy enforcement | Highest, comprehensive control | Enterprise-level, regulated industries, complex workflows |
| Operating System Encryption (e.g., BitLocker) | Full disk or drive encryption, transparent to user | High (protects data at rest) | Securing entire devices or storage media |