
Working with sensitive structured files, whether they're customer databases, financial records, or proprietary research, demands a rigorous approach to security. Ensuring that these files adhere to various regulations isn't just a technical challenge; it's a critical business imperative that protects both your organization and your stakeholders. My experience has shown that a proactive stance on document security compliance can prevent costly breaches and build essential trust.
The landscape of data protection is constantly evolving, with new threats emerging and regulatory frameworks becoming more stringent. For organizations handling structured data, this means that simply encrypting a file is often not enough. A holistic strategy is needed, one that addresses access controls, auditing, data integrity, and long-term retention policies. This article aims to provide a clear roadmap for achieving and maintaining robust document security compliance.
Table of Contents
Understanding the Need for Document Security Compliance
In today's interconnected world, the sheer volume of structured data generated and stored by businesses is immense. This data often contains personally identifiable information (PII), financial details, intellectual property, and other sensitive categories. Failure to protect this data can lead to severe consequences, including hefty fines, legal liabilities, reputational damage, and loss of customer trust. Understanding the specific structured data regulations that apply to your industry and region is the first crucial step.
Regulatory Landscape
Different industries face unique regulatory requirements. For instance, healthcare organizations must comply with HIPAA, financial institutions with GLBA and SOX, and companies handling EU citizen data with GDPR. These regulations often dictate specific security controls, data handling procedures, and breach notification protocols. Staying informed about these evolving structured data regulations is an ongoing process.
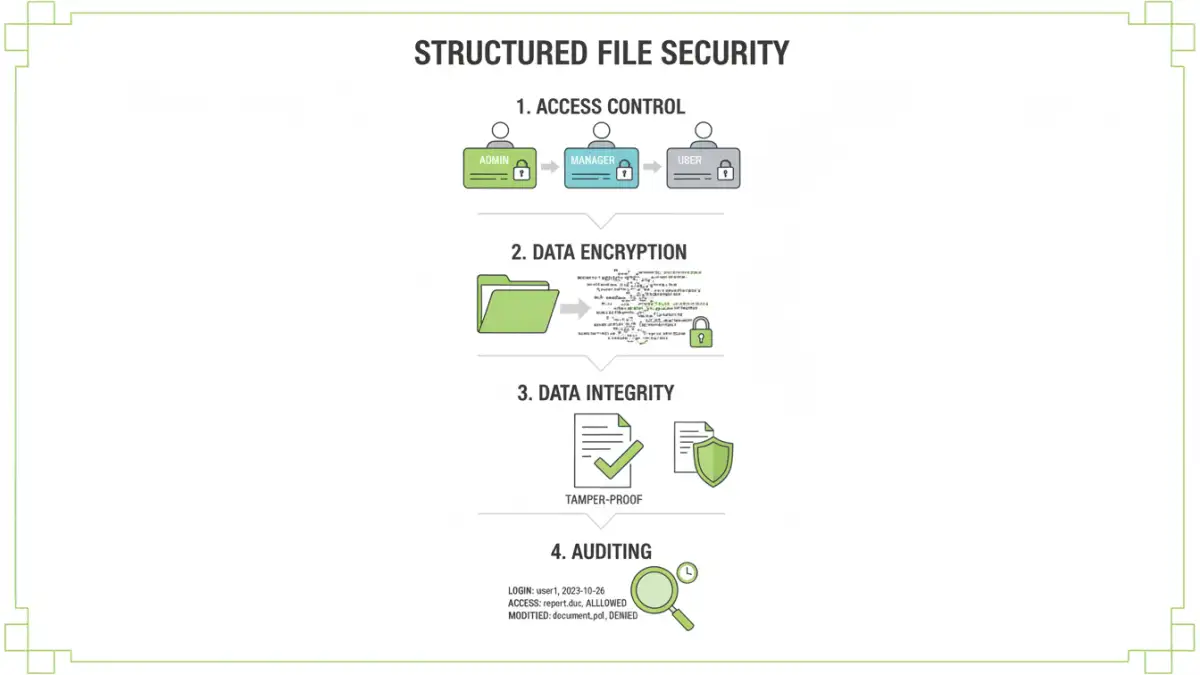
Key Principles of Structured File Security
Achieving effective document security compliance relies on several core principles. These aren't just about technology; they involve people, processes, and policies working in harmony. A robust security posture is built on a foundation of these fundamental elements, ensuring that data is protected comprehensively.
Access Control and Authentication
The principle of least privilege is paramount. Users should only have access to the data and systems necessary for their job functions. Implementing strong authentication methods, such as multi-factor authentication (MFA), ensures that only authorized individuals can access sensitive files. Role-based access control (RBAC) is a common and effective way to manage these permissions systematically.
