
I recently reviewed an API integration for a critical financial application, and the documentation for its file upload endpoint was, to put it mildly, a minefield. Details about authentication were scattered, encryption methods were vaguely described, and error responses were practically non-existent. This experience highlighted a fundamental truth: without clear, comprehensive secure file API documentation, even the most robust security measures can be undermined by developer confusion and misuse.
As a software engineer with over a decade in the field, I’ve seen firsthand how crucial well-structured API documentation is, especially when dealing with sensitive file operations. It's not just about listing endpoints; it's about providing a roadmap for secure interaction, ensuring that developers can integrate confidently and correctly, thereby bolstering overall system security.
Table of Contents
Understanding the Imperative of Clear Documentation

Poorly documented API endpoints, particularly those handling files, are a significant liability. They can lead to incorrect implementations, security vulnerabilities, and a frustrating developer experience. When developers struggle to understand how to interact with your API securely, they might inadvertently introduce weaknesses or abandon the API altogether.
For secure file API documentation, clarity isn't just a convenience; it's a security feature. It ensures that consumers understand the expected security protocols, the data formats, and the potential pitfalls, reducing the attack surface by minimizing guesswork and misinterpretation.
Why Secure File APIs Demand Precision
File-related APIs often involve transferring and storing sensitive data, making them prime targets for malicious actors. Any ambiguity in how authentication tokens are passed, how data should be encrypted, or what validation rules apply can open doors for data breaches, compliance violations, and reputational damage. Precision in your documentation guides developers to implement secure integrations from the start.
I recall a project where an external team misinterpreted file size limits due to unclear documentation, leading to unexpected server load and denial-of-service vulnerabilities. Clear specifications on every aspect, from headers to payload, are non-negotiable for `file security api` endpoints.
Core Principles for Secure File API Documentation
Effective documentation for secure file APIs adheres to several core principles. These principles ensure that all critical security-related information is present, easily accessible, and unambiguous. It’s about being explicit about every step a developer needs to take to interact safely with your service.
Prioritizing these principles during the documentation process transforms it from a mere reference guide into a powerful tool for maintaining `api docs security` and developer trust.
Authentication and Authorization
This is where many documentation efforts fall short. Your documentation must clearly detail the authentication mechanisms (e.g., OAuth 2.0, API keys, JWTs), how tokens are acquired, refreshed, and used in requests. Furthermore, it needs to specify authorization rules: which roles or permissions are required to access specific file operations (upload, download, delete) and under what conditions.
Provide explicit examples for passing authentication headers and handling authorization failures. Explain the lifecycle of access tokens and refresh tokens, including expiration and revocation policies. This clarity helps prevent common mistakes like hardcoding credentials or using expired tokens, which can expose vulnerabilities.
Data Handling and Encryption
When dealing with files, especially sensitive ones, it's paramount to document how data is handled throughout its lifecycle. This includes outlining encryption standards for data in transit (e.g., TLS versions, cipher suites) and at rest (e.g., AES-256, key management practices). Developers need to know if they are responsible for client-side encryption or if the API handles it.
Additionally, specify data retention policies, anonymization processes, and any legal or compliance requirements (e.g., GDPR, HIPAA) that impact file storage and access. Documenting input validation rules, such as allowed file types, maximum file sizes, and content scanning for malware, is also critical to prevent malicious uploads.
Structuring Your API Documentation
Even with great content, poor structure can make documentation unusable. A logical and consistent structure allows developers to quickly find the information they need, reducing frustration and the likelihood of errors. Think of it as designing a user interface for your information.
Tools like OpenAPI/Swagger are invaluable here, providing a standardized format that can generate interactive documentation. However, even with these tools, thoughtful content organization is key to truly `clear api docs`.
