I've spent a good part of my career dealing with digital assets, and one recurring headache is the migration of historical archives. It’s not just about converting files; it’s about making sure that what goes in, comes out exactly as intended, without a single bit of data loss or corruption.
The challenge isn't merely about changing a file extension; it’s about maintaining the authenticity, reliability, and usability of the information. Losing metadata, embedded objects, or even subtle formatting can render an entire archive less valuable, or worse, unusable.
Table of Contents
Understanding the Challenge in Archive Format Conversion
Migrating documents from one archive format to another often introduces a myriad of complexities. We're not just talking about simple text files; these archives frequently contain complex documents like CAD drawings, legacy office suites, or specialized scientific data, each with its unique internal structure and dependencies.
The core problem lies in the inherent differences between formats. A seemingly straightforward conversion can strip away critical metadata, alter embedded objects, or even fundamentally change the rendering of the document, making the original intent difficult to ascertain.
Common Complexities and Pitfalls
One of the most insidious pitfalls is the silent loss of metadata. This isn't just creation dates; it includes author information, revision history, digital signatures, and even internal linking structures that are vital for the document's context and provenance.
Another significant challenge arises with embedded content – think spreadsheets within Word documents, or images linked rather than embedded. Different conversion engines handle these elements disparately, sometimes breaking links or converting them into static, uneditable images, thereby compromising the document integrity preservation.
Core Principles for File Format Integrity
Before even touching a conversion tool, it's crucial to establish a set of guiding principles. These aren't just technical steps, but philosophical commitments to maintaining the authenticity and reliability of your digital assets throughout their lifecycle.
A robust strategy for archive conversion security starts with a clear understanding of what constitutes 'integrity' for your specific document types. This might mean byte-for-byte fidelity, or it could mean visual and logical equivalence, depending on the archive's purpose.
Pre-Conversion Validation and Assessment
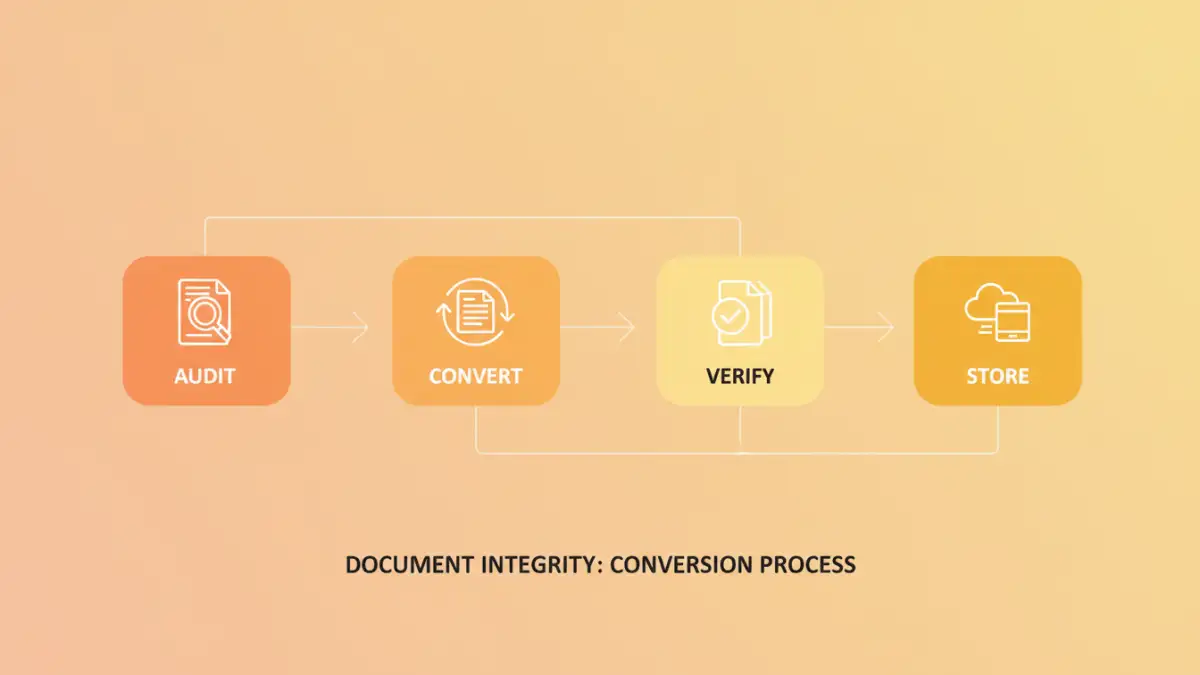
My first step in any major archive conversion project is always a thorough pre-validation. This involves auditing the source files, understanding their internal structure, and identifying any proprietary elements or known issues that might complicate the conversion process.
