
When transferring sensitive information across borders, understanding and adhering to international laws on secure file sharing is not just good practice; it's a legal necessity. My experience has shown that many organizations, especially smaller ones, often overlook the intricate web of regulations that govern data movement. This can lead to significant penalties and reputational damage.
The landscape of data privacy and security is constantly evolving, with different countries and regions implementing their own stringent rules. Navigating these can be a daunting task, but it's crucial for maintaining trust and ensuring the integrity of shared data. This guide aims to shed light on the key considerations for compliant secure file sharing.
Table of Contents
Understanding the Regulatory Landscape
The core principle behind most international laws on data handling is the protection of individual privacy and sensitive corporate information. Regulations typically focus on how data is collected, processed, stored, and, crucially, transferred. Each jurisdiction has its unique approach, but common themes emerge regarding consent, data minimization, security measures, and breach notification.
Failure to comply can result in substantial fines, legal action, and a loss of customer confidence. For businesses operating globally, this means a one-size-fits-all approach to file sharing is rarely sufficient. A nuanced understanding of the legal file transfer requirements in each region of operation is paramount.
Scope of Data Protection Laws
These laws often apply not only to personal data but also to confidential business information, intellectual property, and financial records. The definition of 'sensitive' can vary, but generally includes anything that, if compromised, could lead to harm, discrimination, or financial loss.
Key International Regulations to Know

While a comprehensive list is extensive, several landmark regulations significantly shape global data security practices. Understanding these provides a solid foundation for developing compliant file sharing protocols.
General Data Protection Regulation (GDPR)
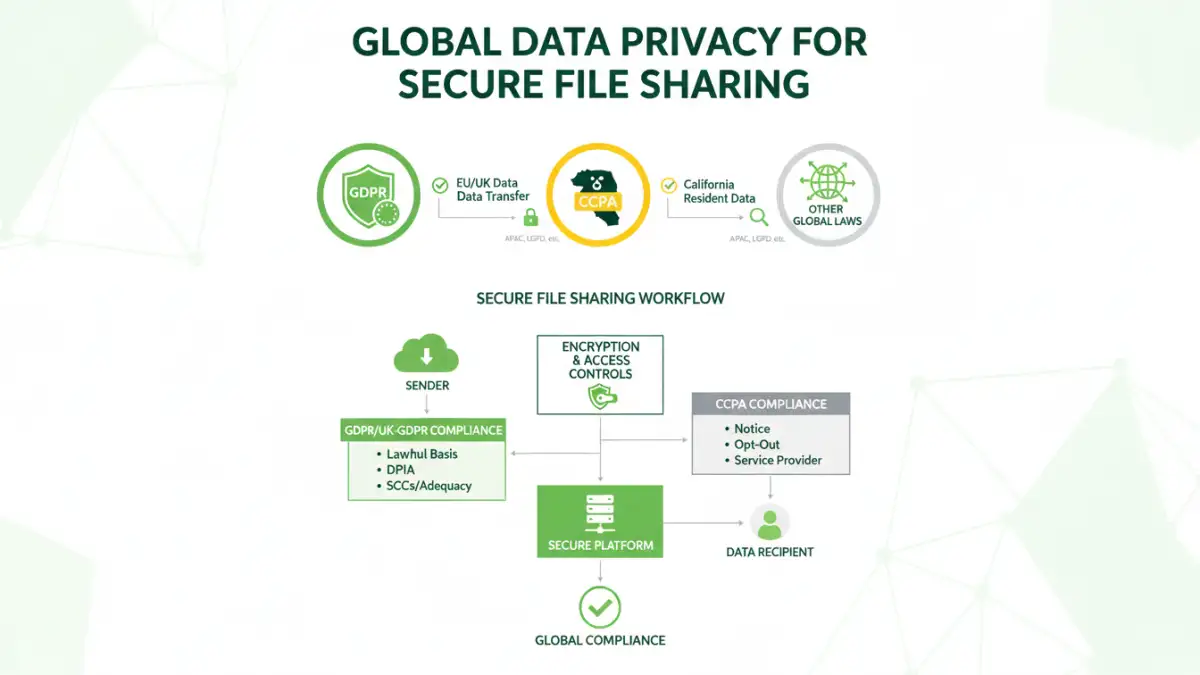
The GDPR, enacted by the European Union, is one of the most comprehensive data protection laws globally. It imposes strict rules on how personal data of EU residents is processed and transferred, regardless of where the processing entity is located. Key requirements include explicit consent, data subject rights, and robust security measures.
