
Working with sensitive documents often necessitates robust protection, especially when they cross borders or are shared widely. Ensuring that these digital assets remain confidential and unaltered is paramount, not just for business continuity but also for legal and ethical compliance. My experience has shown me that simply applying a password isn't always enough; understanding the underlying encryption methods and global standards is crucial for true document security.
The digital landscape demands that we consider how information is protected, not just locally but on a global scale. This involves navigating a complex web of regulations, accepted practices, and technological capabilities. For PDFs, which are ubiquitous for sharing documents, this means understanding the encryption mechanisms that safeguard their content and the international frameworks that govern their use.
Table of Contents
Core Principles of PDF Encryption
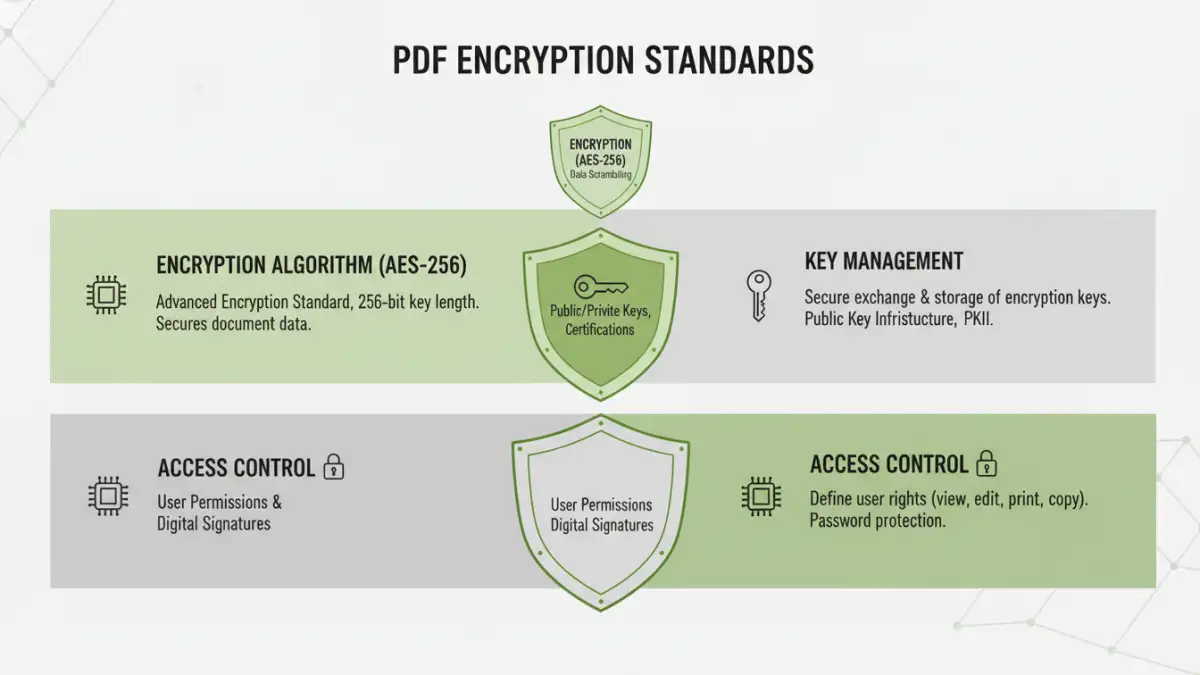
At its heart, PDF encryption involves using algorithms to scramble the document's content, rendering it unreadable without a specific key or password. This process ensures confidentiality, preventing unauthorized parties from accessing sensitive information. Modern PDF encryption typically employs symmetric encryption, where the same key is used for both encrypting and decrypting the data.
Encryption Algorithms and Key Management
The strength of PDF encryption hinges on the algorithms used. Advanced Encryption Standard (AES), particularly AES-128 and AES-256, is the current gold standard, offering a high degree of security against brute-force attacks. Effective key management, which includes how passwords are used to derive encryption keys and how those keys are protected, is equally vital for maintaining security. A weak password can undermine even the strongest encryption.
