
Just last month, I was consulting with a medium-sized tech firm that suffered a significant data leak, not from an external hack, but from an unmonitored internal document sharing process. It was a stark reminder that even the most advanced perimeter defenses can be useless if internal document security risks are overlooked. Waiting for a breach to happen before evaluating your vulnerabilities is a costly mistake.
Understanding where your sensitive documents reside, who has access to them, and how they are protected is paramount. This isn't just about compliance; it's about safeguarding your intellectual property, customer trust, and operational continuity. Proactive assessment is the only way to truly protect your valuable information assets.
Table of Contents
The Silent Threat: Why Document Security Matters
Many organizations focus heavily on network security, firewalls, and endpoint protection. While crucial, this often leaves a blind spot: the documents themselves. Files containing sensitive data – from financial records and client contracts to proprietary code and employee information – are often the weakest link.
A single unencrypted spreadsheet or an improperly shared design document can expose your organization to immense harm. The consequences range from hefty regulatory fines and reputational damage to competitive disadvantage and loss of customer trust. Identifying these document security risks before they escalate is not just good practice, it's essential for survival in today's digital landscape.
Understanding the Landscape of Digital Assets
Your digital assets aren't just servers or databases; they are the countless documents created, shared, and stored daily. These can include PDFs, Word documents, Excel spreadsheets, presentations, images, and even source code files. Each type carries its own set of vulnerabilities and requires specific considerations for protection.
Mapping out where these different document types are stored—whether on local drives, network shares, cloud platforms, or email servers—is a critical first step. This gives you a comprehensive view of your data environment, enabling a more targeted approach to information security assessment.
Common Vulnerabilities
From my experience, common vulnerabilities often stem from human error, outdated processes, or a lack of appropriate tools. Employees might accidentally email sensitive documents to the wrong recipient, or use weak passwords on protected files. Unsecured network shares, cloud storage misconfigurations, and lack of version control are also frequent culprits.
These vulnerabilities create pathways for unauthorized access, modification, or disclosure of sensitive information. Recognizing these typical weak points is fundamental to strengthening your overall data breach prevention efforts.
Your First Line of Defense: Information Security Assessment

An effective information security assessment begins with understanding what you need to protect and why. This isn't a one-time task; it's an ongoing process that adapts to your evolving business needs and the threat landscape. It's about systematically evaluating your current state against desired security postures.
This assessment helps you pinpoint where your greatest document security risks lie. By prioritizing these areas, you can allocate resources effectively and develop a robust strategy for protection, moving beyond reactive measures to proactive defense.
Identifying Critical Documents
Not all documents carry the same level of risk. The first step in any assessment is to classify your documents based on their sensitivity and business impact. What would happen if a particular document were leaked or tampered with? This classification helps you determine which documents require the highest levels of protection.
For example, a marketing brochure might be public, but a quarterly earnings report or a new product design document is highly confidential. Establishing clear classification guidelines and ensuring employees understand them is vital for effective document protection.
Mapping Data Flows
Once critical documents are identified, the next step is to understand their lifecycle. Where are they created? How are they shared internally and externally? Where are they stored? Who has access at each stage? Mapping these data flows reveals potential points of exposure.
I've seen many companies surprised by how widely some sensitive documents circulate, often through unofficial channels. This mapping exercise is crucial for uncovering shadow IT usage and ensuring that security controls are applied consistently across all touchpoints.
Practical Steps for Risk Analysis
Conducting a thorough risk analysis involves evaluating identified vulnerabilities against potential threats. This helps you quantify the likelihood and impact of various document security risks. It's about asking, "What could go wrong, how likely is it, and how bad would it be?"
This analytical approach allows you to move beyond general concerns to specific, actionable insights. Prioritizing risks based on their severity ensures that your mitigation efforts are focused on the areas that pose the greatest danger to your organization.
Technical Controls Review
A technical review examines the existing security mechanisms in place. This includes encryption protocols for documents at rest and in transit, access control lists (ACLs) on file shares, data loss prevention (DLP) solutions, and secure configuration of cloud storage. Are these controls adequately configured and consistently applied?
For instance, checking if documents stored on SharePoint or Google Drive have proper sharing permissions and if external sharing is restricted can uncover significant vulnerabilities. This technical deep dive is essential for identifying gaps in your digital fortifications.
Human Element and Training
Technology alone cannot solve all document security risks. The human element is often the weakest link. Employees must be educated on best practices, such as recognizing phishing attempts, using strong, unique passwords, and understanding document classification policies.
Regular security awareness training, coupled with clear guidelines on handling sensitive information, significantly reduces the likelihood of human error leading to a data breach. It's about fostering a culture of security where everyone understands their role in protecting company data.
