Working with sensitive documents often involves a tedious dance of encryption, access controls, and secure sharing. For years, I've seen how manual processes can lead to errors, delays, and vulnerabilities. The sheer volume of digital information we handle daily means that relying on manual oversight for document security is no longer a sustainable or effective strategy. It's time to move beyond the old ways and embrace solutions that can keep pace with our needs.
The challenge isn't just about protecting information from external threats; it's also about ensuring internal compliance and efficiency. When security measures are complex or time-consuming, people tend to find workarounds, which can inadvertently create new risks. This is precisely why adopting automated approaches to document security is becoming a necessity for businesses and individuals alike.
Table of Contents
Understanding Document Security Automation
At its core, document security automation involves using technology to perform security-related tasks with minimal human intervention. This can range from automatically encrypting files upon creation or saving to implementing robust access controls based on user roles and permissions. The goal is to build security directly into your existing workflows, making it seamless and less prone to human error.
The Role of Automation
When I first started exploring automation for document security, I was looking for ways to reduce the burden on my team. We were spending too much time manually applying passwords and tracking who had access to what. Automation allowed us to define policies – for instance, any document containing 'Confidential' in the title automatically gets encrypted with a specific key and shared only with authorized personnel. This drastically reduced misconfigurations and saved countless hours.
Key Benefits of Automation

The advantages of integrating automation into your document security strategy are numerous. Firstly, it significantly enhances security by ensuring that critical steps are never missed. Policies are applied consistently, reducing the risk of accidental exposure or data breaches caused by human oversight.
Secondly, automation boosts efficiency. By taking over repetitive security tasks, it frees up valuable time for employees to focus on more strategic work. This not only improves productivity but can also lead to cost savings by reducing the need for extensive manual oversight and the potential costs associated with security incidents.
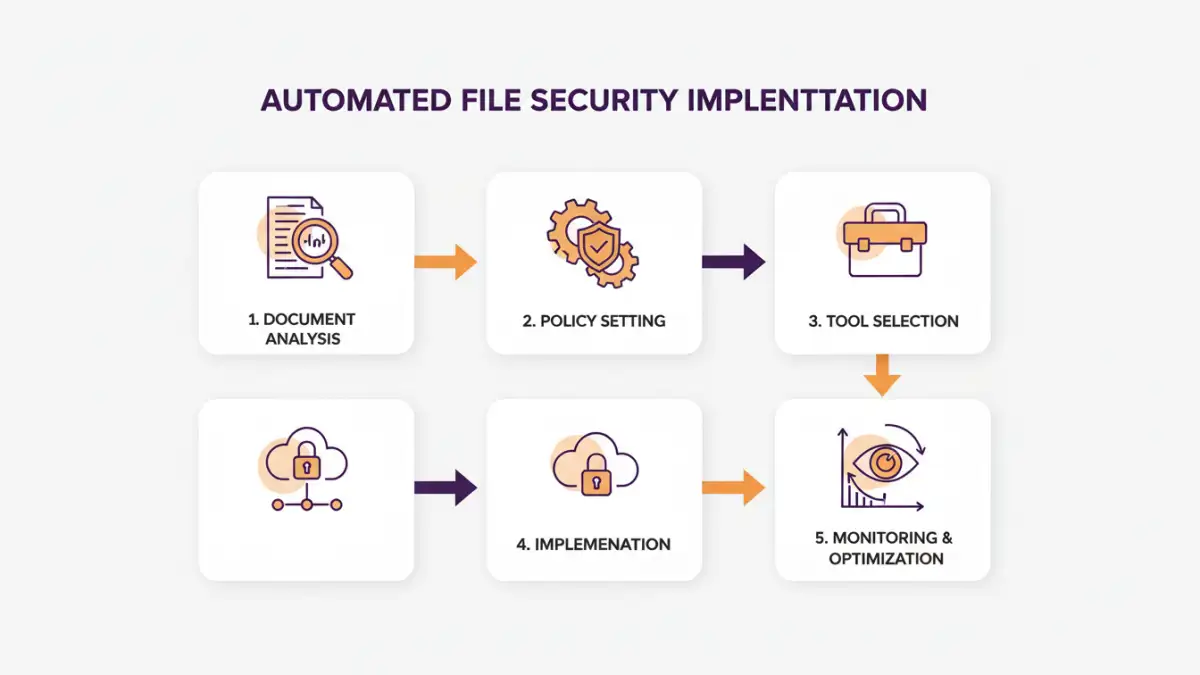
Implementing Automated File Security
Getting started with document security automation requires a thoughtful approach. It's not about flipping a switch; it's about integrating solutions that fit your specific needs and existing infrastructure. I've found that starting with a clear understanding of what needs protection and why is crucial.
Step 1: Assess Your Needs
Before implementing any automation, conduct a thorough assessment of your document types, sensitivity levels, and current security practices. Identify the most critical data and the potential risks associated with its handling. This will help you prioritize which workflows to automate first.
Step 2: Define Policies
Establish clear security policies that dictate how different types of documents should be handled. This includes defining encryption standards, access control rules, retention policies, and audit logging requirements. These policies will serve as the blueprint for your automation efforts.
Step 3: Choose the Right Tools
Select technologies that can enforce your defined policies automatically. This might involve using built-in features of your existing software, dedicated document management systems, or specialized security solutions. The key is to find tools that integrate well into your current environment.
Tools and Technologies
A variety of tools can help you streamline document security. For basic needs, many office suites offer built-in encryption and password protection features that can be applied manually or, with some scripting, semi-automatically. However, for more robust solutions, consider dedicated document management systems (DMS) that often include automated workflows for access control, versioning, and secure sharing.
Cloud storage providers also offer advanced security features, including automated encryption at rest and in transit, as well as granular permission settings. For organizations dealing with highly sensitive data, Data Loss Prevention (DLP) solutions can automatically scan documents for sensitive information and apply predefined security actions, such as blocking sharing or encrypting the file. This level of automated file security is invaluable.
Best Practices for Workflow Document Safety
To ensure your automated document security strategy is effective, adhere to best practices. Regularly review and update your security policies and automation rules to adapt to evolving threats and business needs. Implement comprehensive auditing and logging to track document access and changes, providing visibility and accountability.
Crucially, provide ongoing training to your team on security policies and the proper use of automated tools. While automation reduces human error, user awareness remains a critical component of any strong security posture. Educating your staff about why these measures are in place and how to use the tools correctly will significantly bolster your overall workflow document safety.
Comparison Table: Document Security Automation Methods
| Method | Description | Pros | Cons | Best For |
|---|---|---|---|---|
| Built-in Office Suite Features | Using password protection and encryption within applications like Word or Excel. | Readily available, no extra cost. | Manual application, limited features, easily bypassed if password is weak. | Individual users, basic document protection. |
| Document Management Systems (DMS) | Centralized platforms for storing, managing, and securing documents with automated workflows. | Comprehensive security features, version control, audit trails, role-based access. | Can be costly, requires integration and setup. | Organizations needing robust document control and collaboration. |
| Cloud Storage with Security Features | Utilizing services like Google Drive, Dropbox, OneDrive with their built-in security options. | Automated encryption (in transit/at rest), easy sharing controls, accessibility. | Relies on provider's security, potential privacy concerns with sensitive data. | Teams needing accessible, collaborative, and generally secure document storage. |
| Data Loss Prevention (DLP) Tools | Software that monitors and controls data usage and transfer, automatically enforcing security policies. | Proactive detection and prevention of data leaks, automated policy enforcement. | Complex to configure and manage, can be expensive. | Enterprises with strict compliance requirements and high-value data. |