
The ease of sending digital files has revolutionized how we work, but it has also introduced significant security vulnerabilities. When sensitive information leaves your control, especially through email or cloud sharing without proper protection, it enters a realm of potential exposure. I've seen firsthand how a seemingly minor oversight in document security can lead to major headaches.
Many professionals assume that simply sending a file means it's safe, or that internal communications are inherently secure. This is a dangerous misconception. The digital pathways documents travel are often less protected than we imagine, making the assessment of risks associated with unencrypted document transmission a critical step for any organization or individual handling sensitive data.
Table of Contents
Understanding the Basics of Document Transmission
At its core, document transmission refers to the process of sending or receiving files from one point to another. This can occur via email attachments, file-sharing services, cloud storage platforms, or even physical media. Without explicit security measures, these transmissions often travel over networks that may not be fully secured, leaving data vulnerable.
The Importance of Encryption
Encryption is the process of encoding information so that only authorized parties can access it. When applied to documents, it transforms readable data into an unreadable format, requiring a specific key or password to decrypt. This is the primary defense against unauthorized access during transmission and while stored.
Key Risks of Unencrypted Document Transmission
The most significant risk of sending an unencrypted document is unauthorized access. This can manifest in several ways, leading to severe consequences:
Data Breach and Confidentiality Loss: Sensitive company data, client lists, financial reports, or personal information can be exposed to competitors, malicious actors, or the public. This loss of confidentiality can damage reputation and trust.
Compliance Violations: Many industries are governed by strict regulations (like GDPR, HIPAA, CCPA) that mandate the protection of sensitive data. Transmitting unencrypted documents containing protected information can lead to hefty fines and legal repercussions.
Intellectual Property Theft: Proprietary designs, trade secrets, or innovative plans sent without protection are prime targets for theft, undermining a company's competitive advantage.
Reputational Damage: A data breach resulting from poor security practices can severely damage a company's reputation, leading to a loss of customer trust and market share.
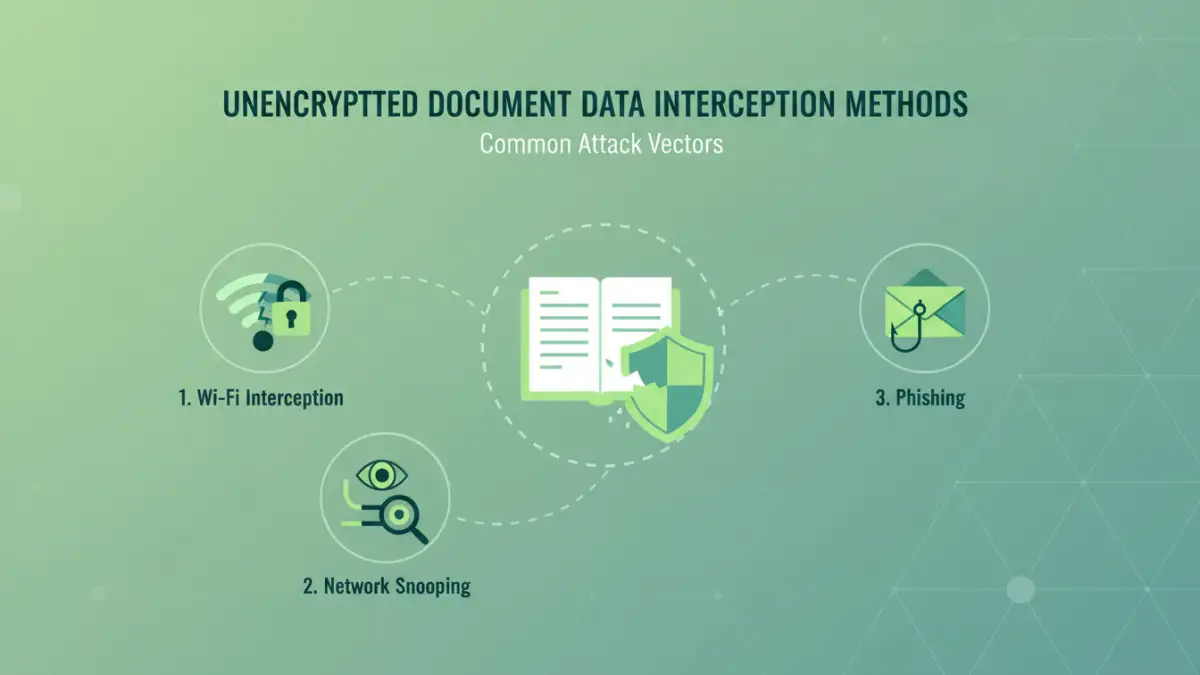
Common Methods of Data Interception
Understanding how data can be intercepted is crucial to appreciating the risks of unencrypted document transmission. Attackers employ various techniques:
Man-in-the-Middle (MitM) Attacks: In these attacks, an attacker secretly relays and possibly alters the communication between two parties who believe they are directly communicating with each other. This is common on public Wi-Fi networks.
Network Snooping: Without encryption, data packets traveling across networks can be captured and read by anyone with the right tools and access. This is akin to eavesdropping on a conversation.
Phishing and Social Engineering: While not direct interception of transmission, these methods can trick users into revealing credentials or downloading malicious files, indirectly leading to data compromise.
Insider Threats: Malicious or careless employees with network access can also intercept or misuse data, even if it's intended for legitimate external transmission.
Strategies for Secure Data Transmission
Fortunately, there are robust methods to ensure your documents are protected during transit. Implementing these strategies significantly reduces the risk of interception and unauthorized access.
End-to-End Encryption
This is the gold standard for secure communication. With end-to-end encryption, the data is encrypted on the sender's device and can only be decrypted by the intended recipient's device. Even the service provider cannot access the content. Many secure messaging apps and some email services offer this feature.
Secure File Transfer Protocols (SFTP) and VPNs
For larger files or more sensitive transfers, using SFTP (Secure File Transfer Protocol) or a Virtual Private Network (VPN) can provide a secure tunnel for data transmission. SFTP encrypts the entire file transfer process, while a VPN encrypts all network traffic from your device.
Password-Protected Documents with Secure Key Exchange
While encrypting a document with a password is a good first step, the security of the password itself is paramount. Sharing the password through a separate, secure channel (e.g., a phone call, a secure messaging app, or a dedicated password manager) is essential to avoid the risk of interception of both the document and its key.
Best Practices for Protecting Confidential Information
Beyond specific transmission methods, adopting a security-conscious mindset is vital. Regularly review your data handling policies and educate your team on the importance of secure practices. Always consider the sensitivity of the information before choosing a transmission method.
Comparison Table: Document Security Methods
| Method | Pros | Cons | Use Case |
|---|---|---|---|
| Email Attachment (Unencrypted) | Quick, convenient | High risk of interception, no security | Non-sensitive internal memos |
| Password-Protected Document | Built-in feature, basic protection | Password can be intercepted, limited encryption strength | Sharing moderately sensitive files |
| Secure File Transfer Protocol (SFTP) | Strong encryption, reliable for large files | Requires setup, client software | Large sensitive data transfers |
| End-to-End Encrypted Messaging/Email | High security, protects content from provider | Requires compatible apps/services, may not support large files | Real-time secure communication, sharing sensitive snippets |
| Virtual Private Network (VPN) | Encrypts all traffic, protects on public networks | Can slow down connection, doesn't encrypt file content directly | Securing all online activity |