
When dealing with sensitive information, ensuring its protection is paramount. Whether it's client data, proprietary business plans, or personal records, unauthorized access can lead to severe consequences. This is where understanding and implementing key compliance frameworks becomes not just a best practice, but a necessity.
My experience has shown me that many organizations struggle to balance accessibility with robust security. The good news is that by leveraging established data protection frameworks, you can create a secure environment for your documents while meeting legal and ethical obligations.
Table of Contents
Understanding the Importance of Compliance
In today's digital landscape, data breaches are a constant threat. Compliance frameworks provide a structured approach to managing and protecting sensitive information, helping organizations avoid hefty fines, reputational damage, and loss of customer trust. They offer a roadmap for building a strong security posture.
Adhering to these frameworks ensures that your organization handles data responsibly. This not only protects your assets but also builds confidence with clients and partners who entrust you with their information. It’s about proactive risk management.
Why Document Security Matters
Documents often contain the most critical and sensitive pieces of information an organization possesses. From financial records and employee details to intellectual property and customer databases, the compromise of these documents can have devastating effects. Implementing strong security measures is crucial for maintaining business continuity and integrity.
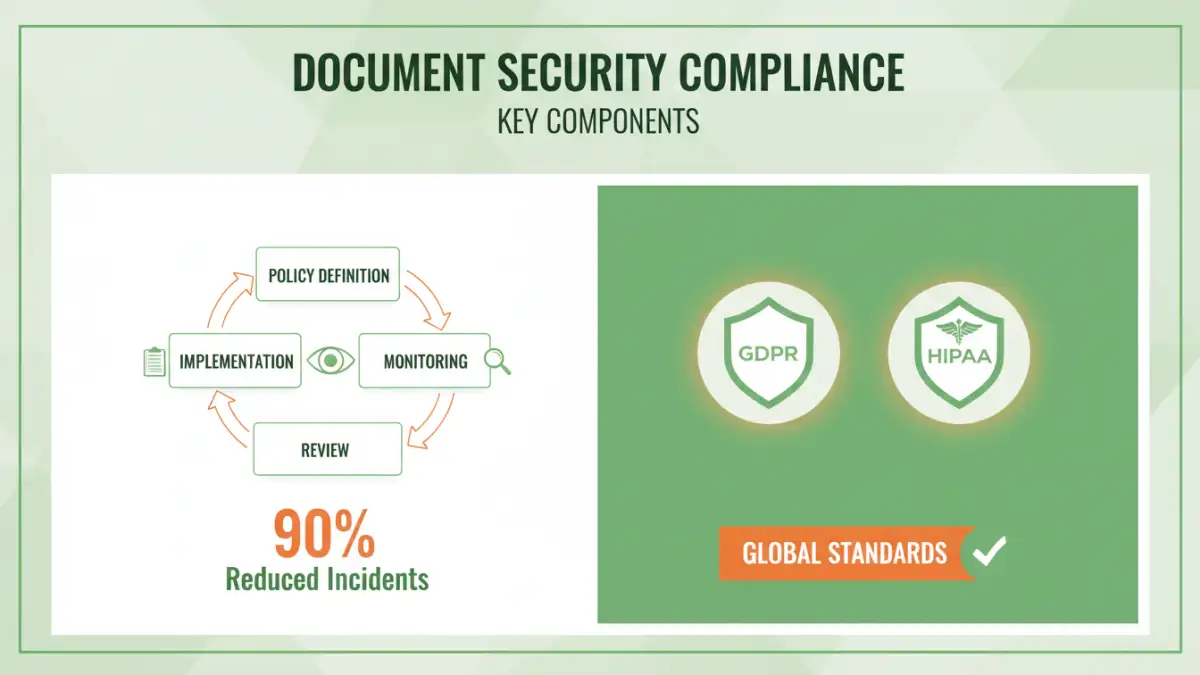
Key Compliance Frameworks Explained

Several prominent frameworks guide organizations in securing their data. Understanding these will help you tailor your security strategy effectively. Each framework addresses different aspects of data protection and privacy.