Creating a detailed inventory and risk assessment helps flag documents that might require special handling or specific conversion pathways. This proactive approach significantly reduces the chances of unexpected data loss or corruption down the line.
Metadata and Structural Preservation
Preserving metadata is non-negotiable. This contextual data provides crucial information about the document's origin, history, and relationships to other files. Losing it is akin to ripping pages out of a library catalog.
Beyond simple metadata, the internal structure of complex documents, such as bookmarks, hyperlinks, and table of contents, must also be preserved. These elements define the document's navigability and usability, and their loss severely impacts its overall utility.
Practical Approaches to Document Integrity Preservation
With the principles in place, we can now look at the practical methods for executing secure conversions. The choice of tools and techniques often depends on the volume, complexity, and sensitivity of the documents being processed.
It's rarely a one-size-fits-all solution; sometimes a combination of commercial software and custom scripting provides the most reliable outcome for maintaining file format integrity.
Leveraging Specialized Conversion Tools
For large-scale or highly complex archives, specialized commercial conversion software is often indispensable. Tools designed specifically for archival migration often have robust error handling, detailed logging, and the ability to process proprietary formats that generic converters cannot.
When evaluating such tools, I always look for features like batch processing capabilities, comprehensive metadata transfer options, and detailed reports on conversion success and any encountered anomalies. Open-source alternatives can also be powerful, but often require more technical expertise to configure correctly.
Scripting and Automation for Consistency
For repetitive tasks or when dealing with highly specific requirements, scripting offers unparalleled control. Languages like Python or PowerShell can be used to automate conversion workflows, apply consistent naming conventions, and even inject missing metadata programmatically.
Automation also allows for the integration of checksum verification at various stages of the process. Calculating MD5 or SHA-256 hashes before and after conversion provides a byte-level assurance that no data has been inadvertently altered or lost, which is critical for secure document handling.
Verifying Integrity Post-Conversion
The conversion process isn't complete until you've thoroughly verified the integrity of the newly formatted documents. This step is as critical as the conversion itself, as it confirms that your efforts to preserve document integrity preservation have been successful.
Blindly trusting a conversion tool's 'success' message is a rookie mistake; real verification requires systematic checks and, ideally, human oversight for a sample set.
Checksum Validation and Content Comparison
Checksums (like MD5, SHA-1, SHA-256) are your best friends here. By generating a cryptographic hash of the original and converted files, you can quickly determine if any byte-level changes have occurred. Any mismatch indicates a potential problem that needs investigation.
Beyond byte-level checks, visual inspection of a representative sample is crucial. For complex documents, automated content comparison tools can highlight differences in text, formatting, and embedded objects, providing a more granular validation of file format integrity.
Establishing Best Practices for Secure Document Handling
Beyond the technical steps, a robust framework for secure document handling during archive format conversion requires organizational commitment and clear policies. It's about creating an environment where integrity is prioritized at every stage.
This includes defining clear roles and responsibilities, providing adequate training for personnel involved in the conversion process, and establishing a continuous review cycle for your conversion methodologies.
Policy Development and Staff Training
Developing clear, documented policies for archive conversion is paramount. These policies should outline acceptable formats, required integrity checks, error handling procedures, and storage protocols for both original and converted files.
Equally important is investing in staff training. Even the most sophisticated tools are only as good as the people operating them. Ensuring your team understands the nuances of document integrity preservation and the tools at their disposal minimizes human error.
Version Control and Audit Trails
Implementing robust version control for converted documents is essential. This means not only tracking changes but also maintaining clear audit trails of who converted what, when, and using which parameters. Retaining the original archive in its native format, perhaps in a read-only state, is also a critical fallback.
A comprehensive audit trail provides transparency and accountability, allowing you to trace back any discrepancies and understand the full history of a document's transformation, reinforcing its overall archive conversion security.
Comparison Table
| Strategy | Primary Goal | Pros | Cons | Best For |
|---|---|---|---|---|
| Manual Conversion | Precise control | High fidelity for unique cases, deep inspection | Time-consuming, prone to human error, not scalable | Small, highly sensitive archives with unique formats |
| Automated Scripting | Consistency & efficiency | Customizable, scalable, good for specific workflows | Requires coding expertise, setup time, maintenance | Batch processing for structured, similar documents |
| Specialized Software | Robustness & features | Handles complex formats, batch processing, reporting | Costly, learning curve, vendor lock-in risk | Large-scale, diverse, and proprietary format archives |
| Cloud-Based Services | Ease of use & accessibility | Convenient, often quick, minimal infrastructure needed | Privacy concerns, limited customization, dependency on service | Non-sensitive documents, quick format changes |