For secure file sharing, GDPR mandates that any transfer of personal data outside the EU must be protected by appropriate safeguards, such as standard contractual clauses or adequacy decisions. This directly impacts how companies share documents containing EU citizens' personal information.
California Consumer Privacy Act (CCPA)
In the United States, the CCPA (and its subsequent amendment, the CPRA) grants California consumers significant rights regarding their personal information. While not as broad as GDPR in scope, it still imposes obligations on businesses concerning data collection, sale, and security, influencing how files containing California resident data are shared.
Other Regional and National Laws
Beyond GDPR and CCPA, numerous other laws exist, such as Brazil's LGPD (Lei Geral de Proteção de Dados), Canada's PIPEDA (Personal Information Protection and Electronic Documents Act), and various national security directives. Each has specific stipulations that must be considered when sharing files internationally.
Implementing Secure File Sharing Practices
Adopting a proactive approach to secure file sharing is essential. This involves implementing technical, organizational, and legal safeguards to protect data throughout its lifecycle.
Encryption is a cornerstone of secure file sharing. Both data in transit (when files are being sent) and data at rest (when files are stored) should be protected. Using strong, up-to-date encryption algorithms ensures that even if data is intercepted, it remains unreadable without the decryption key.
Access controls are equally vital. Implementing the principle of least privilege ensures that only authorized personnel can access specific files. Role-based access and regular audits of permissions help prevent unauthorized disclosure.
Cross-Border Data Transfer Considerations
Sharing files across international borders introduces complex compliance challenges. It's not just about sending a file; it's about ensuring the destination country's legal framework adequately protects the data being transferred.
Many regulations require that data transferred internationally be afforded a level of protection essentially equivalent to that within the originating jurisdiction. Organizations must therefore assess the data protection laws of the recipient country. This often involves contractual agreements like Standard Contractual Clauses (SCCs) or relying on data adequacy decisions made by regulatory bodies.
For instance, when sharing a PDF containing sensitive client information from the UK to the US, one must consider the UK GDPR and the US’s patchwork of federal and state privacy laws. This assessment dictates the appropriate legal mechanisms for the transfer.
Tools and Solutions for Compliance
Leveraging the right technology can significantly simplify adherence to secure file sharing laws. Secure file transfer platforms often incorporate features designed for compliance.
These platforms typically offer end-to-end encryption, granular access controls, audit trails, and compliance certifications. Many also provide tools for managing consent and data subject requests, helping organizations meet their legal obligations efficiently. Choosing a solution that supports international sharing compliance is key.
| Feature | Description | Compliance Benefit | Considerations |
|---|---|---|---|
| End-to-End Encryption | Data is encrypted from sender to receiver, unreadable by intermediaries. | Protects data confidentiality during transit and at rest. | Key management is crucial; ensure strong algorithms are used. |
| Access Controls & Permissions | Granular control over who can view, edit, or download files. | Enforces the principle of least privilege, reducing unauthorized access. | Regular review and updates of permissions are necessary. |
| Audit Trails | Logs all file access, download, and sharing activities. | Provides accountability and evidence of compliance, aiding in breach investigations. | Ensure logs are securely stored and tamper-proof. |
| Data Residency Options | Allows choosing the physical location where data is stored. | Helps comply with national data localization requirements. | May impact performance or cost depending on server locations. |
| Compliance Certifications | Third-party validation of security and privacy standards (e.g., ISO 27001, SOC 2). | Demonstrates commitment to security and helps meet regulatory demands. | Certifications vary in scope; verify relevance to specific laws. |