
As businesses expand, the volume and sensitivity of the documents they handle inevitably increase. Protecting this data becomes not just a best practice, but a critical necessity. Without a robust strategy, sensitive client information, proprietary research, and financial records can become vulnerable.
My experience has shown that many growing companies often start with ad-hoc security measures. While these might suffice initially, they rarely scale effectively. This is where understanding and implementing scalable document encryption solutions becomes paramount for long-term business document security.
Table of Contents
Understanding Scalability in Encryption
Scalability in document encryption means that the chosen solution can handle an increasing amount of data and users without significant performance degradation or a disproportionate increase in cost. For a growing business, this is vital. A system that works for 50 employees might buckle under the demands of 500.
This involves considering factors like the efficiency of the encryption algorithms, the infrastructure supporting the encryption (e.g., cloud vs. on-premise), and the ease of managing keys and access for a larger user base. True scalable document encryption ensures that security doesn't become a bottleneck as your company grows.
Key Considerations for Growth
When evaluating scalability, think about how easily you can add new users, integrate with existing systems, and manage encryption policies across different departments. A solution that requires extensive manual intervention for every new user or file type will quickly become unmanageable. The ability to automate processes and maintain consistent security posture is key.
Common Encryption Methods

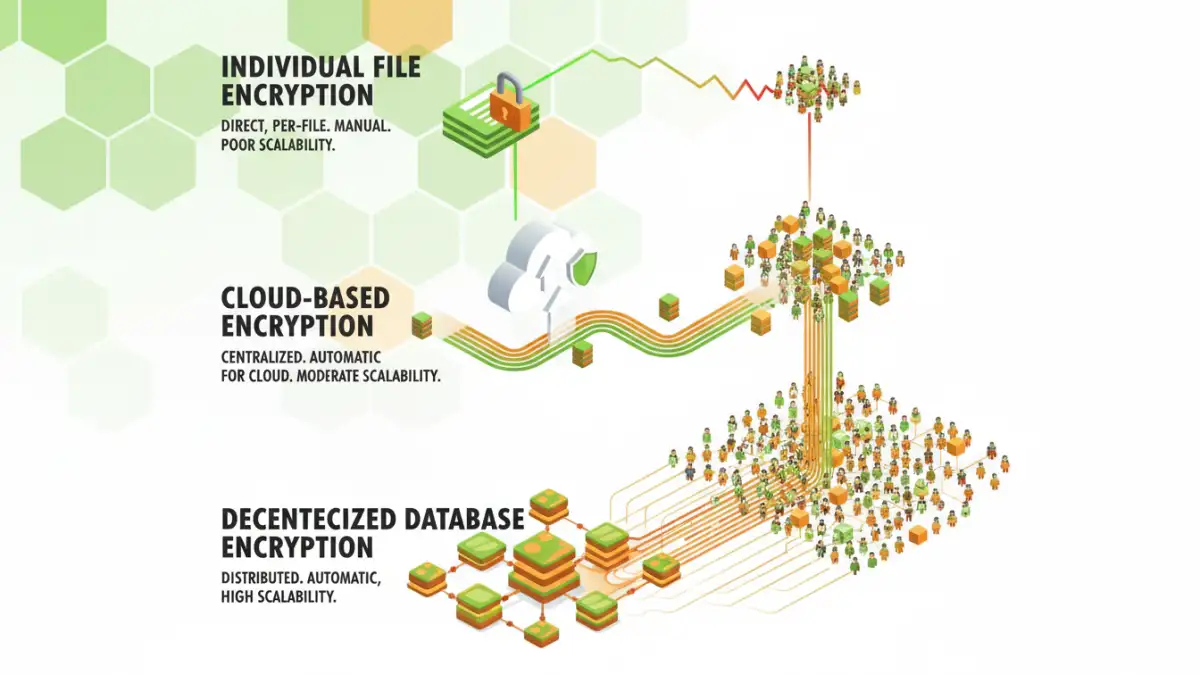
There are several approaches to encrypting documents, each with its own strengths and weaknesses when it comes to scalability and business document security.
File-Level Encryption
This involves encrypting individual files or folders. Tools like VeraCrypt or built-in operating system features (like BitLocker for Windows or FileVault for macOS) can achieve this. While effective for individual documents, managing encryption for thousands of files across many users can become complex.
Application-Level Encryption
Many productivity suites, like Microsoft Office or Google Workspace, offer built-in encryption features for their documents. These are often user-friendly and integrate well with existing workflows. However, the security is dependent on the application's implementation and may require specific versions or licenses.
Database Encryption
For businesses that store large amounts of document data in databases, encrypting the database itself or specific fields can be a highly scalable approach. This method protects data at rest but doesn't typically encrypt documents once they are exported or shared.
Cloud Storage Encryption
Most major cloud storage providers offer some form of encryption, both in transit and at rest. For growing businesses, this can be a very scalable option, as the provider manages the infrastructure. However, understanding the provider's encryption policies and key management practices is crucial.
Choosing the Right Solution
Selecting the appropriate encryption solution depends heavily on your business's specific needs, budget, and technical capabilities. A small startup might find application-level encryption sufficient, while a larger enterprise might require a more comprehensive enterprise encryption solution.
Consider factors like ease of use for your employees, compliance requirements (e.g., GDPR, HIPAA), and the need for centralized key management. Often, a hybrid approach combining several methods might offer the best balance of security and manageability for document protection growth.
Assessing Your Needs
Before committing to a solution, conduct a thorough audit of the types of documents you handle, where they are stored, who needs access, and what regulatory standards you must meet. This assessment will guide you toward a solution that is not only secure but also practical for your operations.
Implementation Best Practices
Implementing any new security measure requires careful planning. For scalable document encryption, this means more than just installing software. It involves policy, training, and ongoing management.
Ensure that strong password policies are enforced if passwords are used for encryption keys. Automate deployment of encryption software where possible and provide clear training to all employees on how to use the encryption tools correctly and securely. Regular audits of your encryption status and access logs are also essential.
Future-Proofing Your Encryption Strategy
The threat landscape and technology both evolve rapidly. What is considered secure today might not be tomorrow. Therefore, your scalable document encryption strategy should include a plan for regular review and updates.
Stay informed about emerging encryption standards and potential vulnerabilities. Consider solutions that offer flexibility and are adaptable to new technologies, such as quantum-resistant cryptography, as it becomes more prevalent. This proactive approach ensures your business document security remains robust.
Comparison Table
| Encryption Method | Scalability | Management Complexity | Typical Use Case |
|---|---|---|---|
| File-Level Encryption | Moderate | High (for many files/users) | Individual sensitive files, small teams |
| Application-Level Encryption | High (within ecosystem) | Low (if integrated) | Documents created in specific suites (Office, Google) |
| Database Encryption | Very High | Moderate (DBA expertise needed) | Large datasets, structured data storage |
| Cloud Storage Encryption | Very High (provider managed) | Low (provider managed) | General file storage, collaboration |
| Enterprise Encryption Solutions | Very High | Moderate to High (requires dedicated management) | Large organizations, strict compliance, centralized control |