
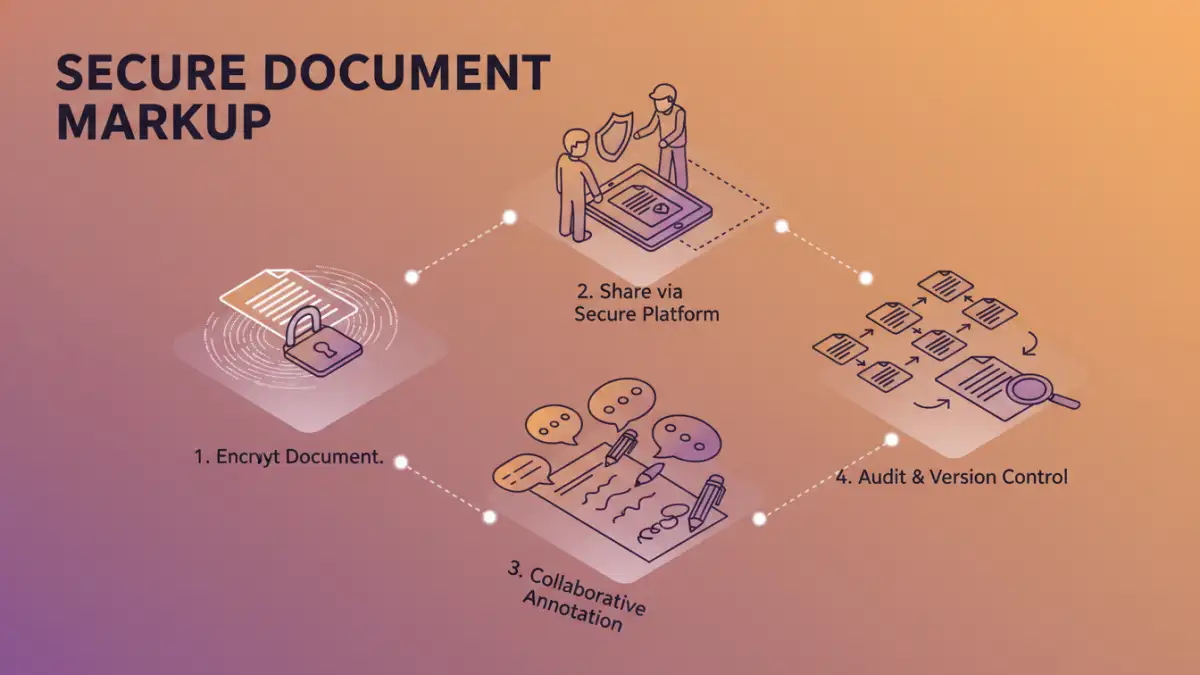
Working with sensitive documents often presents a unique challenge: how do you enable seamless collaboration while maintaining stringent security? I've seen firsthand how teams struggle to balance the need for quick feedback and annotations with the absolute necessity of protecting confidential information. It's a delicate dance, especially when dealing with PDFs that hold critical data.
Table of Contents
Understanding the Core Challenge: Balancing Security and Collaboration
The digital age demands constant information exchange, but this often conflicts directly with the need for data privacy and integrity. My journey in software engineering has taught me that overlooking security in collaboration is a common, and often costly, mistake. It requires a thoughtful approach to safeguard sensitive data.
The Risks of Insecure Sharing
Sharing unencrypted or poorly protected PDFs can lead to data breaches, compliance violations, and significant reputational damage. Simple email attachments or cloud links without proper access controls are significant vulnerabilities. It's not just about unauthorized viewing; the potential for data manipulation is also a serious concern that must be addressed.
Why Standard PDF Tools Fall Short
Many basic PDF viewers offer annotation features but lack robust security protocols. They might allow markups but don't inherently protect the underlying document or track changes securely. This gap necessitates a more specialized approach for effective secure document markup, ensuring both functionality and protection.
Key Features for Secure PDF Markup

Effective collaboration on secure documents requires specific features beyond basic annotation. These tools ensure that while teams work efficiently, the document's integrity and confidentiality remain uncompromised. Identifying these essential features is crucial for selecting the right solution for your organization.
Encryption and Access Control
Robust encryption is non-negotiable for any sensitive document. This includes strong password protection, certificate-based encryption, and granular permission settings that define who can view, edit, or annotate the document. These controls are vital for preventing unauthorized access, even if the file is somehow intercepted.
Audit Trails and Versioning
A comprehensive audit trail logs every action taken on the document, detailing who accessed it, when, and what changes were made. Version control is equally vital, allowing teams to track revisions, revert to previous states, and understand the evolution of the document. This transparency is key for accountability and maintaining data integrity throughout the collaboration process.
Strategies for Collaborative PDF Annotation
Once the foundational security features are understood, implementing practical strategies for collaborative PDF annotation becomes the next step. There are several effective approaches, each with its own advantages depending on the team's size, budget, and specific security requirements. Choosing the right method is crucial for seamless, secure workflows.
Utilizing Cloud-Based Solutions
Platforms like Adobe Acrobat, Foxit PhantomPDF, or specialized secure document collaboration tools often provide cloud-based environments. These allow real-time team document markup with built-in encryption and access controls. The convenience of cloud access combined with centralized security management can streamline workflows significantly, enhancing both efficiency and security.
Desktop Software Approaches
For organizations with stricter data residency requirements or a preference for offline work, desktop software remains a strong option. Many professional PDF editors offer robust security features, allowing documents to be encrypted and marked up locally before secure sharing. This method provides greater control over the document's lifecycle and data handling.
Implementing Best Practices for Secure Document Sharing
Technology alone isn't enough to guarantee security; procedural best practices are essential to fully leverage secure document markup capabilities. Adopting a security-first mindset across the team ensures that the tools are used effectively and consistently, creating a robust defense against potential threats.
Regular Security Audits and Training
Periodically auditing your document sharing processes helps identify and rectify potential vulnerabilities proactively. Coupled with regular user training on secure practices, this creates a strong human firewall. Educating team members about phishing, strong passwords, and proper access request procedures is paramount for maintaining a secure environment.
Secure Communication Channels
Always use secure, encrypted channels for sharing links to secure documents, or for exchanging passwords if absolutely necessary (though sharing passwords should be avoided if possible). Avoid sending sensitive information via unencrypted email or insecure messaging apps. Implementing multi-factor authentication for access to collaboration platforms further enhances overall security, adding an extra layer of protection.
Secure PDF Collaboration Tools Comparison
| Feature | Basic PDF Editor | Dedicated Secure PDF Platform | Cloud-Based Collaboration Suite |
|---|---|---|---|
| Encryption Level | Basic (password) | Advanced (certificate, granular) | Advanced (platform-wide) |
| Access Control | Limited (file password) | Granular (user/role-based) | Granular (project/team-based) |
| Audit Trails | None or very basic | Comprehensive (activity logs) | Comprehensive (version history, user actions) |
| Real-time Markup | No | Yes (often) | Yes (standard) |
| Cost | Low to moderate | Moderate to high subscription | Moderate to high subscription |
| Compliance Support | Minimal | Strong (HIPAA, GDPR, etc.) | Strong (various industry standards) |