
Working with sensitive legal documents in a litigation context demands the utmost attention to security. The integrity and confidentiality of case files are paramount, and any breach can have severe repercussions. Ensuring robust protection for your digital evidence and client information isn't just good practice; it's a professional and ethical imperative.
As someone who has navigated complex digital workflows for over a decade, I've seen firsthand how crucial secure document handling is, especially when dealing with legal proceedings. From initial discovery to final presentation, every PDF carries weight, and protecting it is a core responsibility.
Table of Contents
Understanding the Basics of PDF Security
At its core, PDF security involves safeguarding the content of a Portable Document Format file from unauthorized access, modification, or distribution. This is typically achieved through various mechanisms, primarily encryption and access controls. Encryption scrambles the data, making it unreadable without a specific key or password. Access controls, on the other hand, define who can view, print, or edit the document.
Encryption Levels
PDFs can be secured using different encryption algorithms. Older standards like 40-bit RC4 are less secure and easily compromised. Modern standards, such as AES-128 and AES-256, offer much stronger protection, making them the preferred choice for sensitive legal materials. The strength of the encryption directly correlates with the difficulty of unauthorized decryption.
Key Considerations for Litigation

In the realm of litigation, the stakes for document security are incredibly high. This isn't just about protecting proprietary business information; it's about preserving the integrity of evidence, maintaining client privilege, and adhering to strict court rules and discovery protocols. Every step taken must consider the potential legal ramifications of a security lapse.
This means that effective litigation document management goes beyond simply storing files. It involves a comprehensive strategy that addresses access, audit trails, and tamper-proofing. The goal is to ensure that documents remain authentic and admissible throughout the legal process, which is a core aspect of secure e discovery.
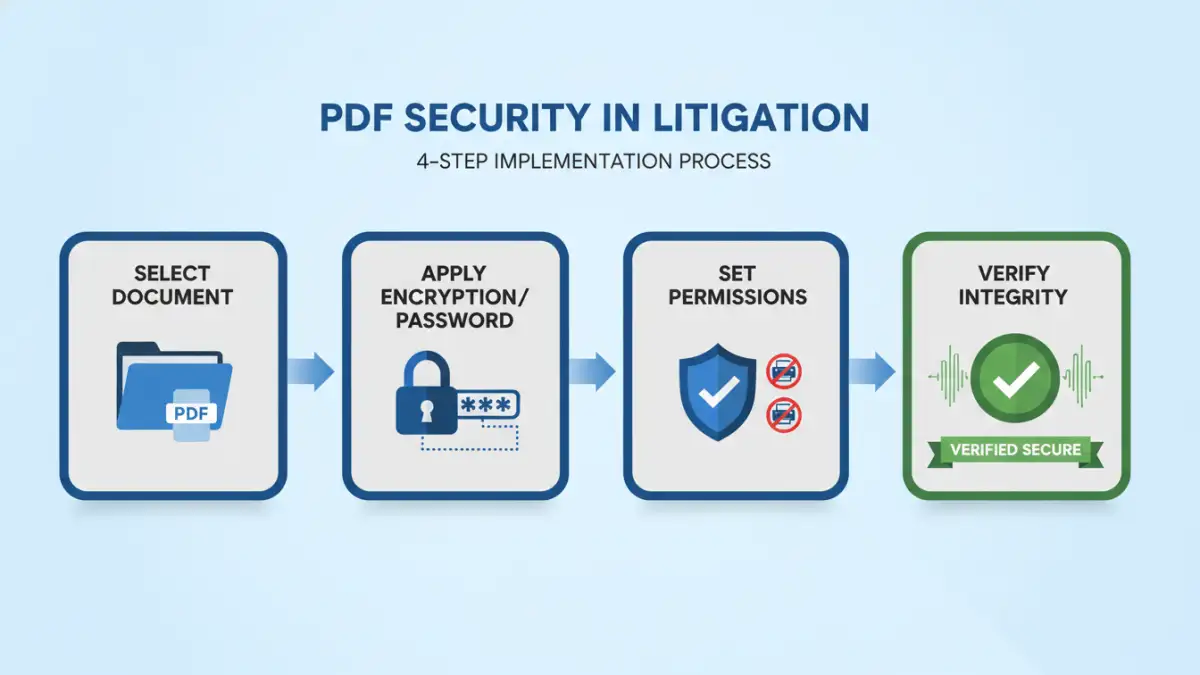
Implementation Methods
Securing PDFs for litigation can be approached through several methods, ranging from built-in software features to dedicated security solutions. The choice often depends on the sensitivity of the documents, the volume of files, and the existing IT infrastructure.
Using Built-in PDF Software Features
Most professional PDF editing software, like Adobe Acrobat Pro, offers robust security features. You can set passwords for opening documents, restrict printing and editing, and even apply digital signatures. Setting a strong password—one that is complex and unique—is the first line of defense. For editing restrictions, you'll typically set a separate password to prevent modifications, ensuring the document's integrity.
Leveraging Third-Party Tools
Beyond standard PDF editors, specialized software and online tools can enhance security. Some platforms offer batch encryption, watermarking, and advanced access control features tailored for legal workflows. When using online tools, however, due diligence regarding their data privacy policies and security protocols is crucial, especially for highly confidential legal case file security.
Advanced Security Techniques
For particularly sensitive or high-stakes litigation, standard password protection might not suffice. Advanced techniques can provide layered security and more granular control over document access and usage. These methods are often employed when dealing with extremely confidential information or when preparing for complex e discovery processes.
Digital Signatures and Certificates
Digital signatures provide a verifiable way to authenticate the sender of a document and ensure that the content has not been altered since it was signed. This is achieved using digital certificates, which are unique identifiers issued by trusted Certificate Authorities. Implementing digital signatures adds a layer of trust and non-repudiation to your legal documents.
Access Control and Permissions Management
More sophisticated solutions allow for granular permission settings. This can include time-limited access, restrictions based on user roles, or even document expiry dates. Such controls are invaluable in managing document sharing among large teams or opposing counsel, ensuring that access is granted only for the necessary duration and purpose.
Ongoing Best Practices
PDF security isn't a one-time setup; it's an ongoing process that requires consistent vigilance and adherence to best practices. Regularly reviewing security protocols and educating team members are vital components of maintaining a secure digital environment for legal documents.
Regularly update your software to ensure you have the latest security patches. Educate your team on the importance of strong password hygiene and the risks associated with sharing sensitive documents. Implement clear policies for document handling and retention to maintain compliance and security throughout the litigation lifecycle. This holistic approach is key to effective pdf security litigation.
Comparison Table: PDF Security Methods for Litigation
| Method | Ease of Use | Security Strength | Cost | Best For |
|---|---|---|---|---|
| Built-in PDF Software (e.g., Adobe Acrobat Pro) | Moderate | AES-128/256 Encryption, Password Protection | Varies (often subscription-based) | Individual documents, standard protection needs |
| Third-Party Desktop Software | Moderate to High | Advanced Encryption, Batch Processing, Watermarking | One-time purchase or subscription | High volume, specialized security features |
| Online PDF Security Tools | High | Varies (check provider's encryption standard) | Free to Paid (freemium models common) | Quick, simple tasks, non-critical documents (use with caution for sensitive data) |
| Digital Signatures/Certificates | Moderate (requires setup) | Authentication, Integrity Verification, Non-repudiation | Varies (certificate costs) | Authenticating document origin and integrity |
| Enterprise Document Management Systems (EDMS) | High (with training) | Robust Access Control, Auditing, Encryption, Version Control | High (enterprise-level cost) | Comprehensive legal case file security, large teams, regulatory compliance |