
Securing sensitive information during transit is a perennial challenge for both individuals and organizations. As digital footprints expand and remote work becomes the norm, the methods we use to share files have evolved dramatically. Among these, password protected sharing has emerged as a critical layer of defense against unauthorized access.
Understanding how this method is being adopted and used provides valuable insights into current data security practices. By examining user statistics, we can gauge the effectiveness of these measures and identify areas for improvement in how we protect digital assets.
Table of Contents
Adoption Trends in Secure Sharing
The adoption of secure file sharing methods, particularly those involving passwords, has seen a steady increase. This rise is directly correlated with heightened awareness of data breaches and the increasing value of digital information. Organizations are moving away from email attachments for sensitive documents, opting instead for dedicated secure file sharing solutions that offer encryption and access controls.
The convenience of password protected sharing, when implemented correctly, strikes a balance between usability and security. It allows for granular control over who can access specific files, reducing the risk of accidental exposure. This has driven its integration into various collaboration platforms and cloud storage services.
Growth in Encrypted File Transfer
Statistics from various cybersecurity reports indicate a significant upward trend in the use of encrypted file transfer protocols and services. Users are actively seeking out tools that provide end-to-end encryption, with password protection serving as a primary access gate. This demand is fueled by regulatory compliance requirements and the desire to maintain client trust.
User Demographics and Preferences
When we look at who is using these secure methods, a diverse picture emerges. While large enterprises have been early adopters due to strict compliance needs, small and medium-sized businesses (SMBs) are rapidly catching up. SMBs often face similar threats but may have fewer resources, making user-friendly password protected sharing solutions particularly appealing.
Individual users, especially those handling personal financial information or proprietary creative work, are also increasingly employing these techniques. The proliferation of free and freemium tools has lowered the barrier to entry, making advanced security features accessible to a broader audience. Preferences often lean towards solutions that require minimal technical expertise.
Motivations for Password Protection
The primary motivation behind choosing password protected sharing is, unsurprisingly, security. Users want to prevent unauthorized access, protect intellectual property, and comply with data privacy regulations like GDPR or HIPAA. The fear of data breaches and the associated reputational damage is a powerful driver for adopting robust security measures.
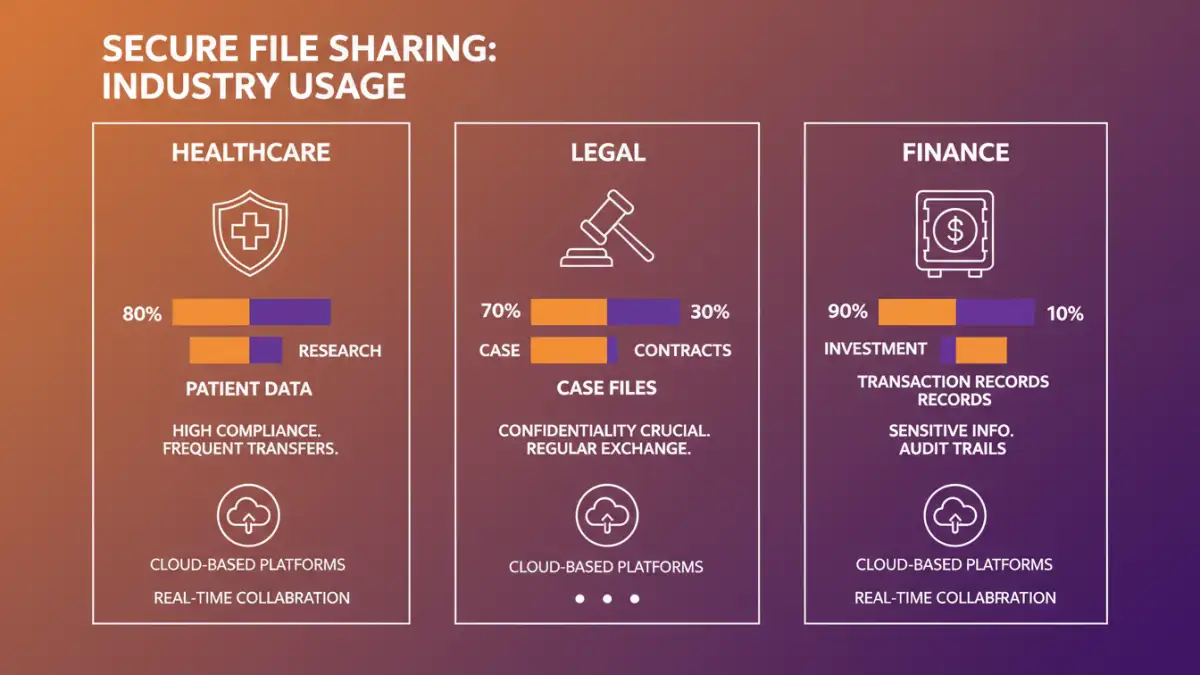
Industry-Specific Usage Patterns
Different industries exhibit unique patterns in their adoption and usage of secure file sharing. The healthcare sector, for instance, has stringent requirements for patient data privacy, making encrypted file transfer a necessity. Similarly, the legal profession relies heavily on confidentiality, with password protected documents being standard practice for case files and client communications.
