
The chilling moment you realize your critical files are inaccessible, locked behind an unknown encryption, is a scenario many dread. Recently, I was part of a team that faced this exact challenge after a sophisticated ransomware attack. The attackers demanded a hefty sum, but our focus immediately shifted from payment to recovery. This wasn't just about retrieving data; it was about validating our preparedness and executing a robust defense strategy.
Our mission was clear: bypass the encryption and restore normal operations without succumbing to the attackers' demands. This required a multi-pronged approach, combining technical expertise, diligent investigation, and leveraging every available resource. The success we achieved serves as a testament to proactive cybersecurity measures and swift, decisive action.
Table of Contents
Understanding the Ransomware Threat
Ransomware attacks have become a pervasive threat, targeting individuals and organizations alike. These malicious programs encrypt a victim's files, rendering them unusable until a ransom is paid. The attackers often employ strong encryption algorithms, making manual decryption virtually impossible without the unique decryption key.
The Anatomy of an Attack
Understanding how these attacks unfold is the first step in combating them. Typically, ransomware enters a system through phishing emails, malicious downloads, or exploiting software vulnerabilities. Once inside, it spreads rapidly, encrypting files across networks. The attackers then display a ransom note, detailing the amount and method of payment, usually in cryptocurrency.
Initial Assessment and Containment

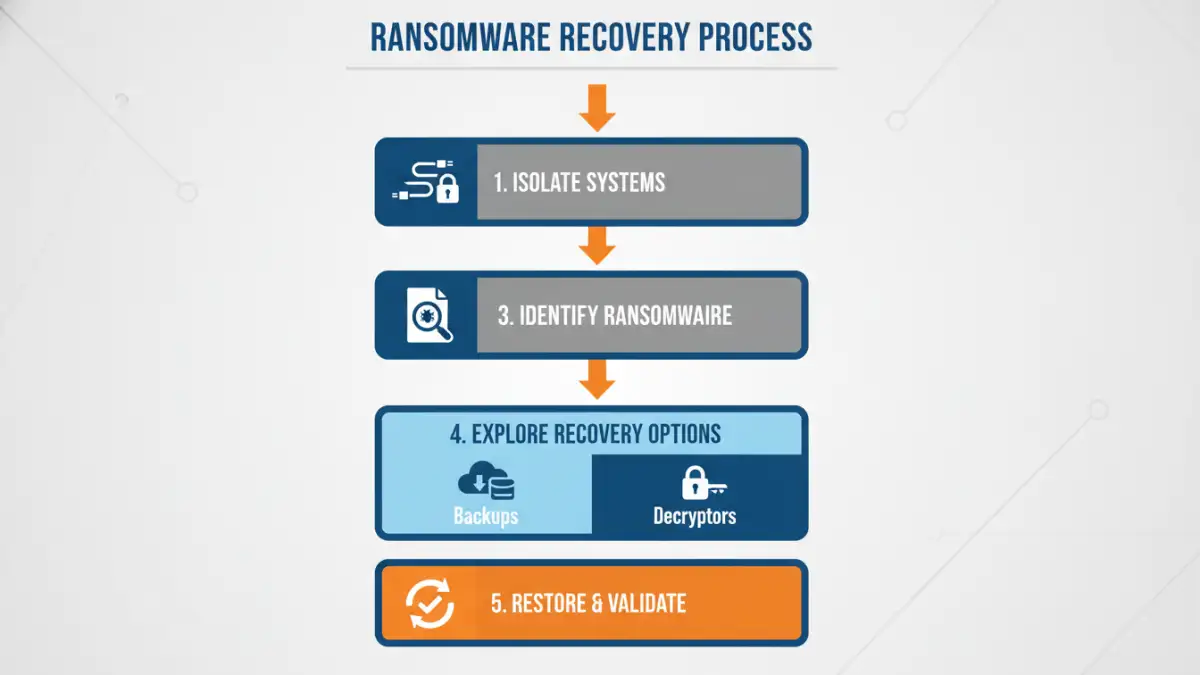
Upon detecting the ransomware, our immediate priority was to contain the spread. This involved isolating infected systems from the network to prevent further encryption or lateral movement by the malware. We meticulously documented the ransomware strain and its behavior, gathering crucial intelligence for the subsequent recovery phase.
Identifying the initial point of entry was critical for understanding the attack vector and preventing future breaches. This investigation often involves analyzing logs, network traffic, and endpoint data. Containment is a delicate balance; it must be swift to limit damage but thorough enough to ensure the threat is truly neutralized.
Recovery Strategies Employed
With the network secured, we shifted our focus to encrypted file recovery. Our strategy revolved around several key pillars: backups, known vulnerabilities, and specialized tools. We explored every avenue to restore data without paying the ransom, which is generally advised against as it doesn't guarantee file recovery and encourages further criminal activity.
Leveraging Backups
The most reliable method for ransomware file recovery is restoring from clean, verified backups. We immediately initiated a process to test our recent backup integrity. This involved restoring a sample set of files to an isolated environment to ensure they were not corrupted or infected.
Exploring Decryption Tools
For cases where backups were insufficient or unavailable, we investigated publicly available decryption tools. Many cybersecurity firms and researchers work tirelessly to develop free decryptors for known ransomware variants. This often involves reverse-engineering the malware and identifying weaknesses in its encryption implementation.
Technical Aspects of Encrypted File Recovery
The technical execution of encrypted document rescue requires a deep understanding of file systems, encryption protocols, and malware analysis. When a ransomware attack occurs, the primary challenge is accessing files that have been rendered unintelligible by the encryption process. Our team meticulously analyzed the specific ransomware variant to determine the encryption method used.
Data Forensics and Analysis
We performed thorough data forensics on affected systems. This involved examining file metadata, identifying encryption patterns, and searching for any residual unencrypted data or temporary files that the ransomware might have overlooked. Understanding the encryption keys, or lack thereof, was paramount.
System Restoration and Validation
Once we had a viable recovery method—whether from backups or a decryption tool—the next phase was system restoration. This involved rebuilding affected systems, patching vulnerabilities, and carefully migrating recovered data. Each restored file was then validated to ensure its integrity and usability, confirming our data breach recovery success.
Prevention and Lessons Learned
This incident underscored the vital importance of a robust, multi-layered cybersecurity strategy. Proactive measures are far more effective and less costly than reactive recovery efforts. Regular security audits, employee training, and up-to-date endpoint protection are non-negotiable.
The key takeaway is that while ransomware attacks are daunting, they are not always insurmountable. A well-prepared organization with a solid incident response plan stands a much better chance of achieving ransomware file recovery and minimizing business disruption. This cybersecurity success story highlights the power of preparedness and expertise.
Comparison Table: Ransomware Recovery Methods
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Restoring from Backups | Most reliable, no cost if backups are current | Requires regular, verified backups; potential data loss since last backup | Organizations with strong backup policies |
| Using Decryption Tools | Free, can recover data without paying ransom | Only available for specific ransomware variants; may not always work perfectly | Known ransomware strains with available decryptors |
| Paying the Ransom | Potential to get files back (no guarantee) | Encourages cybercrime, no guarantee of recovery, financial loss, potential legal issues | Last resort when data is irreplaceable and no other options exist |
| Professional Data Recovery Services | Expertise, can handle complex cases | Can be expensive, time-consuming | Severely damaged or complex encryption scenarios |