Key Global Encryption Standards
While specific implementations can vary, several international standards and recommendations guide the use of encryption for documents. These standards aim to ensure interoperability, security, and compliance across different jurisdictions. Adhering to these recognized protocols is essential for businesses operating in a globalized environment.
AES and Its Variants
The Advanced Encryption Standard (AES) is an internationally recognized symmetric encryption algorithm approved by the U.S. government and widely adopted worldwide. PDF specifications often support AES-128 and AES-256 bit encryption. These standards provide a robust level of security, making it computationally infeasible for unauthorized individuals to decrypt the data without the correct key.
Public-Key Cryptography (PKC) in PDFs
While symmetric encryption is used for the bulk of the document data, Public-Key Cryptography (PKC) plays a role in managing the keys, especially in enterprise settings. This often involves digital signatures and certificates, which not only secure the content but also verify the sender's identity and ensure document integrity. This is crucial for secure PDF sharing globally.
Implementing Secure PDF Sharing
Protecting PDFs goes beyond just encrypting the file. It involves a holistic approach to how documents are created, shared, and managed. When I've worked on projects requiring high levels of security, we always considered the entire lifecycle of the document.
Using PDF Software Features
Most professional PDF editing software, like Adobe Acrobat Pro or alternatives, offers built-in encryption features. These tools allow users to set passwords for opening the document, restrict printing or editing, and apply encryption standards like AES-256. It’s important to select the highest level of encryption supported by the software and the user's needs.
Secure Sharing Platforms
For critical documents, relying solely on password-protected PDFs might not be sufficient, especially when considering cross-border data security. Utilizing secure file-sharing platforms that offer end-to-end encryption, access controls, audit trails, and compliance certifications can provide an additional layer of security and manageability. These platforms are designed to handle sensitive data transfer more effectively.
Navigating Document Encryption Compliance
Different countries and industries have specific regulations concerning data privacy and security, which directly impact how documents must be protected. Understanding these requirements is critical for avoiding legal penalties and maintaining trust with clients and partners.
GDPR and CCPA Considerations
Regulations like the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) mandate strict rules for handling personal data. For organizations dealing with sensitive information in PDF format, this means implementing appropriate technical and organizational measures, including strong encryption, to protect data during transit and at rest. Document encryption compliance is no longer optional.
Industry-Specific Regulations
Sectors like healthcare (HIPAA), finance, and government have their own stringent requirements for data security. These often dictate specific encryption protocols, key management practices, and auditing procedures that must be followed. Ensuring that your PDF encryption methods meet these specific international encryption laws is paramount.
Best Practices for Global Data Security
Beyond technical standards and legal mandates, adopting a set of best practices can significantly enhance the security of your PDF documents when shared globally. These practices are born from practical experience in dealing with diverse security challenges.
Strong Password Policies
Enforce the use of strong, unique passwords for all encrypted documents. This means passwords should be long, complex, and not easily guessable. Educating users on password hygiene and considering the use of password managers can greatly improve security.
Regular Audits and Updates
Periodically review your encryption policies and practices. Ensure that the software and algorithms used are up-to-date with the latest security recommendations. Regularly auditing access logs for encrypted documents can also help detect potential breaches or unauthorized access attempts.
Comparison Table: PDF Protection Methods
| Method | Description | Security Level | Ease of Use | Best For |
|---|---|---|---|---|
| Password Protection (Standard) | Basic password to open PDF. | Low to Medium (depends on password strength) | Very High | Non-sensitive personal documents. |
| AES-128 Encryption | Industry-standard symmetric encryption. | High | High (via software) | Most business documents. |
| AES-256 Encryption | Stronger version of AES. | Very High | High (via software) | Highly sensitive corporate or personal data. |
| Digital Signatures & Certificates | Verifies sender and document integrity. | High (integrity & authenticity) | Medium (requires setup) | Contracts, official documents, secure PDF sharing globally. |
| Secure File Sharing Platforms | Cloud-based solutions with end-to-end encryption. | Very High | High | Collaborative work, cross-border data security, compliance needs. |