Financial services are another major user base, where the protection of sensitive financial data is paramount. E-commerce platforms and technology companies also utilize these methods extensively for sharing proprietary code, customer data, and internal reports. The common thread is the presence of high-value or sensitive information that requires careful handling.
Impact on Collaboration
While security is the main driver, the impact on collaboration is also a key consideration. Secure file sharing platforms aim to facilitate teamwork without compromising safety. Features like secure links, expiration dates for shared files, and audit trails enhance collaborative workflows. Understanding these features helps users choose the right tools for their team's needs.
Security Concerns and Motivations
Despite the benefits, users still harbor security concerns. The strength of the password itself is a critical factor, and the risk of weak passwords being compromised remains a significant vulnerability. Users need education on creating strong, unique passwords and the benefits of using password managers.
Another concern is the security of the sharing platform itself. Users need assurance that the service provider has robust security measures in place to protect the data being shared. Trust in the platform is therefore as important as the password protection mechanism itself. This fuels the demand for reputable and transparent service providers.
Document Sharing Statistics Insights
Looking at document sharing statistics reveals that a substantial percentage of shared files contain sensitive information. This underscores the critical need for robust security measures. Reports suggest that many data breaches originate from insecure file sharing practices, highlighting the gap between perceived security and actual risk.
Future Outlook for Encrypted Transfer
The future of password protected sharing and encrypted file transfer looks increasingly integrated and sophisticated. We can expect to see more AI-driven security features, such as intelligent threat detection and automated policy enforcement. The focus will likely remain on making security seamless and intuitive for the end-user.
As cyber threats continue to evolve, the demand for secure, reliable, and user-friendly file sharing solutions will only grow. Password protection will remain a cornerstone of these solutions, adapting to new technologies and user expectations to ensure data remains safe in an increasingly connected world.
Comparison Table: Secure File Sharing Methods
| Method | Ease of Use | Security Level | Best For | Considerations |
|---|---|---|---|---|
| Email Attachments (with password) | High | Low to Medium (depends on password strength & email security) | Quick, small, non-critical files | Vulnerable to interception before encryption; password shared insecurely |
| Cloud Storage (link sharing with password) | Medium to High | Medium to High (depends on provider & password strength) | Documents, project files, collaboration | Requires trusted cloud provider; password management is key |
| Dedicated Secure File Transfer Services | Medium | High (often end-to-end encryption) | Large files, sensitive data, regulated industries | Can involve costs; requires learning new platform |
| File Encryption Software (e.g., ZIP with password) | Medium | High (strong encryption algorithms) | Archiving, long-term storage, standalone file security | Requires software installation; recipient needs compatible software |