Building a Proactive Data Breach Prevention Strategy
After assessing your document security risks and conducting a thorough risk analysis, the final step is to build a robust and proactive data breach prevention strategy. This involves implementing new controls, refining existing ones, and establishing a continuous monitoring framework.
A truly proactive strategy ensures that security is embedded into every process, rather than being an afterthought. It's about creating a resilient environment that can withstand evolving threats and minimize the impact of any potential incidents.
Implementing Robust Policies
Clear, enforceable policies are the backbone of any strong security posture. These should cover document classification, access control, data retention, incident response, and employee responsibilities. Policies must be communicated effectively and regularly reviewed to ensure they remain relevant.
For example, a policy mandating encryption for all sensitive documents shared externally, or requiring multi-factor authentication for accessing critical file repositories, provides a clear framework for secure operations. Such policies are vital for effective data breach prevention.
Continuous Monitoring and Improvement
The threat landscape is constantly changing, so your security strategy must evolve with it. Continuous monitoring of document access logs, DLP alerts, and user behavior helps detect suspicious activities early. Regular audits and penetration testing can identify new vulnerabilities before they are exploited.
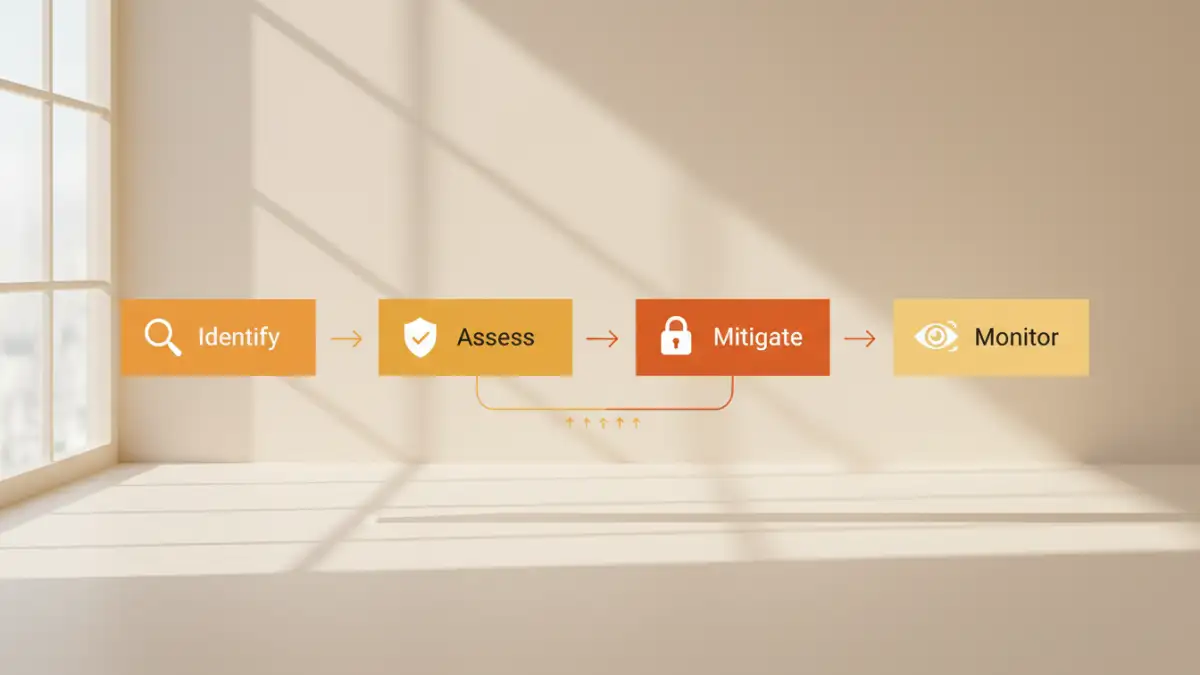
Furthermore, post-incident reviews, even for minor security events, provide valuable lessons for improvement. This iterative process of assess, implement, monitor, and refine is crucial for maintaining a strong and adaptable security posture against document security risks.
Document Security Risk Assessment Areas Comparison
| Assessment Area | Focus | Key Activities | Benefits for Data Breach Prevention |
|---|---|---|---|
| Technical Controls | Software, Hardware, Network Security | Review encryption, access controls, DLP tools, network segmentation | Directly mitigates unauthorized access and data exfiltration |
| Human Element | Employee Behavior, Training, Awareness | Assess security awareness programs, phishing simulations, policy adherence | Reduces human error, insider threats, and social engineering risks |
| Process & Policy | Document Lifecycles, Data Handling Procedures | Examine data classification, retention, sharing policies, incident response plans | Ensures consistent security practices and regulatory compliance |
| Third-Party Risk | Vendor & Partner Security Posture | Audit vendor contracts, security certifications, data sharing agreements | Protects data shared with external entities, prevents supply chain breaches |