
Working with password-protected documents can be frustrating, especially when the original owner is no longer available. This often happens in business settings when key personnel leave, or in personal situations involving inherited digital assets. The challenge lies in gaining access to information that is vital for ongoing operations or personal matters.
Over my career, I've encountered numerous scenarios where critical data was locked away behind encryption. These situations demand a systematic approach, combining technical know-how with a deep understanding of data security principles. Successfully navigating these challenges ensures business continuity and preserves important personal histories.
Table of Contents
Understanding Document Inheritance
When we talk about inherited files, we're often referring to digital assets left behind by a previous owner, whether that's a colleague who left the company or a family member who has passed away. These files can contain anything from sensitive financial records and proprietary business plans to personal memories stored in documents, photos, or videos.
The complexity arises because these files are typically secured using encryption or passwords to protect privacy and intellectual property. Without the correct credentials or access keys, these valuable pieces of information can become inaccessible, creating significant hurdles for those who need them.
The Importance of Legacy Data
Legacy data access is crucial for several reasons. For businesses, it ensures that operations can continue smoothly without interruption, preventing loss of productivity or critical project data. For individuals, it allows for the preservation of personal history, estate management, and access to important personal documents.
Common Challenges with Encrypted Files

The primary obstacle is, of course, the encryption itself. Standard password-protected files, like those encrypted with a simple password in Microsoft Office or Adobe PDF, are one type of challenge. However, more robust encryption methods used by specialized software or operating systems present a higher barrier.
Another significant challenge is the lack of documentation. Often, the original owner may not have left clear instructions or stored the passwords in a readily accessible location. This leaves inheritors scrambling to find ways to unlock the data, sometimes without even knowing the specific encryption method used.
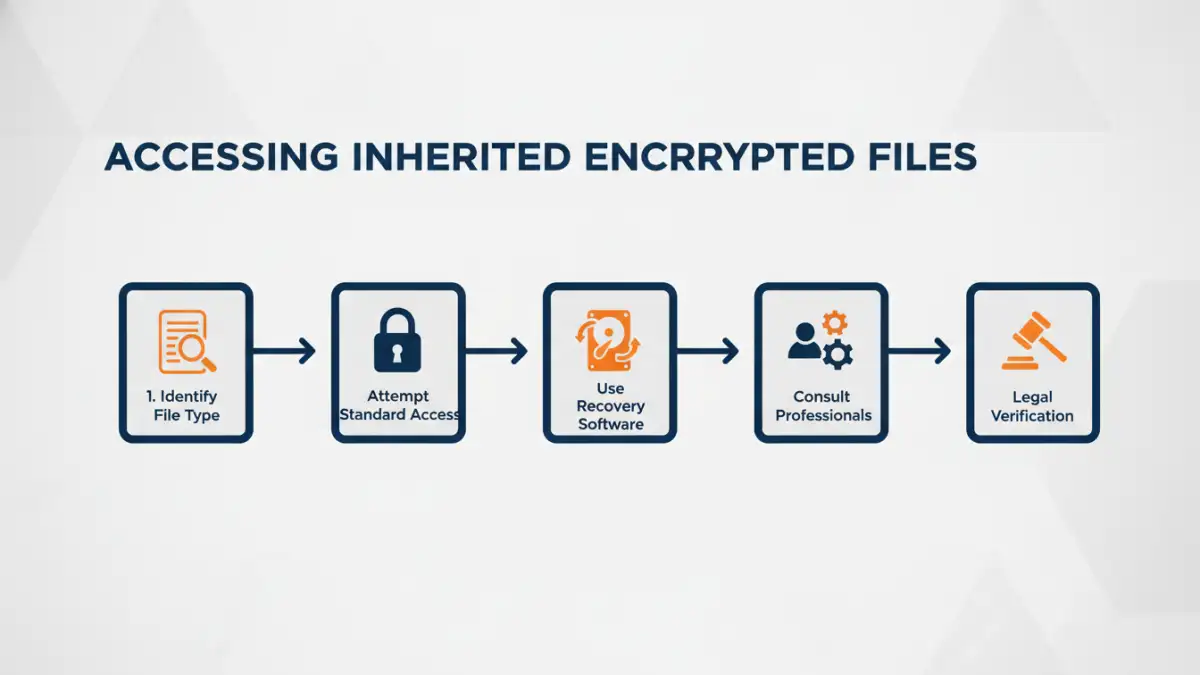
Methods for Accessing Inherited Files
When faced with inherited encrypted files, a multi-pronged approach is often necessary. The first step is always to try the most straightforward methods, assuming the encryption isn't overly complex.
Attempting Standard Password Recovery
For common file types like Microsoft Word, Excel, PowerPoint, or Adobe PDFs, there are often built-in password recovery features or standard password prompts. If the password is known or can be guessed (e.g., based on common patterns or personal information), this is the quickest route. Many operating systems and applications offer options to 'reset' or 'recover' passwords, though this typically requires the original owner's credentials or administrator privileges.
Utilizing Specialized Software and Tools
When standard methods fail, specialized software designed for password recovery or data decryption becomes essential. These tools vary widely in their capabilities, from brute-force attacks (trying every possible combination) to dictionary attacks (using lists of common words and phrases) and exploiting known vulnerabilities in older encryption algorithms.
For particularly stubborn cases, particularly those involving employee file recovery where company policies might be involved, engaging professional data recovery services can be a viable option. These experts have access to advanced techniques and hardware that can often unlock even heavily encrypted files. This is also where the concept of digital inheritance becomes critical, as it involves the legal transfer of these digital assets.
Legal and Ethical Considerations
Accessing inherited encrypted files is not just a technical problem; it also involves significant legal and ethical dimensions. Depending on the jurisdiction and the nature of the data, there are laws governing data privacy, digital asset inheritance, and intellectual property rights.
It's crucial to ensure that any attempt to access these files complies with relevant laws. For instance, attempting to brute-force a password on a file that you do not have legal rights to could have legal repercussions. In a business context, company policies and data protection regulations like GDPR must be strictly adhered to. Understanding the legal framework surrounding digital inheritance is paramount before proceeding.
Preventative Measures for the Future
Learning from these challenges, it's clear that proactive measures are the best defense against future data access issues. Establishing clear protocols for document security and access management within an organization is key. This includes creating a robust system for password management and ensuring that critical data is backed up securely.
For personal use, maintaining an inventory of important digital assets and their access credentials, stored securely, can prevent significant distress for loved ones. This could involve using a secure password manager or a digital vault that can be passed on. Implementing strong encryption from the outset, with well-documented access procedures, is always more effective than trying to recover lost access later.
Comparison Table: Methods for Accessing Encrypted Files
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Standard Password Prompt | Quick and easy if password is known or guessable. No extra software needed. | Only works for basic password protection. Useless if password is unknown. | Simple document encryption (e.g., Office, PDF). |
| Password Recovery Software | Can attempt to crack passwords using various techniques (brute-force, dictionary). Available for different file types. | Can be time-consuming, may require significant computing power. Success not guaranteed. Potential privacy concerns with some tools. | Moderately complex encryption where the password is lost but the file is legally accessible. |
| Professional Data Recovery Services | Highest success rate, handles complex encryption, expert knowledge. Legally compliant options available. | Most expensive option. Requires trusting a third party with sensitive data. | Highly sensitive or critical data, complex or unknown encryption, legal requirements for employee file recovery. |
| Digital Inheritance Planning | Proactive. Ensures smooth access for beneficiaries. Minimizes future access issues. | Requires upfront effort and planning. Needs secure storage for credentials. | Anyone wanting to ensure their digital assets are accessible after their passing. |