
The scenario is all too common in the fast-paced world of startups: a critical file, locked down with robust encryption, suddenly becomes inaccessible. This isn't just a technical glitch; it's a potential business disaster. Imagine months of work, sensitive client data, or crucial financial reports suddenly out of reach. This was the reality facing a burgeoning tech startup I recently assisted.
They had implemented strong security measures, including encrypting all their sensitive documents. However, a combination of a failed hard drive and an unfortunately forgotten password to the encryption key presented a daunting challenge. The pressure was immense, as their operational continuity hinged on regaining access to these files. This situation underscores the dual nature of encryption: a powerful shield, but one that requires diligent management to prevent it from becoming a barrier.
Table of Contents
The Unforeseen Challenge
This particular startup dealt with sensitive intellectual property and client contracts. To safeguard this information, they employed industry-standard file encryption software, adding an extra layer of security to their digital assets. The encryption itself was sound, designed to be virtually impenetrable without the correct decryption key or password.
The crisis began when a primary workstation experienced a catastrophic hardware failure, corrupting the local storage. Compounding the issue, the individual responsible for managing the master encryption keys had recently departed the company, and their access credentials had been deactivated without a proper handover of the decryption protocols. This left the team in a bind, facing a significant data loss event.
Understanding the Risk
The immediate concern was the potential for prolonged downtime and reputational damage. Losing access to these encrypted documents meant they couldn't fulfill client obligations or continue development on key projects. The perceived impossibility of encrypted document recovery loomed large, creating significant stress for the team.
Initial Attempts and Roadblocks

Understandably, the team first tried the most straightforward approaches. They attempted to use the last known password combinations, brute-force attempts with common password patterns, and even tried to access older backups, assuming they might contain unencrypted versions. Unfortunately, the encryption was robust, and the password management practices were not as rigorous as they should have been.
Each failed attempt amplified the urgency. They realized that this wasn't a problem solvable with standard IT troubleshooting. The nature of the encryption meant that incorrect guesses could potentially lock the files permanently or corrupt the data further. This is where the need for specialized expertise in data recovery case study scenarios became apparent.
Specialized Solutions for Encrypted File Access
Recognizing the limitations of their internal capabilities, the startup sought external help. This is often a critical step in business file restoration when dealing with encrypted data. Engaging with a specialized data recovery service that had a proven track record with encrypted file access was paramount.
These services employ advanced techniques and proprietary tools. They often have extensive databases of common encryption algorithms and vulnerabilities, as well as sophisticated methods for password recovery or data reconstruction. Their approach moves beyond simple password guessing into more complex forensic analysis and decryption protocols.
Evaluating Recovery Options
The recovery specialists first assessed the type of encryption used and the extent of the data corruption. They explained that different encryption methods (like AES-256, BitLocker, VeraCrypt, or proprietary software) require different recovery strategies. Understanding the specific software and its implementation was the first hurdle.