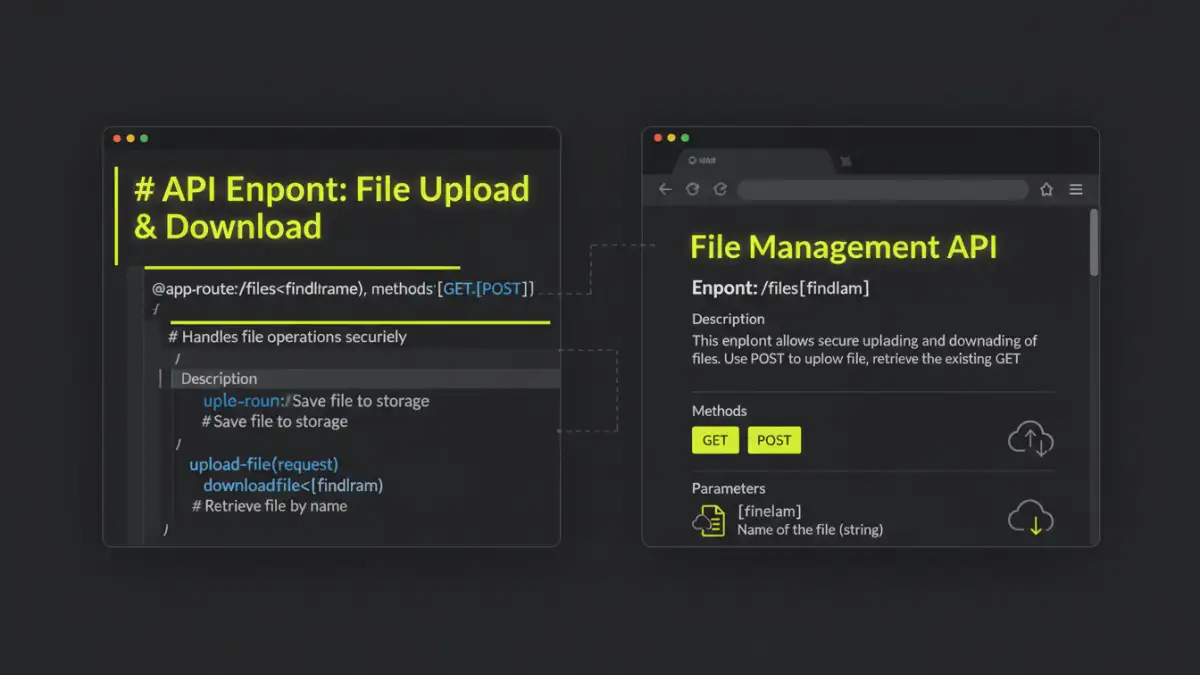
Endpoint-Specific Details
Each file-related endpoint (e.g., /files/upload, /files/{id}/download) should have its own dedicated section. This section must include:
- HTTP Method: (e.g., POST, GET, DELETE)
- URL Path: With clear examples of path parameters.
- Request Headers: Required headers, especially for authentication and content type.
- Request Body: Schema for multipart/form-data, including field names, types, and descriptions for the file itself and any associated metadata.
- Response Codes: All possible HTTP status codes (200 OK, 201 Created, 400 Bad Request, 401 Unauthorized, 403 Forbidden, 404 Not Found, 500 Internal Server Error) with descriptions and example response bodies.
- Example Usage: Practical code snippets in multiple languages (Curl, Python, Node.js) demonstrating a complete, secure interaction.
Error Handling and Response Codes
One of the most overlooked aspects of API documentation is comprehensive error handling. Developers need to know what to expect when things go wrong and how to recover. Document all possible error codes, their meanings, and the structure of error response bodies. Differentiate between client-side errors (4xx) and server-side errors (5xx).
Provide guidance on common error scenarios specific to file operations, such as file size limits exceeded, unsupported file types, or corrupted uploads. Clear error messages and documentation reduce debugging time and help developers build more resilient applications.
Best Practices for Clarity and Maintainability
Creating excellent documentation isn't a one-time task; it's an ongoing commitment. To ensure your `secure file api documentation` remains accurate and useful, integrate it into your development lifecycle. Treat documentation as a first-class citizen, just like your code.
Regular reviews, automated checks, and a feedback loop with API consumers are essential for maintaining high-quality documentation that truly serves its purpose.
Version Control and Changelogs
Your API, and consequently its documentation, will evolve. Implement version control for your documentation, linking it directly to your API versions. Every API change, no matter how minor, that affects how developers interact with file endpoints should be reflected in the documentation. A detailed changelog or release notes section is critical.
Clearly communicate deprecations, new features, and breaking changes. This proactive approach prevents developers from encountering unexpected behavior and ensures they can adapt their integrations smoothly, maintaining the integrity of their applications.
Key Documentation Elements for Secure File APIs
| Element | Description | Security Impact | Clarity Benefit |
|---|---|---|---|
| Authentication Methods | How users/systems prove identity to the API. | Prevents unauthorized access and impersonation. | Clear access instructions for developers. |
| Authorization Rules | What authenticated users/systems are permitted to do. | Prevents privilege escalation and data misuse. | Defines the scope of actions for each role/permission. |
| Encryption Details | Standards for data in transit and at rest. | Protects data confidentiality and integrity. | Assures developers of data security measures. |
| Input Validation | Rules for accepted file types, sizes, and content. | Prevents malicious uploads, injection attacks, and resource exhaustion. | Reduces error rates and guides proper data submission. |
| Error Codes | Specific HTTP status codes and custom error messages. | Helps developers understand and respond to failures. | Faster debugging and more resilient application design. |