
Working with sensitive business documents means grappling with the ever-present risk of data loss or unauthorized access. When a security incident strikes, the ability to quickly and effectively recover these critical files can be the difference between a minor setback and a catastrophic business disruption. My experience has shown me that proactive planning and swift execution are key to minimizing damage.
The immediate aftermath of a breach can be chaotic. Systems may be compromised, data corrupted, or access outright denied. In such scenarios, having a well-defined strategy for secure document recovery isn't just good practice; it's a business imperative. This guide will walk you through the essential steps and considerations for restoring your sensitive business documents.
Table of Contents
Understanding the Breach Impact
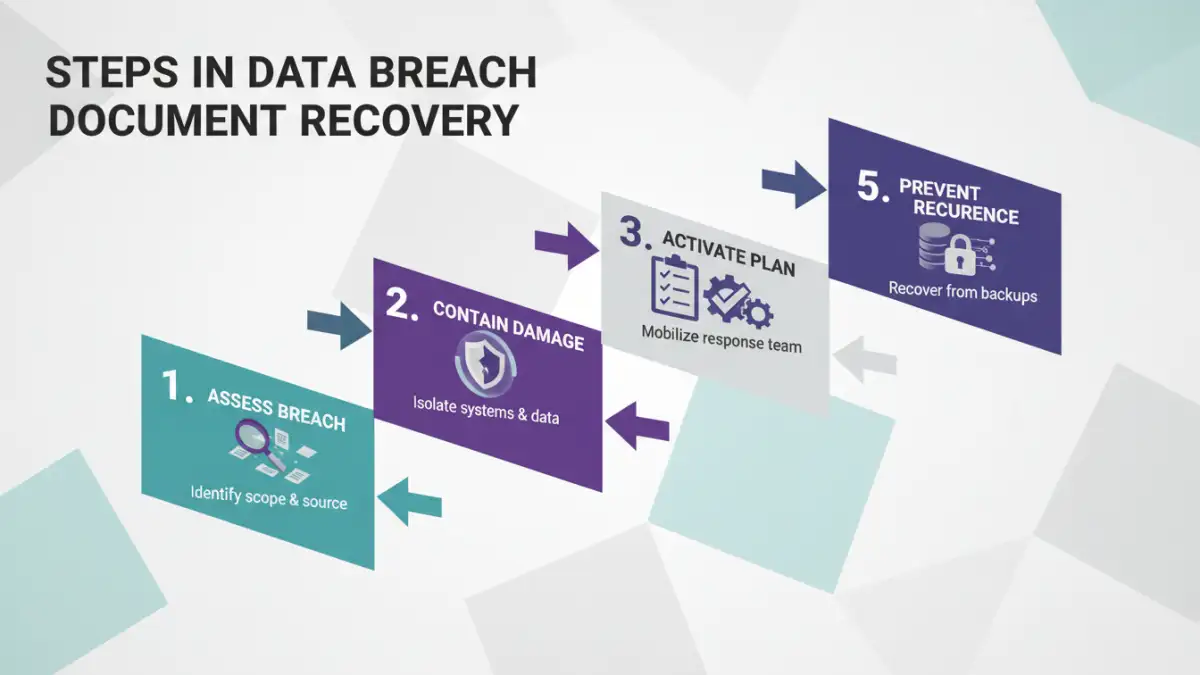
The first step in any recovery effort is to accurately assess the scope and nature of the data breach. Was it a ransomware attack locking files, a phishing incident leading to unauthorized access, or a system failure causing data corruption? Understanding the 'how' and 'what' of the breach dictates the 'how' of the recovery. This assessment helps prioritize which documents are most critical and how they were affected.
Assessing Data Compromise
Identifying precisely which documents and data sets were accessed, altered, or deleted is paramount. This involves log analysis, system scans, and potentially forensic investigations. Knowing the extent of the compromise informs the urgency and specific methods required for restoration.
Immediate Response Steps
Once a breach is detected, immediate action is crucial to contain the damage and begin the recovery process. This phase focuses on isolating affected systems, preventing further data loss, and securing the environment.
Containment and Isolation
The priority is to stop the bleeding. This often means disconnecting affected servers or workstations from the network. It's also vital to preserve any evidence that might be useful for forensic analysis or legal proceedings. Quick containment can limit the spread of malware or unauthorized access.
Activating the Incident Response Plan
If your organization has an incident response plan, now is the time to activate it. This plan should outline roles, responsibilities, communication protocols, and step-by-step procedures for various breach scenarios. Without a plan, response efforts can be ad-hoc and inefficient, costing valuable time and resources.
Effective Recovery Strategies
With the immediate threat contained, the focus shifts to restoring lost or compromised documents. The chosen strategy will depend heavily on your backup and security infrastructure.
Leveraging Backups
Regular, verified backups are the cornerstone of any effective data breach document recovery effort. Whether using cloud-based solutions, local network attached storage (NAS), or offsite tape backups, restoring from a clean, recent backup is often the fastest route to recovery. It's crucial to ensure the backup itself hasn't been compromised.
Utilizing Forensic Tools
In cases of data deletion or corruption where backups are insufficient or also affected, specialized data recovery software and forensic tools may be necessary. These tools can sometimes retrieve deleted files or reconstruct fragmented data, though success is not guaranteed and often requires expertise. This is where post breach data restoration becomes a technical challenge.
Engaging Third-Party Experts
For complex breaches or when internal resources are insufficient, engaging cybersecurity and data recovery specialists is a wise decision. These experts have the tools, knowledge, and experience to handle sophisticated attacks and complex post breach data restoration scenarios, ensuring a more thorough and secure recovery.
Prevention and Best Practices
While recovering from a breach is critical, preventing future incidents is equally important. Implementing robust enterprise file security measures can significantly reduce the risk and impact of future breaches.
Regular Audits and Monitoring
Continuously monitoring systems for suspicious activity and conducting regular security audits can help detect threats early. This proactive approach allows for intervention before a breach escalates into a major incident.
Employee Training and Awareness
Human error remains a leading cause of data breaches. Comprehensive and ongoing training for employees on recognizing phishing attempts, practicing good password hygiene, and understanding data security policies is essential. A well-informed workforce is your first line of defense.
Implementing Strong Access Controls
Enforcing the principle of least privilege ensures that employees only have access to the data and systems necessary for their job functions. Multi-factor authentication (MFA) adds another critical layer of security, making it much harder for unauthorized individuals to gain access even if credentials are compromised.
Secure Document Recovery Methods Comparison
| Method | Description | Pros | Cons | When to Use |
|---|---|---|---|---|
| Backup Restoration | Restoring files from pre-defined backup sets. | Fast, reliable if backups are current and uncompromised. | Requires consistent backup strategy; backups can be lost or corrupted. | Most common and effective method for data loss or corruption. |
| Data Recovery Software | Using specialized tools to recover deleted or corrupted files. | Can retrieve data not present in backups. | Success not guaranteed; requires technical skill; can be time-consuming. | When backups are unavailable or insufficient. |
| Forensic Investigation | In-depth analysis to retrieve and reconstruct data from compromised systems. | Can recover highly damaged or fragmented data; provides breach insights. | Expensive, requires expert knowledge, time-intensive. | Complex breaches, ransomware, or when data integrity is severely compromised. |
| Third-Party Specialists | Engaging external cybersecurity and data recovery experts. | Access to advanced tools and expertise; efficient handling of complex incidents. | Can be costly; requires trust and due diligence in selection. | Large-scale breaches, critical data loss, or when internal resources are limited. |