The need to share files securely is constant, whether it's sensitive client data, proprietary intellectual property, or confidential internal documents. Manually managing these transfers can be time-consuming, prone to human error, and a potential security risk. I've seen firsthand how organizations struggle with inefficient processes that leave them vulnerable. Automating these workflows isn't just about convenience; it's a critical step towards robust data protection and seamless collaboration.
Table of Contents
Understanding Secure File Sharing Automation
At its core, secure file sharing automation involves setting up systems and processes that automatically handle the secure transfer, storage, and management of files without manual intervention. This means defining rules and triggers for when files should be sent, to whom, and using what security measures. It's about building a reliable, repeatable system that minimizes risk.
What It Entails
This often involves integrating various tools and platforms, such as cloud storage, encryption services, and workflow automation software. The goal is to create a streamlined process where sensitive information moves from point A to point B securely and efficiently, with audit trails for compliance. A well-designed workflow for secure files is crucial for any business handling sensitive data.
Key Benefits of Automation
Implementing automated secure sharing offers significant advantages. Firstly, it drastically reduces the chances of human error, such as sending files to the wrong recipient or forgetting to encrypt them. This enhanced accuracy leads to improved data integrity and security.
Secondly, automation boosts efficiency. By removing manual steps, employees can focus on more strategic tasks. This also speeds up business processes, leading to quicker turnaround times for projects and client requests. The overall workflow for secure files becomes much more agile.
Building Your Secure File Sharing Workflow
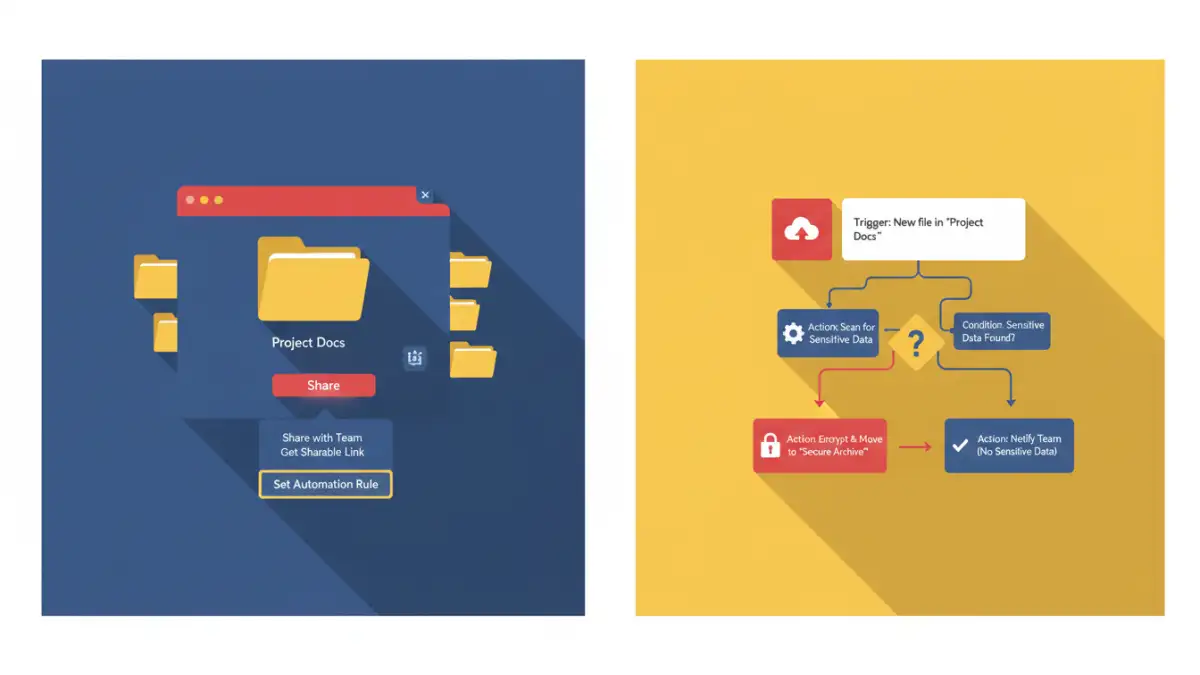
Creating an effective automated secure sharing process starts with a clear understanding of your specific needs. Identify the types of files you share, their sensitivity levels, the recipients, and the frequency of sharing. This analysis will dictate the tools and methods you employ.