Data Encryption
Encryption is a cornerstone of data protection. Structured files containing sensitive information should be encrypted both at rest (when stored) and in transit (when being transferred). Choosing strong, industry-standard encryption algorithms (like AES-256) is vital. Key management also becomes critical; securely storing and managing encryption keys prevents unauthorized decryption.
Data Integrity and Non-Repudiation
Ensuring data integrity means guaranteeing that data has not been altered or corrupted. Hashing algorithms and digital signatures can verify that a file's content remains unchanged. Non-repudiation ensures that actions taken by a user can be traced back to them, preventing them from denying their actions, which is crucial for auditing and accountability.
Implementing Security Measures
Translating these principles into practice requires a strategic implementation plan. This involves selecting appropriate tools and technologies, configuring them correctly, and integrating them into existing workflows. Often, a layered security approach offers the best protection against diverse threats.
Using Secure File Transfer Protocols
When transferring structured files, especially across networks or to external parties, using secure protocols is non-negotiable. SFTP (SSH File Transfer Protocol) and FTPS (FTP Secure) provide encrypted channels for data transfer, protecting it from eavesdropping. For cloud-based storage, ensure that the service provider uses robust encryption for data in transit.
Leveraging Database Security Features
Many databases offer built-in security features that are essential for protecting structured data. This includes granular access controls at the table or row level, data masking for sensitive fields, and audit logging. Regularly reviewing and updating database security configurations is crucial, especially as new vulnerabilities are discovered.
Implementing Access Control Policies
Beyond technical controls, clear policies on data access are vital. These policies should define who can access what data, under what circumstances, and for how long. Regular training for employees on these policies and the importance of data governance helps reinforce good security habits.
Auditing and Monitoring for Compliance
Effective document security compliance isn't a one-time setup; it requires continuous monitoring and auditing. Regular checks ensure that security measures remain effective and that no unauthorized access or modifications have occurred. This proactive approach is key to identifying and mitigating risks before they escalate.
Log Management and Analysis
Comprehensive logging of all access and modification activities related to structured files is essential. This includes who accessed a file, when, what changes were made, and from where. Centralized log management systems and security information and event management (SIEM) tools can help aggregate, analyze, and alert on suspicious activities. Reviewing these logs regularly is a critical part of data governance.
Regular Security Audits
Conducting periodic security audits, both internal and external, helps validate the effectiveness of your security controls. These audits should assess compliance with relevant regulations and internal policies. Findings from audits should be documented, and remediation plans should be put in place to address any identified gaps or vulnerabilities.
Best Practices for Long-Term Success
Maintaining document security compliance is an ongoing journey. Adopting a set of best practices ensures that your security posture remains strong and adaptable to changing threats and regulations. It fosters a culture of security within the organization, making everyone a responsible stakeholder.
Employee Training and Awareness
The human element is often the weakest link in security. Regular, comprehensive training on security policies, threat awareness (like phishing), and proper data handling procedures is crucial for all employees. This reinforces the importance of file compliance and encourages vigilance.
Data Minimization and Retention Policies
Only collect and retain the data that is absolutely necessary. Implementing strict data minimization policies reduces the attack surface and simplifies compliance efforts. Similarly, clear data retention policies ensure that old, unnecessary data is securely disposed of, reducing potential liabilities.
Incident Response Planning
Despite best efforts, security incidents can occur. Having a well-defined incident response plan is critical for minimizing damage. This plan should outline steps for detection, containment, eradication, recovery, and post-incident analysis. Regular testing of the incident response plan ensures its effectiveness.
Comparison Table: Security Measures for Structured Files
| Security Measure | Description | Pros | Cons | Relevance to File Compliance |
|---|---|---|---|---|
| Access Control (RBAC) | Assigning permissions based on user roles. | Granular control, reduces human error. | Can be complex to manage initially. | Essential for limiting access to sensitive structured data. |
| Data Encryption (AES-256) | Scrambling data so it's unreadable without a key. | Protects data at rest and in transit. | Requires secure key management. | Mandatory for many regulations regarding sensitive structured data. |
| Secure File Transfer (SFTP/FTPS) | Using encrypted protocols for data transmission. | Protects data during transfer. | Requires compatible client/server software. | Crucial for secure exchange of structured data with partners. |
| Audit Logging | Recording all access and modification events. | Provides accountability, aids investigation. | Can generate large volumes of data. | Critical for demonstrating compliance and detecting breaches. |
| Data Masking | Obscuring sensitive data fields. | Protects PII in non-production environments. | May impact data analysis if not implemented carefully. | Helps meet privacy requirements for structured data. |