GDPR Document Handling
The General Data Protection Regulation (GDPR) is a comprehensive data privacy law in the European Union. For document security, it mandates strict controls over how personal data is collected, processed, stored, and deleted. This includes requirements for consent, data minimization, and the right to erasure, all of which impact document management policies.
HIPAA File Security
The Health Insurance Portability and Accountability Act (HIPAA) sets standards for protecting sensitive patient health information in the United States. HIPAA file security requires covered entities to implement administrative, physical, and technical safeguards to ensure the confidentiality, integrity, and availability of electronic protected health information (ePHI).
Other Data Protection Frameworks
Beyond GDPR and HIPAA, numerous other data protection frameworks exist globally, such as CCPA (California Consumer Privacy Act), ISO 27001 (Information Security Management), and SOC 2 (Service Organization Control 2). These frameworks often overlap in their objectives but may have specific requirements tailored to different industries or regions. A comprehensive secure document management strategy often incorporates elements from multiple frameworks.
Implementing Security Measures
Putting compliance into practice involves a multi-faceted approach. It’s not just about technology; it's also about policies, procedures, and people. A layered security strategy is the most effective way to protect your documents.
This includes implementing access controls, data encryption, regular backups, and secure disposal methods. Training employees on data handling policies is also a critical component of a robust security program.
Access Control and Permissions
One of the most fundamental aspects of document security is controlling who can access what. Implementing role-based access control (RBAC) ensures that users only have permissions to view, edit, or delete documents relevant to their job function. This principle of least privilege minimizes the risk of accidental or malicious data exposure.
Encryption and Data Masking
Encryption transforms data into an unreadable format, making it unintelligible to anyone without the decryption key. This is vital for data both in transit (e.g., email attachments, cloud uploads) and at rest (e.g., on servers, laptops). Data masking, on the other hand, involves obscuring sensitive data with altered, fictitious data for testing or development purposes, further protecting its integrity.
Ongoing Document Security Management
Document security is not a one-time setup; it requires continuous attention and adaptation. As threats evolve and regulations change, your security measures must evolve with them.
Regular audits, vulnerability assessments, and employee training are essential to maintaining a strong security posture. Staying informed about emerging threats and best practices is key to proactive defense.
Regular Audits and Monitoring
Periodically auditing your access logs, security policies, and overall data handling procedures helps identify potential weaknesses. Monitoring systems for suspicious activity can alert you to attempted breaches or policy violations in real-time, allowing for swift intervention.
Secure Document Disposal
When documents are no longer needed, they must be disposed of securely. This means more than just deleting files. For digital documents, secure deletion or overwriting methods are necessary. For physical documents, shredding or pulping is essential to prevent information recovery.
Best Practices for Secure Document Handling
Beyond specific frameworks, adopting general best practices can significantly enhance your document security. These practices create a culture of security within your organization.
This includes using strong, unique passwords, enabling multi-factor authentication, and educating employees about phishing and social engineering tactics. Regularly updating software and security protocols is also crucial.
Real-world Scenario: A small consulting firm I worked with was struggling with GDPR compliance. They had client contracts and financial data scattered across various unencrypted cloud storage services. We implemented a policy requiring all sensitive documents to be stored in an encrypted, access-controlled cloud platform, with clear guidelines on data retention and disposal. This significantly reduced their compliance risk and improved client trust.
Comparison Table: Document Security Measures
| Measure | Description | Pros | Cons | Framework Relevance |
|---|---|---|---|---|
| Access Control | Restricting user access based on roles | Minimizes unauthorized access, principle of least privilege | Requires careful configuration and ongoing management | GDPR, HIPAA, ISO 27001 |
| Data Encryption | Scrambling data into unreadable format | Protects data at rest and in transit | Can impact performance, requires key management | GDPR, HIPAA, ISO 27001 |
| Secure Disposal | Methods for permanently deleting data | Prevents data leakage from old documents | Requires specific tools/processes, can be time-consuming | GDPR, HIPAA |
| Regular Audits | Reviewing security logs and policies | Identifies vulnerabilities and policy adherence | Time-intensive, requires expertise | ISO 27001, SOC 2 |
| Employee Training | Educating staff on security protocols | Reduces human error, builds security culture | Requires consistent effort, can be overlooked | GDPR, HIPAA, ISO 27001 |