The legal profession hinges on trust and confidentiality. As legal professionals, we handle extremely sensitive information daily – client case files, financial records, personal details, and proprietary business strategies. The secure transfer and sharing of these documents are not just a matter of good practice; they are a fundamental ethical and legal obligation. A breach can lead to devastating consequences, including severe financial penalties, reputational damage, and the loss of client trust that takes years to rebuild.
With cyber threats becoming increasingly sophisticated, relying on outdated or insecure methods for sharing critical legal documents is no longer an option. It's imperative that law firms adopt robust solutions designed to protect sensitive data throughout the entire sharing process. This involves understanding the risks and implementing appropriate safeguards.
Table of Contents
Understanding the Risks of Insecure Sharing
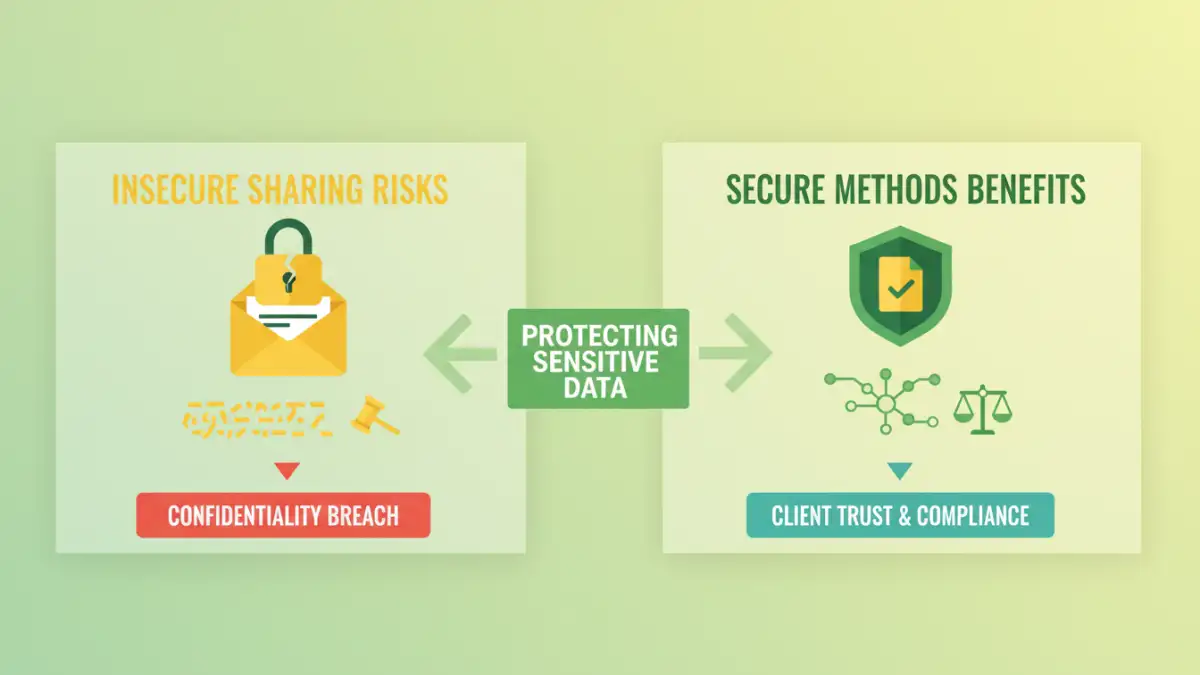
Many common methods of document transfer, like standard email attachments, unencrypted cloud storage links, or physical media, pose significant security risks. These methods often lack the necessary encryption or access controls, making them vulnerable to interception by unauthorized parties. Even seemingly minor oversights can create gaping holes in your firm's security posture.
Common Vulnerabilities
Email is a prime example; messages can be intercepted in transit, and attachments can be easily forwarded without the sender's knowledge. Public cloud storage services, while convenient, might not offer the granular control or end-to-end encryption required for sensitive legal documents. This lack of robust protection can inadvertently expose client information, leading to potential malpractice claims and regulatory violations.
Methods for Secure Document Sharing
Fortunately, several effective strategies and technologies are available to ensure confidential document transfer. These methods provide layers of security, including encryption, access controls, and audit trails, giving legal professionals peace of mind.
Encrypted Email and Messaging
Using end-to-end encrypted email services or secure messaging platforms ensures that only the intended recipient can read the content. These tools often employ strong encryption algorithms to protect data both in transit and at rest. Some platforms also offer features like message self-destruction and secure file attachments.
Secure File Transfer Protocols (SFTP) and VPNs
For more technical users or firms with IT infrastructure, SFTP provides a secure channel for transferring files over a network. Coupled with a Virtual Private Network (VPN), it creates a highly secure, encrypted tunnel for all data transmission, shielding it from external snooping. This is a robust option for transferring large or exceptionally sensitive files.
