
When handling sensitive client information, intellectual property, or financial data, ensuring its security is paramount. I've seen firsthand how a single data breach can have devastating consequences for a company's reputation and bottom line. This is where robust document encryption comes into play, acting as a critical line of defense. However, navigating the landscape of encryption can be complex, especially with varying regulations and evolving threats.
Understanding and adhering to global standards for document encryption in business isn't just about compliance; it's about building trust and safeguarding your organization's future. These standards provide a framework for implementing effective security measures, ensuring that your digital assets remain confidential and intact, regardless of where they are stored or transmitted.
Table of Contents
Understanding the Basics of Document Encryption
At its core, document encryption is the process of converting readable data into an unreadable format, known as ciphertext, using an algorithm and a key. Only authorized individuals with the correct decryption key can convert the ciphertext back into its original, readable form. This process is fundamental to maintaining confidentiality and integrity of sensitive business information.
The Role of Encryption Keys
Encryption keys are the secret pieces of information used to encrypt and decrypt data. The strength and security of the encryption depend heavily on the complexity and secrecy of these keys. For business applications, using strong, randomly generated keys and managing them securely is a critical aspect of effective data protection.
Key International Security Standards

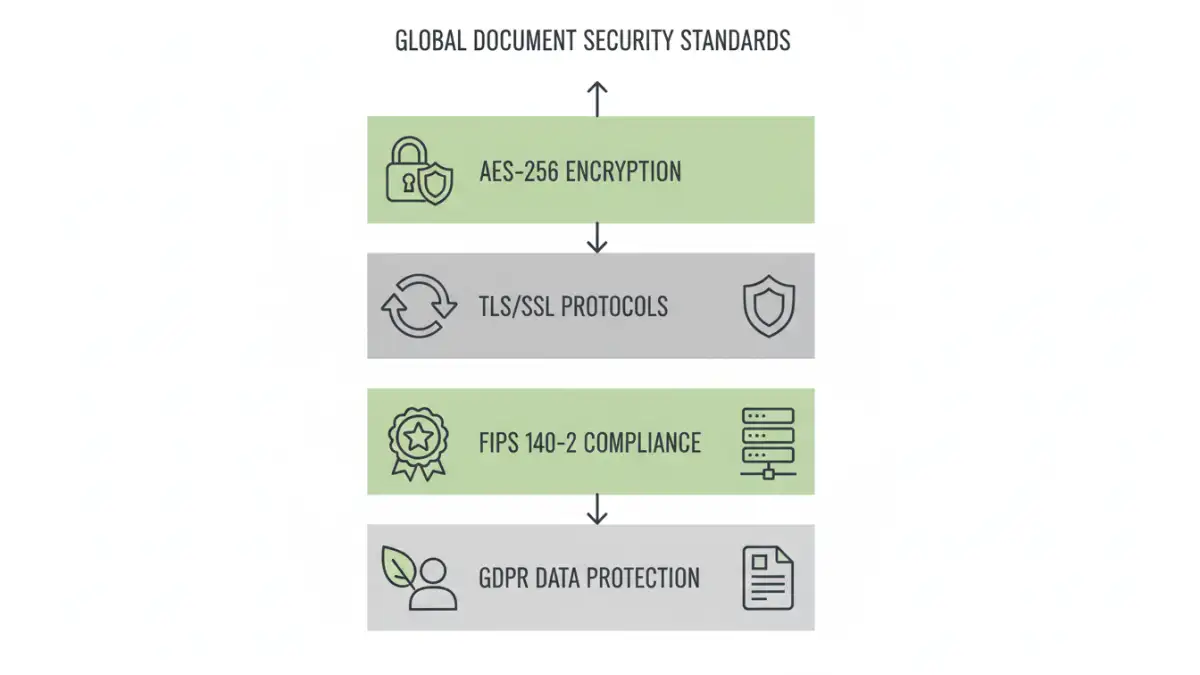
Several international standards and regulations guide how businesses should approach document encryption. Adhering to these frameworks helps ensure a baseline level of security and compliance across different jurisdictions. These standards are often developed by reputable organizations dedicated to information security.