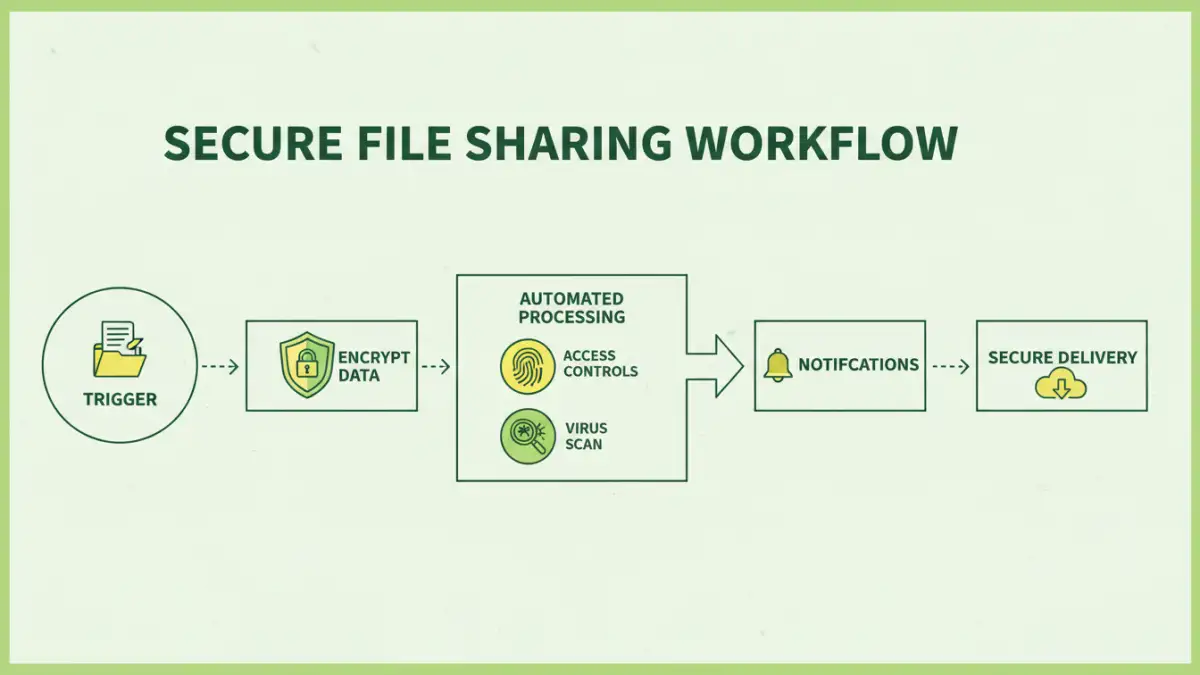
Step 1: Define Triggers and Actions
Determine what initiates the file sharing process. This could be a new file added to a specific folder, an email with an attachment, or a form submission. Once triggered, define the automated actions: encryption, uploading to a secure location, sending notifications, or sharing with specific users.
Step 2: Select Security Measures
Choose appropriate security protocols. This might include end-to-end encryption, access controls, password protection, or secure file transfer protocols (SFTP). The chosen methods should align with the sensitivity of the data being shared and any regulatory requirements.
Step 3: Implement and Test
Set up your chosen automation tools and configure the workflow. Rigorously test the entire process with dummy files and various scenarios to ensure it functions as expected. Verify that security measures are correctly applied and that files reach the intended recipients without issues.
Tools and Technologies for Automation
Several types of tools can facilitate secure file sharing automation. Cloud storage platforms like Google Drive, Dropbox, and OneDrive offer built-in sharing controls and integration capabilities. Many also provide APIs that allow for further automation.
Dedicated workflow automation tools, such as Zapier, IFTTT, or Microsoft Power Automate, are excellent for connecting different applications. You can create 'zaps' or 'flows' that trigger secure file actions based on events in other services. Encryption software and secure file transfer services also play a vital role in ensuring data protection during transit and at rest.
Best Practices for Secure Automation
To ensure your automated secure sharing remains effective, adhere to best practices. Regularly review and update your security protocols as threats evolve. Implement robust access controls and the principle of least privilege, ensuring users only have access to the files they need.
Maintain clear audit logs of all file sharing activities. This is essential for tracking who accessed what, when, and for compliance purposes. Educate your team on the importance of data security and the proper use of automated sharing systems. Finally, choose reputable tools and services that have strong security track records.
Comparison Table: Secure File Sharing Automation Methods
| Method | Pros | Cons | Ideal Use Case |
|---|---|---|---|
| Manual Sharing with Encryption | High control over individual files | Time-consuming, prone to error, difficult to scale | Occasional sharing of highly sensitive documents |
| Cloud Storage Integrations | Easy to use, accessible, collaboration features | Reliance on provider security, potential access issues if not configured correctly | Team collaboration, internal document sharing |
| Workflow Automation Tools (Zapier, Power Automate) | Connects disparate systems, highly customizable, scalable | Can involve subscription costs, requires setup and maintenance | Complex, multi-step processes involving various applications |
| Dedicated Secure File Transfer Services | Robust security features, audit trails, compliance-focused | Can be more expensive, might have a steeper learning curve for advanced features | Large file transfers, external client sharing, strict compliance needs |