
Working with sensitive documents, whether they are PDFs or Microsoft Word files, often requires a robust security strategy. I've seen firsthand how a lack of clear guidelines can lead to weak passwords, inconsistent protection, and ultimately, vulnerabilities. Establishing a set of consistent password rules isn't just about making things look professional; it's a critical step in safeguarding confidential information from unauthorized access.
Whether you're a freelancer protecting client deliverables or part of a larger organization managing proprietary data, implementing uniform security measures for your files is paramount. This involves understanding the nuances of password protection across different file types and ensuring that the policies you set are both effective and practical for everyday use.
Table of Contents
Understanding the Need for Rules
The digital landscape is fraught with risks, and documents are often prime targets for data breaches. Without standardized guidelines, individuals might opt for simple, easily guessable passwords or forget them altogether, creating security gaps. A consistent password policy ensures that everyone understands the requirements for protecting sensitive information, regardless of the file type.
This uniformity helps prevent common mistakes like using the same password across multiple documents or employing easily cracked combinations. It streamlines the security process and reduces the likelihood of accidental data exposure, contributing to overall better document access control.
Key Concepts in Document Security
When we talk about document security, several core concepts come into play. These include encryption, which scrambles data to make it unreadable without a key (the password), and access control, which dictates who can view, edit, or share a document. Understanding these principles is fundamental to setting effective password rules.
PDF Password Protection Strategies

PDFs are a common format for sharing finalized documents, and they offer built-in security features. You can typically set passwords to restrict opening the document or to limit actions like printing, copying text, or editing. My experience suggests that using separate passwords for opening versus permissions offers a good balance of security and usability.
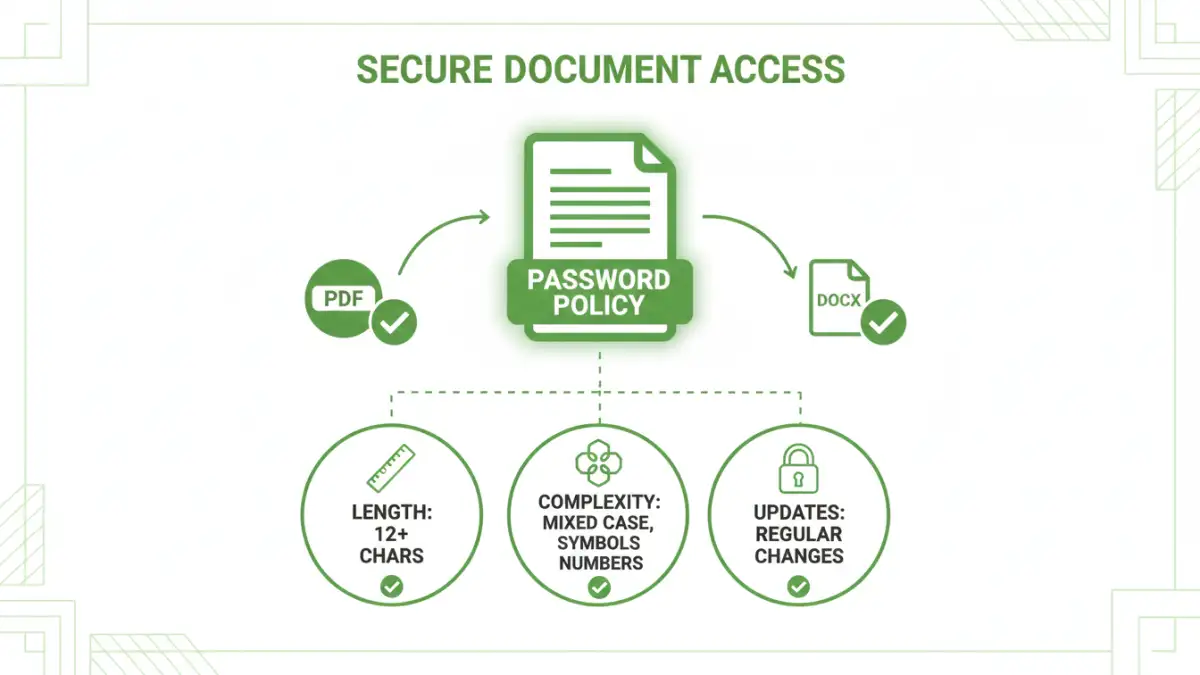
When implementing pdf doc password rules, it's crucial to advise users on creating strong, unique passwords for each document if possible, or at least adhering to a strong set of criteria. For instance, requiring a minimum length, a mix of upper and lowercase letters, numbers, and symbols significantly enhances security.
Setting Up PDF Passwords
Most PDF readers and editors, like Adobe Acrobat or even built-in browser functions, allow you to set passwords. The process usually involves navigating to security settings within the file properties. It’s important to document these steps clearly for anyone who needs to secure a PDF.
Word Document Security Measures
Microsoft Word documents also provide robust password protection options. You can encrypt a document by requiring a password to open it, thereby preventing unauthorized viewing. Like PDFs, Word allows for different levels of protection, though the primary focus is typically on preventing access entirely.
When setting passwords for Word documents, the same principles of strong password creation apply. A policy might mandate a minimum character count, the inclusion of diverse character types, and regular password updates to maintain file security standards.
Encrypting Word Files
To encrypt a Word document, you typically go to 'File' > 'Info' > 'Protect Document' and then select 'Encrypt with Password'. This action immediately secures the file, but it relies entirely on the strength of the password chosen by the user.
Creating a Consistent Policy
Developing a comprehensive and consistent password policy is the cornerstone of effective document security. This policy should outline the requirements for password strength, frequency of changes, and how passwords should be managed and shared. It needs to be clear, concise, and easily accessible to all users.
The policy should also address what to do in case a password is lost or forgotten, and it should be reviewed and updated periodically to adapt to evolving security threats. A well-defined policy minimizes ambiguity and ensures uniform application of security measures across all documents.
Elements of a Strong Policy
A strong password policy typically includes requirements for password length (e.g., minimum 12 characters), complexity (e.g., uppercase, lowercase, numbers, symbols), and prohibits common or easily guessable information. It may also specify password expiration periods and guidelines for secure password storage, such as using a password manager.
Best Practices for Enforcement
Enforcing password rules effectively is as important as creating them. This can involve technical controls where possible, but often relies on user education and regular audits. Training sessions can help users understand why these rules are in place and how to comply with them.
Regularly auditing document security settings and providing feedback can reinforce the importance of the policy. When users understand the risks and the mechanisms for protection, compliance becomes more natural, leading to better overall document access control.
Comparison Table: Password Protection Methods
| Method | Description | Pros | Cons | Use Case |
|---|---|---|---|---|
| PDF Password (Open) | Requires password to view the PDF content. | Simple, direct protection against viewing. | Doesn't restrict editing or printing if password is known. | Securing sensitive reports, contracts. |
| PDF Password (Permissions) | Restricts actions like printing, editing, copying. | Allows viewing but controls specific actions. | Requires a separate password for opening if set. | Sharing drafts, preventing unauthorized copying. |
| Word Document Encryption | Requires password to open the .docx file. | Strong protection against unauthorized access. | Can be difficult to recover if password is lost. | Protecting proprietary business plans, financial data. |
| Third-Party Tools | Software or online services offering advanced encryption and password management. | Often more features, better usability, batch processing. | May involve costs, privacy concerns with online tools. | Bulk encryption, complex security needs. |