AES (Advanced Encryption Standard)
AES is a symmetric encryption algorithm that has become the de facto standard for encrypting sensitive data worldwide. It is widely adopted by governments and industries for its robust security and efficiency. AES supports key sizes of 128, 192, and 256 bits, with 256-bit being the most secure.
TLS/SSL (Transport Layer Security/Secure Sockets Layer)
While not directly for document encryption at rest, TLS/SSL is crucial for securing data in transit. When documents are sent via email or uploaded to cloud services, TLS/SSL ensures that the connection is encrypted, preventing eavesdropping. This is a vital component of overall secure file management.
Other Relevant Standards
Other standards like FIPS 140-2 (Federal Information Processing Standards) provide security requirements for cryptographic modules used by U.S. federal agencies, but are often adopted globally as a benchmark. GDPR (General Data Protection Regulation) and CCPA (California Consumer Privacy Act) also mandate strong data protection measures, including encryption, for personal data.
Implementation Strategies for Corporate Data Protection
Implementing effective document encryption requires a strategic approach that considers various aspects of corporate data protection. It's not just about encrypting files; it's about integrating security into daily workflows and policies. This involves choosing the right tools and methods that align with business needs and regulatory requirements.
End-to-End Encryption
End-to-end encryption ensures that data is encrypted from the moment it's created to the moment it's accessed by the intended recipient. This means that even the service provider cannot decrypt the data. This is particularly important for highly sensitive communications and collaborations.
Key Management Practices
Securely managing encryption keys is as important as the encryption itself. This includes generating strong keys, storing them safely (often in hardware security modules or dedicated key management systems), and defining clear access policies. Poor key management can render even the strongest encryption useless.
Encryption Best Practices for Secure File Management
To maximize the effectiveness of document encryption in business, adopting several best practices is essential. These practices help create a comprehensive security posture for your organization's digital assets.
Regular Audits and Updates
Encryption algorithms and protocols evolve. Regularly auditing your encryption methods and updating software to the latest secure versions is crucial to stay ahead of potential vulnerabilities. This also applies to reviewing access logs and key management policies.
Employee Training
Human error remains a significant factor in security incidents. Educating employees on the importance of encryption, secure password practices, and how to use encrypted tools correctly is vital. Training should cover phishing awareness and secure handling of sensitive documents.
Data Classification
Not all data requires the same level of security. Implementing a data classification policy helps identify sensitive information and apply appropriate encryption measures. This ensures that resources are focused on protecting the most critical assets.
Comparison Table: Encryption Methods for Business Documents
| Method | Description | Security Level | Use Case | Pros | Cons |
|---|---|---|---|---|---|
| Built-in OS Encryption (e.g., BitLocker, FileVault) | Full-disk or file-level encryption provided by operating systems. | High (when implemented correctly) | Securing entire drives or specific files on company devices. | Convenient, often already available. | Can be complex to manage across an organization; relies on OS security. |
| Third-Party Encryption Software | Dedicated applications offering advanced encryption features for files and folders. | Very High | Protecting sensitive documents, large volumes of data, or when specific compliance is needed. | Feature-rich, robust security, often cross-platform. | Can incur costs, requires installation and management. |
| Cloud Service Encryption (e.g., AES-256 at rest) | Encryption managed by cloud providers for data stored on their servers. | High (provider dependent) | Securing data stored in cloud storage solutions. | Seamless integration, managed by provider. | Reliance on provider's security practices; potential access concerns. |
| End-to-End Encrypted Messaging/Sharing Platforms | Data encrypted from sender to receiver, inaccessible by the platform itself. | Extremely High | Securely sharing sensitive documents and communications. | Maximum confidentiality, protects against platform breaches. | Limited file size or features; requires compatible platforms. |