
The landscape of digital security is constantly evolving, with cyber threats becoming more sophisticated. This necessitates a deep understanding of the prevailing global encryption standards. As someone who has navigated the complexities of securing sensitive information for over a decade, I've seen firsthand how crucial adherence to these standards is for maintaining trust and protecting data.
Staying abreast of the latest developments in encryption technology and the industry's consensus on best practices is not just a technical requirement; it's a fundamental pillar of modern business operations. This report aims to shed light on the current state of these standards, offering insights into what drives them and how organizations can best leverage them.
Table of Contents
Understanding Global Encryption Standards
At its core, encryption is the process of encoding information so that only authorized parties can access it. Global encryption standards are the agreed-upon methodologies and specifications that ensure this encoding process is robust, reliable, and interoperable across different systems and jurisdictions. They are developed through collaboration among security experts, researchers, and industry bodies to create a common baseline for data protection.
These standards are vital for fostering trust in digital communication and transactions. Without them, it would be challenging to ensure that sensitive data, whether personal, financial, or corporate, remains secure when transmitted or stored. The goal is to create a secure digital environment where data integrity and confidentiality are paramount.
The Importance of Standardization
Standardization is key because it allows different technologies and platforms to communicate securely. It prevents fragmentation where incompatible encryption methods could create vulnerabilities. When everyone adheres to the same set of rules, the overall security posture of the digital ecosystem is significantly strengthened. This is particularly important for cross-border data flows and international business operations.
Key Encryption Protocols and Algorithms

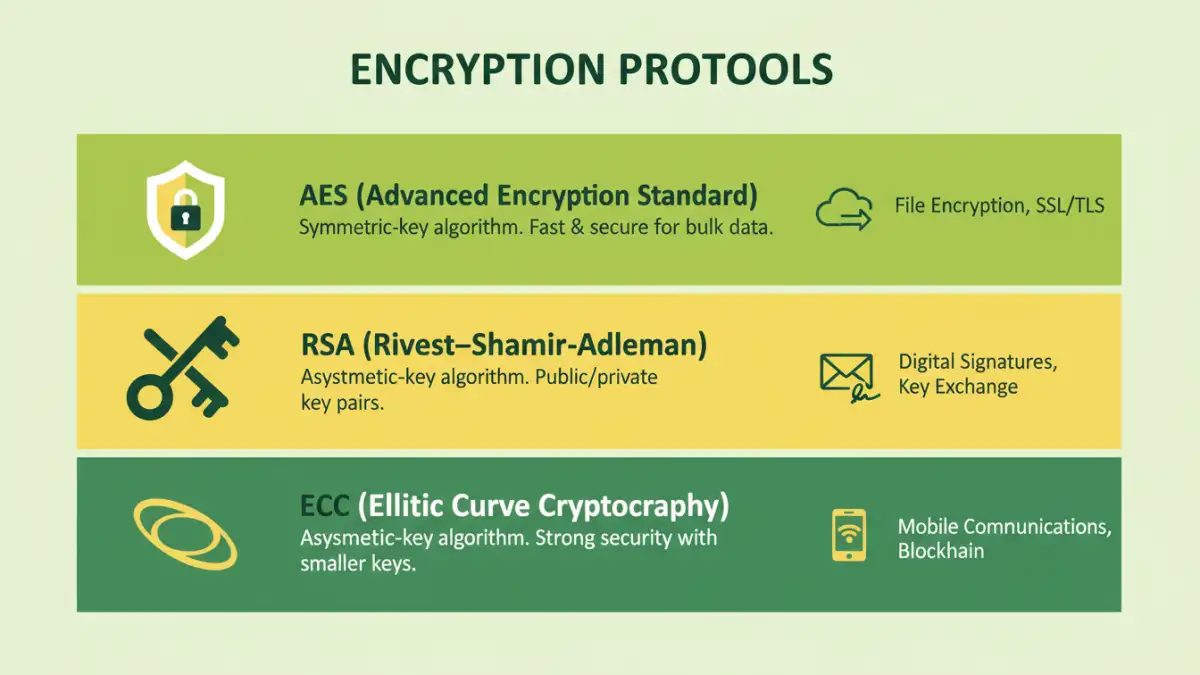
The effectiveness of encryption hinges on the underlying protocols and algorithms. Several have emerged as industry benchmarks, each with specific strengths and applications. Understanding these is fundamental to appreciating the global encryption standards.
