
Working with sensitive documents means the need for robust security is paramount. Whether it's confidential business data, personal financial records, or legal agreements, ensuring these files remain private and uncompromised is not just a best practice – it's a necessity in today's digital landscape. I've seen firsthand how a single breach can lead to significant financial loss and reputational damage.
The challenge often lies in finding encryption methods that are both highly secure and practical for everyday use. While basic password protection is common, it's often insufficient against determined attackers. This is where innovative PDF encryption comes into play, offering layers of security that go beyond simple password barriers.
Table of Contents
Understanding PDF Encryption Basics
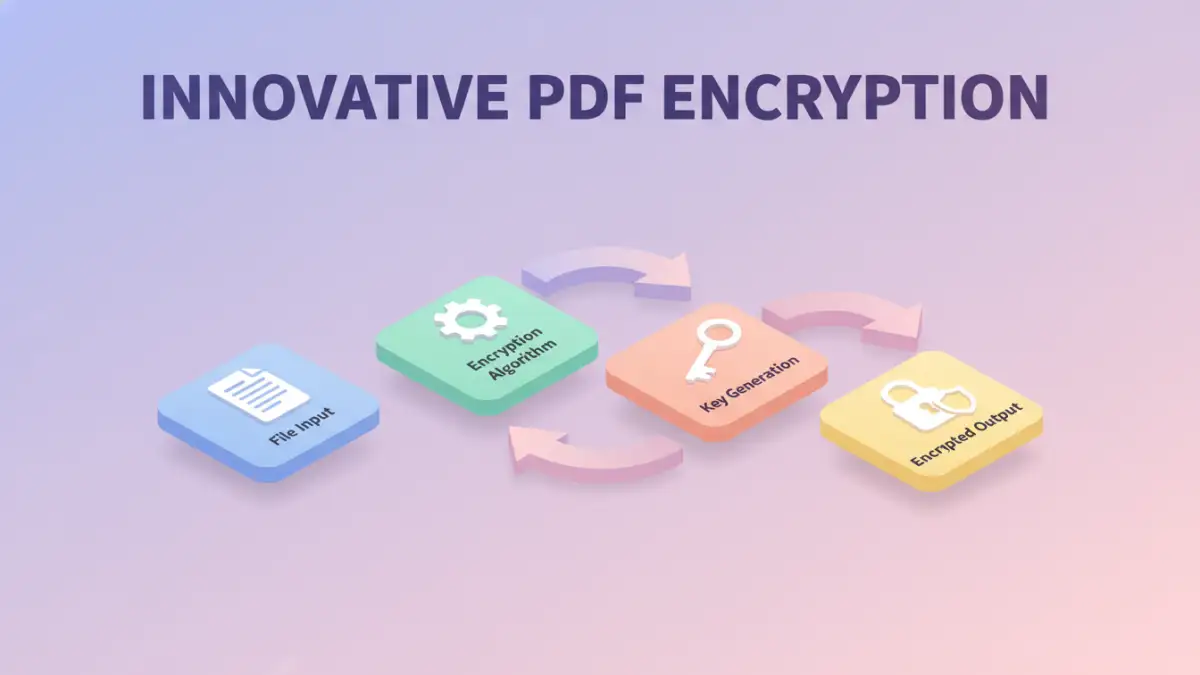
At its core, PDF encryption involves scrambling the content of a document so that it can only be read by authorized individuals. This is typically achieved using an encryption algorithm and a secret key, often a password. Without the correct password, the encrypted content appears as gibberish.
The goal is to make unauthorized access prohibitively difficult. This protects sensitive information from being intercepted, copied, or altered. Over the years, the sophistication of these methods has evolved significantly, driven by the increasing sophistication of cyber threats.
Key Concepts
The fundamental concepts involve algorithms like RC4, AES, and RSA, each offering different levels of security and performance. The 'key' is the secret piece of information used by the algorithm to encrypt and decrypt data. A stronger key, often derived from a complex password, makes the encryption harder to break.
Standard vs. Advanced Encryption

Standard PDF encryption often relies on password protection, which can be as simple as a single password to open the document. Some software allows for setting permissions, like preventing printing or copying text, but these can sometimes be circumvented.
Advanced pdf security, however, utilizes more robust cryptographic methods. This includes stronger encryption algorithms, longer key lengths, and sometimes even multi-factor authentication or more complex key management systems. These advanced techniques are crucial for protecting highly sensitive data.
Innovative PDF Encryption Methods
Beyond basic password protection, several innovative approaches offer enhanced security for PDF documents. These methods are designed to be more resilient against modern hacking techniques and provide greater control over document access.
AES-256 Bit Encryption
AES (Advanced Encryption Standard) is a widely adopted symmetric encryption algorithm. AES-256 uses a 256-bit key, which is currently considered one of the strongest encryption standards available. Many modern PDF tools and software utilize AES-256 for their encryption capabilities, offering a very high level of security against brute-force attacks.
Public Key Cryptography
Also known as asymmetric encryption, this method uses a pair of keys: a public key for encryption and a private key for decryption. Anyone can use the public key to encrypt a message or document, but only the holder of the corresponding private key can decrypt it. This is particularly useful for secure pdf sharing, as you can distribute your public key widely, and recipients use their private key to access the file.
Digital Watermarking
While not strictly encryption, digital watermarking embeds invisible or visible marks within a PDF document. These watermarks can contain information about the recipient, the time of access, or usage restrictions. If the document is leaked, the watermark can help trace its origin and identify unauthorized distribution, acting as a deterrent and an audit trail.
Implementation Best Practices
Choosing the right encryption method is only part of the solution. Proper implementation is equally critical. I always advise clients to use strong, unique passwords for their PDFs, especially when using symmetric encryption.
Regularly updating your software to the latest version ensures you benefit from the most current security patches and encryption protocols. For public key cryptography, secure management of private keys is paramount; losing a private key means losing access to all encrypted documents.
Choosing the Right Method
The best method depends on your specific needs. For simple password protection, standard AES-256 is often sufficient. If you need to share documents securely with multiple parties who have unique access requirements, public key cryptography might be a better fit.
Digital watermarking adds an extra layer of accountability and tracking. When evaluating document encryption methods, consider the sensitivity of the data, the intended audience, and the technical expertise available for managing the security measures.
Comparison Table: PDF Encryption Approaches
| Method | Security Level | Ease of Use | Use Case | Key Management |
|---|---|---|---|---|
| Standard Password (RC4) | Low to Medium | High | Basic document protection | Single password |
| AES-256 Bit Encryption | High | Medium | Sensitive business/personal data | Complex password or key file |
| Public Key Cryptography (RSA) | Very High | Medium (for setup) | Secure sharing with multiple parties | Public/Private key pairs |
| Digital Watermarking | Deterrent/Audit Trail | High | Tracking document distribution | Embedded data |
When selecting an encryption strategy, always prioritize methods that offer strong algorithms and robust key management. Understanding the nuances of each approach allows for more informed decisions about protecting your valuable information.