
When building applications that handle sensitive data, providing clear and secure code examples is paramount. Developers need to understand not just how to use an API, but how to use it safely. This is especially true for document-related APIs where privacy and integrity are critical. I've seen many projects falter due to insufficient guidance on security best practices within their code examples.
Effectively documenting secure document API code examples ensures that developers can integrate these functionalities without introducing vulnerabilities. It bridges the gap between raw API functionality and secure, real-world application development. This guide aims to provide that clarity, offering insights and practical approaches.
Table of Contents
Understanding the Importance of Secure Examples
The primary goal of any API is to enable functionality, but when that functionality involves documents, security cannot be an afterthought. Providing insecure code examples can lead to widespread data breaches and erode user trust. Developers often copy and paste code, so the examples themselves must be robust and secure by default.
My experience has shown that developers appreciate examples that not only work but also demonstrate secure coding habits. This builds confidence and promotes a culture of security within development teams. It’s about empowering users to build secure applications from the outset.
Common Pitfalls to Avoid
Developers might overlook crucial security steps like proper input validation, secure credential handling, or appropriate error management. Insecure examples can inadvertently teach these bad habits. For instance, an example that hardcodes API keys or exposes sensitive data in logs is a significant risk.
Core Principles for Secure API Documentation
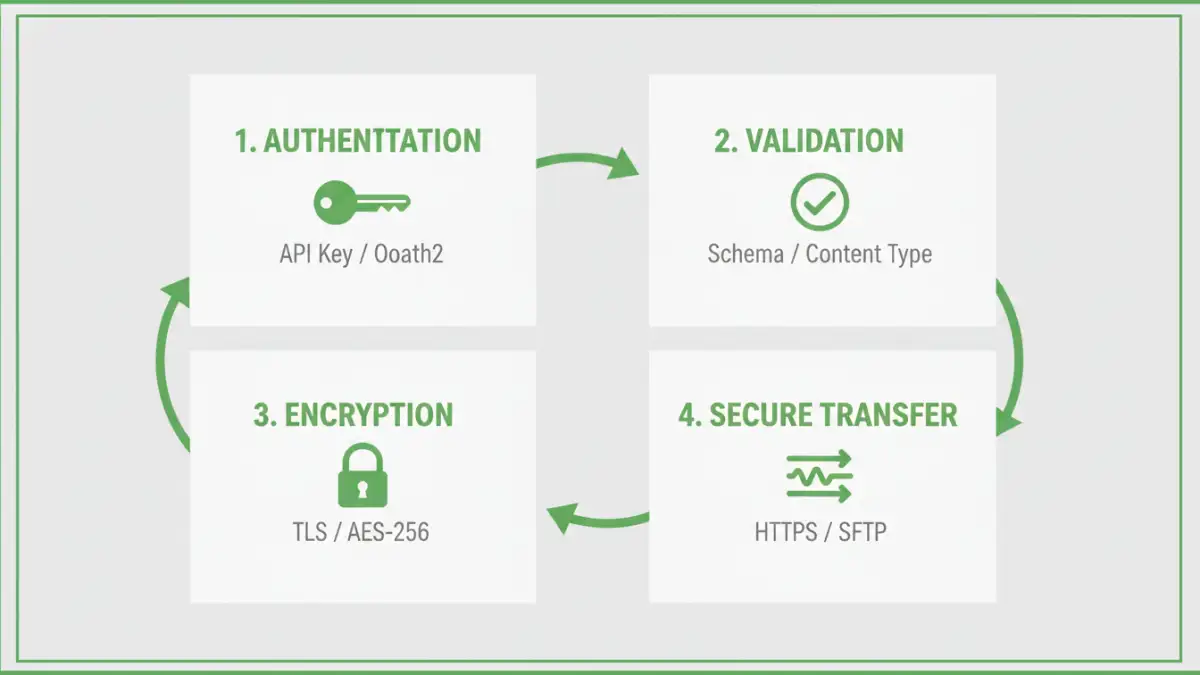
When crafting documentation for APIs that handle documents, several core principles must be upheld. These principles guide the creation of code examples that are both functional and secure. Adhering to them is essential for protecting user data and maintaining API integrity.