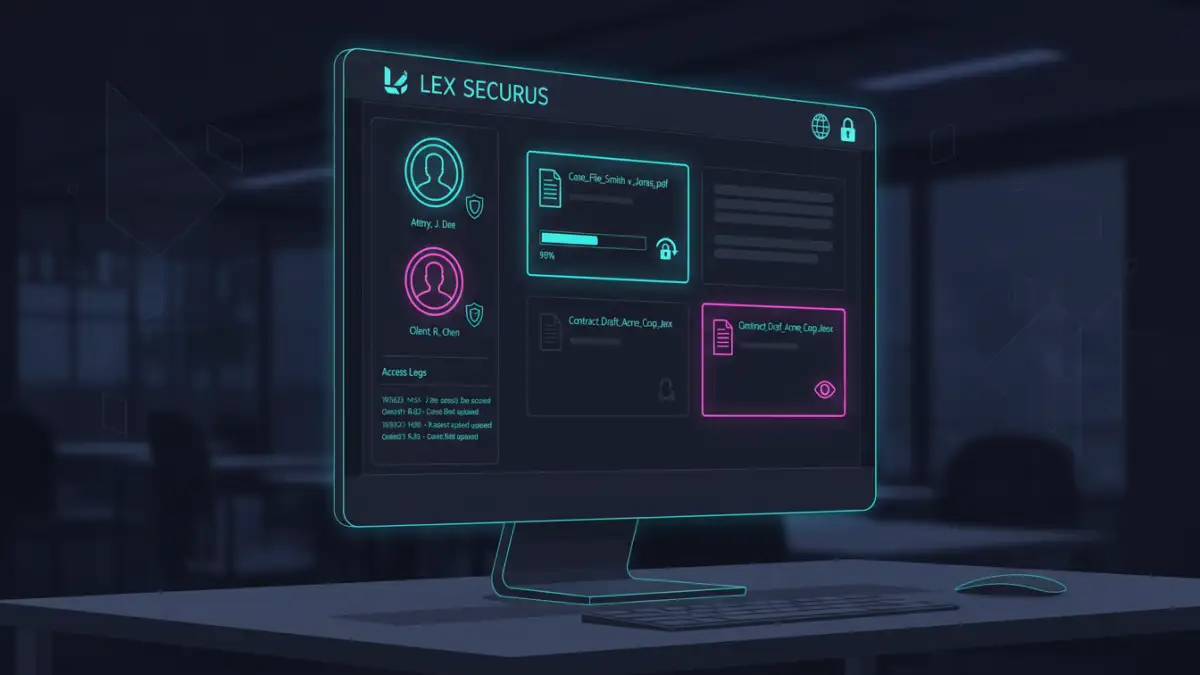
Dedicated Secure Collaboration Platforms
Many specialized platforms are designed for law firm secure collaboration. These often integrate document management, secure messaging, client portals, and encrypted file sharing into a single, user-friendly interface. They typically offer granular permissions, audit logs, and compliance features tailored to the legal industry.
Choosing the Right Solution
Selecting the appropriate secure document sharing method depends on your firm's specific needs, size, budget, and technical capabilities. It's crucial to evaluate potential solutions based on their security features, ease of use, integration capabilities, and compliance certifications.
Key Features to Consider
Look for features such as end-to-end encryption, multi-factor authentication (MFA), granular access controls (e.g., view-only, edit, download permissions), audit trails that log all activity, and data retention policies. Client portals can also significantly enhance communication and file exchange with clients, ensuring a controlled environment.
Best Practices for Law Firms
Beyond implementing specific technologies, establishing clear policies and procedures for document sharing is vital. Regular training for all staff on data security protocols and the proper use of chosen tools is essential to maintain a strong security posture. Promptly updating software and security patches also prevents known vulnerabilities from being exploited.
I’ve seen firsthand how a simple, consistent approach to secure document sharing can prevent major headaches. For instance, training paralegals to always use the firm's designated secure portal for client document uploads, rather than personal cloud links, drastically reduces the risk of accidental exposure. It’s about building a culture of security.
Comparison Table: Document Sharing Methods for Law Firms
| Method | Key Security Features | Ease of Use | Cost | Best For |
|---|---|---|---|---|
| Standard Email | None (inherently insecure) | Very High | Free | Non-sensitive internal memos only |
| Encrypted Email/Messaging | End-to-end encryption, secure transit | Moderate | Varies (free to paid) | Sensitive emails, quick document snippets |
| Secure File Transfer (SFTP/VPN) | Strong encryption, secure tunnel | Low to Moderate (requires setup) | Varies (server costs, software) | Large files, bulk transfers, IT-managed |
| Secure Collaboration Platforms | MFA, access controls, audit logs, encryption | High | Paid (subscription) | Comprehensive law firm collaboration, client portals |