
The digital landscape has blurred geographical lines, making global collaboration a daily reality for many organizations. While this interconnectedness offers immense benefits, it simultaneously introduces a complex web of challenges, especially when dealing with sensitive documents that need to traverse international borders. Ensuring these files remain secure and compliant with diverse legal frameworks isn't just a technical task; it's a critical legal and ethical responsibility.
Table of Contents
Understanding the Complexities of Cross-Border Data
Working as a software engineer for over a decade, I've seen firsthand how easily data can move across the globe, often without organizations fully grasping the legal implications. What might be permissible in one country could lead to severe penalties in another. This global fluidity demands a deep understanding of varied legal requirements and their impact on sensitive document security.
Key Regulatory Frameworks
Several major regulatory frameworks dictate how organizations must handle data, particularly when it crosses borders. The European Union's GDPR (General Data Protection Regulation) is perhaps the most well-known, setting stringent rules for personal data protection. Similarly, the CCPA (California Consumer Privacy Act) in the US and various national laws in Asia, Africa, and South America all contribute to a fragmented, yet interconnected, regulatory environment. Organizations must identify which laws apply to their specific data transfers and tailor their compliance efforts accordingly.
Defining Sensitive Documents in a Global Context
What constitutes a 'sensitive document' can also vary by jurisdiction. Generally, this includes personal identifiable information (PII), protected health information (PHI), financial records, intellectual property, and trade secrets. However, some laws might extend this definition to include political opinions, religious beliefs, or even biometric data. Understanding these nuances is crucial for implementing effective sensitive document security measures that meet global standards.
Navigating Cross-Border Data Transfer Challenges

Moving data from one country to another is rarely a straightforward technical exercise. Beyond the technical hurdles, organizations face significant legal and operational challenges that can impact their ability to maintain international file protection. Failing to address these can result in hefty fines, reputational damage, and loss of customer trust.
Jurisdiction and Enforcement Discrepancies
One of the biggest headaches arises from conflicting jurisdictional claims. A data breach occurring in one country might involve data subjects from multiple nations, each with its own reporting requirements and enforcement bodies. This can create a compliance nightmare, as organizations try to satisfy differing legal obligations simultaneously. My experience has shown that a proactive, multi-jurisdictional approach is far more effective than a reactive one.
Data Localization and Sovereignty
Many countries are increasingly enacting data localization laws, which require certain types of data to be stored and processed within their national borders. This concept of data sovereignty aims to give nations more control over their citizens' information. For global companies, this means potentially setting up local data centers or using specific cloud providers, adding layers of complexity to their cross-border data transfer strategies.
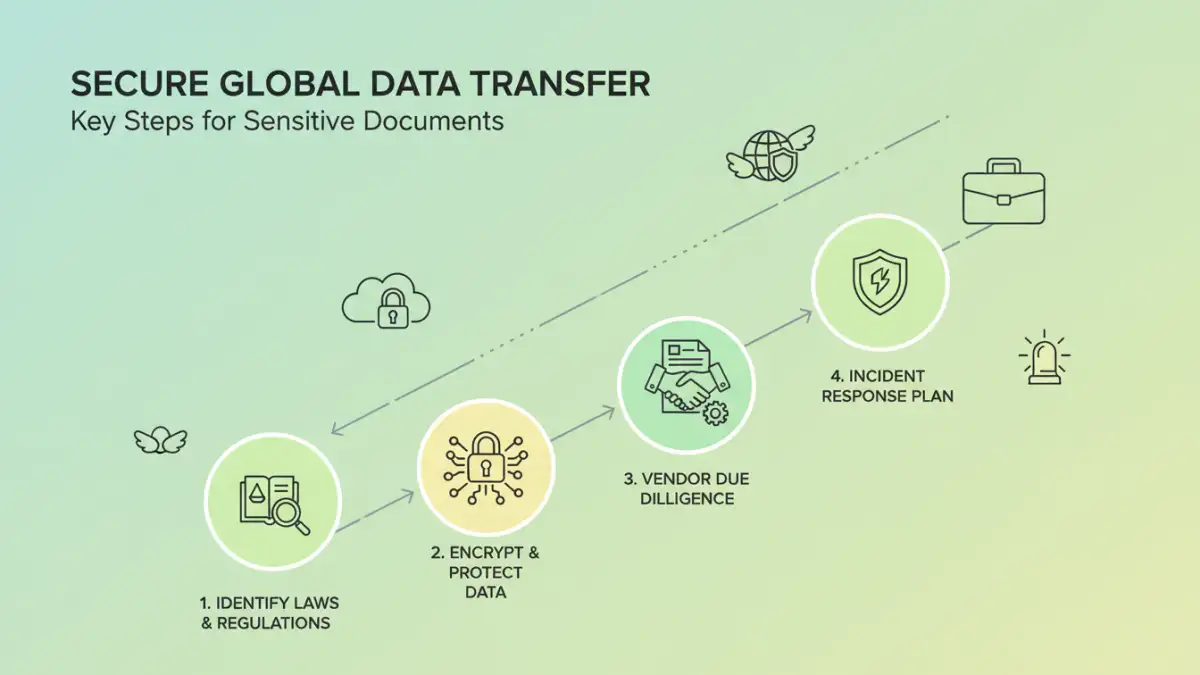
Implementing Robust International File Protection Strategies
Given the intricate legal landscape, organizations need to adopt comprehensive strategies to safeguard their sensitive documents during international transfers. This goes beyond basic password protection and delves into architectural and policy-driven solutions. The goal is to build resilience and ensure compliance regardless of where the data resides or travels.