Firstly, clarity and conciseness are key. Developers should be able to understand the code and its security implications quickly. Secondly, security must be integrated, not bolted on. Examples should inherently demonstrate secure practices rather than requiring developers to remember separate security checklists.
Secure Coding Standards
This involves adhering to industry-standard secure coding practices. For document APIs, this often means emphasizing encryption, secure authentication, and authorization mechanisms. The code examples should reflect these standards transparently, making them easy to follow and implement correctly.
Practical Secure Document API Code Examples
Let's look at some practical scenarios and how to present them securely. We'll focus on common tasks like uploading, downloading, and encrypting documents using an API.
Consider an API endpoint for uploading a document. A secure example would include code that validates the file type and size before uploading, and ensures the data is sent over HTTPS. It should also demonstrate how to handle potential errors gracefully without revealing sensitive information.
Document Upload Example
Here’s a conceptual Python snippet illustrating a secure upload:
import requests
def upload_document(api_url, api_key, file_path):
allowed_types = ['pdf', 'docx', 'txt']
max_size_mb = 10
filename = file_path.split('/')[-1]
file_extension = filename.split('.')[-1].lower()
file_size_mb = os.path.getsize(file_path) / (1024 * 1024)
if file_extension not in allowed_types or file_size_mb > max_size_mb:
print("Error: Invalid file type or size.")
return None
headers = {'Authorization': f'Bearer {api_key}'}
with open(file_path, 'rb') as f:
files = {'file': (filename, f)}
response = requests.post(api_url + '/upload', headers=headers, files=files)
if response.status_code == 200:
print("Document uploaded successfully.")
return response.json()
else:
print(f"Upload failed: {response.status_code} - {response.text}")
return None
This example includes basic validation and uses a bearer token for authentication, assuming HTTPS is enforced by the server. It also shows how to handle the API response, both success and failure.
Document Download and Decryption
When downloading and decrypting documents, the key is to manage the decryption keys securely and ensure the downloaded content is handled appropriately. An example might show downloading a file and then decrypting it using a provided key, ensuring the key itself is not exposed in logs or insecure variables.
Advanced Security Considerations
Beyond basic examples, advanced topics like end-to-end encryption, access control management, and auditing are crucial for high-security applications. Documenting these requires careful explanation and illustrative code.
For instance, demonstrating how to implement signed URLs for temporary, secure access to documents can be invaluable. This involves generating a URL with an embedded signature that expires after a set time, allowing controlled access without needing a persistent API key for the user.
Best Practices for Documentation
To ensure your secure document API code examples are effective, follow these best practices. They are derived from years of working on API documentation and seeing what truly helps developers.
Always provide context for the code. Explain what each part does, especially the security-related aspects. Use clear language and avoid jargon where possible. Furthermore, ensure your examples are runnable and tested, perhaps providing a sandbox environment or clear setup instructions. Showing API usage examples that are easy to integrate is key.
| Feature | Description | Security Implication | Example Focus |
|---|---|---|---|
| Authentication | How users prove their identity (e.g., API keys, OAuth) | Prevents unauthorized access | Secure key management, token usage |
| Authorization | What authenticated users can do (permissions) | Ensures users only access permitted data | Role-based access control logic |
| Input Validation | Checking data before processing (file type, size) | Mitigates injection attacks, malformed data issues | File type/size checks in examples |
| Data Encryption | Protecting data at rest and in transit | Confidentiality and integrity | HTTPS usage, optional client-side encryption |
| Error Handling | Managing and reporting errors securely | Prevents information leakage | Generic error messages, logging best practices |