The Recovery Process in Action
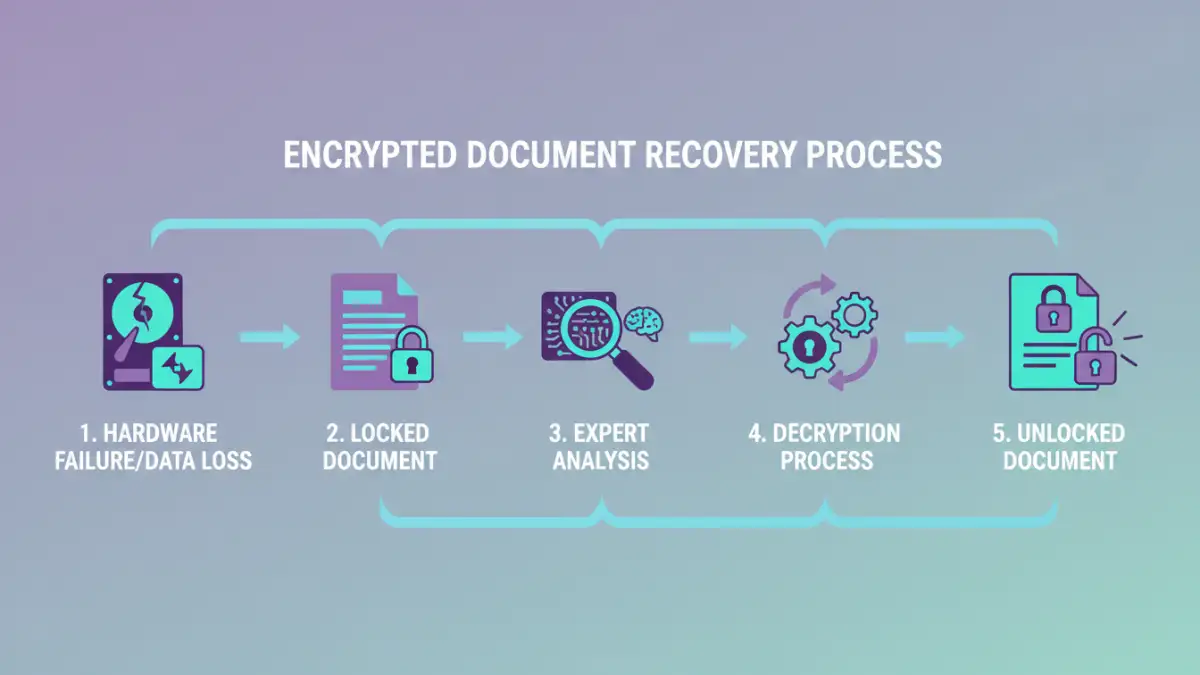
The chosen recovery service employed a multi-pronged approach. Initially, they attempted to recover the lost encryption key from the damaged drive's sectors. This involved deep disk imaging and sector-by-sector analysis to find residual data fragments that could reconstruct the key.
When direct key recovery proved impossible, they moved to advanced password recovery techniques. This wasn't simple brute-forcing but rather intelligent guessing based on linguistic patterns, common passwords, and information gleaned about the company and its former employees (ethically and legally, of course). They also explored potential backdoors or default credentials specific to the encryption software used.
The process was meticulous and time-consuming, requiring significant computational resources and expert analysis. It involved multiple stages of verification and decryption, ensuring data integrity throughout. The successful encrypted document recovery was a testament to the specialists' patience and technical prowess.
Lessons Learned and Best Practices
This incident provided invaluable lessons for the startup. Firstly, the critical importance of a robust password management policy cannot be overstated. This includes secure storage of encryption keys, regular key rotation, and a clear, documented handover procedure for departing employees. Centralized, encrypted password vaults are essential.
Secondly, maintaining regular, verified backups is crucial, but it's equally important to ensure these backups are also secure and that the means to access them (like decryption keys) are managed properly. The team also learned the value of having a pre-established relationship with a data recovery service, so in the event of a crisis, they know exactly who to contact and what information to provide.
Finally, while strong encryption is vital for security, it must be balanced with accessibility. Implementing a system where critical decryption keys or passwords are securely accessible by multiple authorized individuals can prevent single points of failure. This experience transformed their approach to data security, turning a near-catastrophe into a catalyst for improved business resilience.
Comparison Table: Document Recovery Methods
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Standard IT Troubleshooting | Quick for common issues, internal staff can handle | Ineffective for strong encryption, limited tools | Minor software glitches, file corruption without encryption |
| Online Decryption Tools | Accessible, often free for basic use, user-friendly | Privacy concerns, limited encryption types supported, potential malware risk | Simple password-protected PDFs/Office files with known weak passwords |
| Desktop Encryption Software Features | Built-in recovery options (e.g., password hints, reset via account) | Dependent on software provider, may require subscription | Files encrypted with specific software that offers recovery mechanisms |
| Specialized Data Recovery Services | Expertise in complex encryption, high success rates, handles hardware failure | Expensive, time-consuming, requires trust in third party | Critical encrypted data loss, hardware failure with encryption, forgotten master passwords |