Leveraging Advanced Encryption and Access Controls
At the heart of any robust sensitive document security strategy is strong encryption. End-to-end encryption for data in transit and encryption at rest for stored data are non-negotiable. Combined with strict access controls, multi-factor authentication, and granular permission management, organizations can significantly reduce the risk of unauthorized access. I've often advised teams to implement least privilege access, ensuring only those who absolutely need to view or modify a document can do so.
Data Minimization and Pseudonymization
A fundamental principle in many data protection laws is data minimization – collecting and retaining only the data absolutely necessary for a specific purpose. Pseudonymization, which replaces direct identifiers with artificial ones, can further enhance security by making it harder to link data back to an individual without additional information. These techniques reduce the risk exposure should a breach occur, making the data less valuable to malicious actors.
Establishing Global Security Standards and Compliance
Achieving and maintaining compliance with global security standards requires a continuous effort, integrating legal considerations into every aspect of data handling. This includes everything from selecting technology vendors to preparing for potential security incidents. Establishing a culture of security awareness is also paramount.
Due Diligence for Third-Party Vendors
Many organizations rely on third-party cloud providers, SaaS tools, and other vendors for data storage and processing. It's critical to conduct thorough due diligence to ensure these vendors meet your international file protection requirements and comply with relevant cross-border data transfer laws. This involves reviewing their security certifications, audit reports, and contractual agreements, especially regarding data residency and sub-processors. My experience has taught me that the weakest link in a security chain is often a third party.
Proactive Incident Response Planning
Despite best efforts, data breaches can happen. A well-defined incident response plan is crucial for mitigating damage and ensuring legal document handling protocols are followed. This plan should include clear steps for identifying, containing, eradicating, and recovering from an incident, as well as specific procedures for notifying affected individuals and regulatory authorities in different jurisdictions. Regular drills and updates to the plan are essential for effectiveness.
Comparison Table: Cross-Border Data Transfer Mechanisms
| Mechanism | Description | Key Requirement | Best Use Case |
|---|---|---|---|
| Standard Contractual Clauses (SCCs) | Pre-approved model data protection clauses for transfers outside 'adequate' regions. | Binding contractual obligations between data exporter and importer. | Most common for transfers to third countries without adequacy decisions. |
| Binding Corporate Rules (BCRs) | Internal corporate rules approved by data protection authorities for intra-group transfers. | Comprehensive internal policy outlining data protection for multinational companies. | Large multinational corporations for internal data transfers. |
| Adequacy Decisions | European Commission decision that a non-EU country offers equivalent data protection. | Country's legal framework offers 'essentially equivalent' protection to EU law. | Transfers to countries deemed 'adequate' by the EU (e.g., Japan, New Zealand). |
| Consent | Explicit, informed, and unambiguous consent from the data subject for the transfer. | Consent must be freely given, specific, informed, and revocable. | Limited, specific, and non-repetitive transfers where other mechanisms aren't suitable. |