Symmetric encryption, like AES (Advanced Encryption Standard), is known for its speed and efficiency, making it suitable for encrypting large volumes of data. Asymmetric encryption, such as RSA, uses a pair of keys (public and private) and is crucial for secure key exchange and digital signatures, forming the backbone of secure communication protocols like TLS/SSL.
Commonly Used Algorithms
AES is the current gold standard for symmetric encryption, widely adopted for its security and performance. For asymmetric encryption, RSA and ECC (Elliptic Curve Cryptography) are prevalent. ECC is gaining traction due to its ability to provide equivalent security with smaller key sizes, leading to better performance on resource-constrained devices.
Compliance and Regulatory Landscape
The implementation of encryption is heavily influenced by compliance requirements and data privacy regulations. Laws like GDPR in Europe, CCPA in California, and HIPAA in the healthcare sector mandate specific levels of data protection, often necessitating the use of strong encryption methods.
Organizations must align their encryption strategies with these legal frameworks to avoid hefty fines and reputational damage. This often means selecting encryption algorithms and key management practices that meet or exceed regulatory expectations. The data encryption report often highlights how these regulations drive the adoption of specific security protocols.
Navigating Global Regulations
The global nature of business means companies must contend with a patchwork of international regulations. Understanding how different regions approach data protection and encryption is critical for multinational corporations. This involves staying updated on evolving legal requirements and ensuring that encryption practices are compliant everywhere data is processed or stored.
Emerging Trends in Encryption
The field of encryption is not static. Researchers are continuously exploring new techniques and refining existing ones to counter emerging threats. Quantum computing, for instance, poses a future challenge to current asymmetric encryption methods, driving research into post-quantum cryptography.
Another significant trend is the increasing use of homomorphic encryption, which allows computations to be performed on encrypted data without decrypting it first. This has profound implications for privacy-preserving data analysis and cloud computing. The evolution of global encryption standards is closely tied to these advancements.
The Rise of End-to-End Encryption
End-to-end encryption (E2EE) has become a cornerstone of secure communication, ensuring that only the sender and intended recipient can access the message content. Its widespread adoption in messaging apps and collaboration tools underscores the growing demand for user-centric privacy and security. This trend reflects a broader societal push for greater control over personal data.
Strategies for Effective Implementation
Implementing encryption effectively goes beyond just choosing an algorithm. It involves a holistic approach that includes secure key management, regular audits, and employee training. My experience has shown that without proper key management, even the strongest encryption can be compromised.
Organizations should develop clear policies for encryption, define which data needs protection, and implement robust procedures for key generation, storage, rotation, and destruction. This ensures that the encryption measures are sustainable and resilient against attacks. Choosing the right security protocols is only part of the solution; their practical application matters most.
Key Management Best Practices
Secure key management is often the weakest link in an encryption system. Implementing hardware security modules (HSMs), using strong access controls, and segregating key management functions are essential. Regular review and updates to key management policies are also crucial to adapt to evolving threats and technologies.
Comparison Table: Encryption Methods and Use Cases
| Encryption Method | Primary Use Case | Key Strength | Key Weakness | Typical Application |
|---|---|---|---|---|
| AES (Symmetric) | Bulk data encryption | Speed, efficiency | Key distribution challenge | File encryption, database encryption |
| RSA (Asymmetric) | Secure key exchange, digital signatures | Key management simplified (public key) | Slower performance | TLS/SSL, secure email (PGP) |
| ECC (Asymmetric) | Secure key exchange, digital signatures | High security with smaller keys, efficient | More complex mathematics | Mobile devices, IoT, cryptocurrencies |
| Homomorphic Encryption | Computation on encrypted data | Data privacy during processing | Significant performance overhead | Confidential cloud computing, secure analytics |