
Working with sensitive information requires robust security measures, and password-protected documents are a cornerstone of this. However, simply applying a password isn't always enough. Understanding who is accessing these files, when, and how often is crucial for maintaining security and compliance. This is where password protected document usage reports come into play, offering invaluable insights into your secure file management practices.
These reports go beyond basic encryption, providing a layer of oversight that helps identify potential vulnerabilities or misuse. For organizations handling confidential data, having visibility into document access is not just good practice; it's often a regulatory requirement. I've seen firsthand how a lack of oversight can lead to security breaches, making detailed usage reports a critical component of any comprehensive security strategy.
Table of Contents
What Are Password Protected Document Usage Reports?
A password protected document usage report is a log or summary that details the activity surrounding files secured with a password. This can include information like who attempted to open the document, the success or failure of those attempts, the timestamp of the activity, and potentially the IP address or system from which the access was made.
Essentially, these reports transform static security into dynamic oversight. They provide an audit trail, allowing administrators or authorized personnel to monitor access patterns and detect any anomalies. This level of detail is indispensable for organizations aiming for stringent access control and data governance.
Components of a Typical Report
A comprehensive usage report typically includes several key pieces of information. This includes the filename, the user who interacted with it, the date and time of the action, the type of action (e.g., opened, attempted to open, shared), and the outcome (success or failure). Some advanced systems might also log the duration of access or changes made to the document.
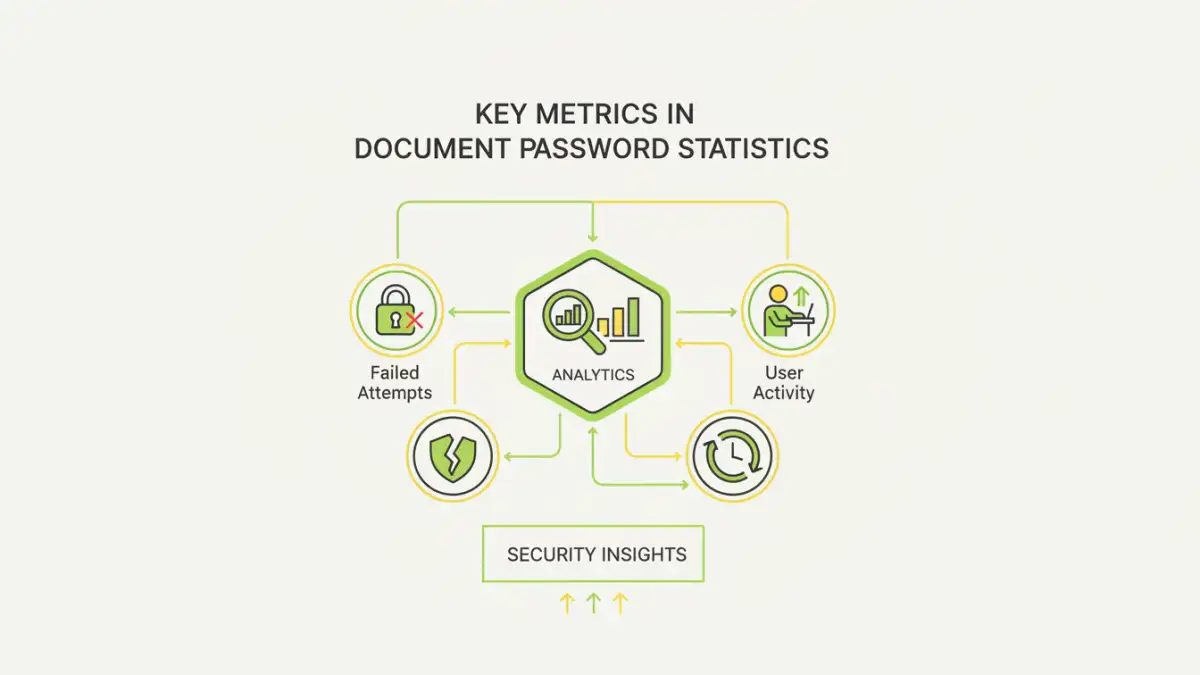
Key Metrics in Usage Reports

The value of these reports lies in the specific data points they capture. Understanding these metrics allows for better analysis of document security and user behavior. Tracking these document password statistics is vital for identifying trends and potential risks.
Some of the most critical metrics include successful access counts, failed access attempts, unique users accessing a document, and the frequency of access over a given period. A spike in failed attempts, for instance, could indicate brute-force attacks or unauthorized individuals trying to gain entry.
Analyzing Access Patterns
Regular analysis of these metrics can reveal important information. For example, if a document that is rarely accessed suddenly sees high activity, it might warrant further investigation. Conversely, if a critical document shows no access for an extended period, it could mean authorized users are not aware of its existence or its importance.
Benefits of Tracking Document Access
Implementing a system that generates usage reports for password protected documents offers numerous advantages. From enhanced security to meeting compliance mandates, the benefits are far-reaching for any organization.
The primary benefit is improved security. By monitoring access, you can quickly identify and respond to suspicious activity, preventing potential data breaches. This proactive approach is far more effective than reacting after a security incident has already occurred. It also aids in fulfilling compliance requirements, such as GDPR or HIPAA, which often mandate strict data access controls and audit trails.
Compliance and Auditing Support
Many industries are subject to regulations that require detailed logging of access to sensitive data. Usage reports provide the necessary audit trail to demonstrate compliance to regulatory bodies. This simplifies the auditing process and reduces the risk of penalties associated with non-compliance.
Implementing Usage Reporting
The method for generating these reports varies depending on the tools and systems you use. Many modern document management systems, cloud storage solutions, and specialized security software offer built-in reporting features for password protected files.
For documents protected using native features in applications like Microsoft Word or Adobe Acrobat, generating detailed usage logs might require third-party solutions or more advanced configuration. It's essential to choose a solution that integrates well with your existing workflow and provides the level of detail you need for effective secure file management.
Best Practices for Secure File Management
Beyond just implementing usage reports, a holistic approach to secure file management is key. This involves a combination of strong password policies, regular security audits, and user training.
Ensure that passwords are complex and changed regularly. Educate users on the importance of password security and the proper handling of sensitive documents. Regularly review the access control report data to identify any potential security gaps or policy violations. This continuous improvement cycle is vital for maintaining a secure environment.
Comparison Table: Methods for Document Security Reporting
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Native Application Features (e.g., MS Office, Adobe Acrobat) | Built-in, no extra cost. | Limited logging capabilities, often requires manual setup or specific versions. | Basic password protection, individual files. |
| Cloud Storage Services (e.g., Google Drive, OneDrive, Dropbox) | Centralized access logs, version history, collaboration features. | Reporting might be limited to administrator-level access, potential privacy concerns with cloud providers. | Team collaboration, shared access control. |
| Document Management Systems (DMS) | Comprehensive audit trails, granular access control, detailed usage reports. | Can be costly, requires implementation and management. | Enterprise-level security, regulatory compliance. |
| Third-Party Encryption Software | Advanced encryption, detailed logging, customizable reports. | May require additional software purchase and integration. | High-security environments, specific encryption needs. |