
Working with structured document files like XML, JSON, or even common office formats such as Word and Excel, we often focus on their utility for organizing and exchanging data. However, beneath their tidy structure lies a landscape of potential security risks. Over the years, I've encountered numerous instances where seemingly innocuous documents became vectors for significant data breaches or system compromises, primarily due to overlooked document security vulnerabilities.
From embedded macros to hidden metadata, these files can inadvertently expose sensitive information or even execute malicious code. Understanding these inherent structured data risks is crucial for anyone involved in handling, processing, or developing applications that interact with such documents. My aim here is to shed light on these common pitfalls and outline effective strategies for exploit prevention.
Table of Contents
Understanding Structured Document Risks
Structured documents are ubiquitous in modern computing. They range from simple configuration files to complex data exchange formats and rich-text documents. Their structured nature, while beneficial for parsing and processing, also provides distinct attack surfaces that unstructured text might not.
The very features that make these files powerful – like embedding executable code, referencing external entities, or storing extensive metadata – are precisely what can be exploited. Attackers continuously look for weaknesses in file format security to gain unauthorized access, elevate privileges, or exfiltrate data. It's a constant cat-and-mouse game.
The Allure of Structured Data for Attackers
Attackers are drawn to structured documents because they often contain valuable information or are processed by applications with elevated privileges. Exploiting a vulnerability in a document parser or a file itself can lead to a cascade of security failures. This makes them prime targets for data security threats.
For instance, a document might traverse multiple systems and users, carrying its embedded risks silently until it reaches a vulnerable application or an unsuspecting user. This broad reach amplifies the potential impact of any successful exploit, making them a high-value target.
Common Security Vulnerabilities

Having worked on various systems that process documents, I've seen a range of vulnerabilities manifest. Each file type and its processing mechanism presents a unique set of challenges. Knowing these common attack vectors is the first step towards effective exploit prevention.
Macro-Enabled Exploits
Perhaps one of the oldest yet still potent threats comes from macro-enabled documents, particularly in Microsoft Office formats. VBA macros, designed to automate tasks, can be weaponized to download malware, steal credentials, or encrypt files for ransomware attacks. Despite warnings and security settings, users can still be tricked into enabling these macros.
I recall a client's system being compromised because an employee opened an Excel file from an unknown sender and clicked 'Enable Content'. It quickly spread, highlighting the persistent danger of these seemingly benign features when not properly managed or understood by end-users.
XML External Entities (XXE) Attacks
XML documents, especially those processed by parsers that don't adequately restrict external entity resolution, are susceptible to XXE attacks. An attacker can craft an XML document that, when parsed, forces the server to disclose local files, perform server-side request forgery (SSRF), or even launch denial-of-service attacks.
This vulnerability stems from the XML standard's ability to define entities that can reference local or remote content. If the parser is misconfigured or lacks proper sanitization, it can fetch and embed content from arbitrary sources, presenting a significant structured data risk.
Metadata Leaks and PII Exposure
Many structured document files store a surprising amount of metadata: author names, creation dates, revision history, comments, and even GPS data from images. This metadata, often hidden from casual view, can inadvertently expose Personally Identifiable Information (PII) or sensitive operational details.
I've seen legal documents where tracked changes revealed internal deliberations, or financial reports that inadvertently contained the network path of the server they were created on. This type of information can be invaluable to an attacker for reconnaissance or social engineering, representing a subtle yet significant document security vulnerability.
Object Injection and Deserialization Flaws
When applications deserialize data from structured formats like JSON, YAML, or even custom binary formats, they can be vulnerable to object injection attacks. If an attacker can control the serialized data, they might be able to inject malicious objects that execute arbitrary code during the deserialization process.
This is particularly dangerous in languages like Java, Python, and PHP, where object graphs can be complex. A seemingly harmless data file could, upon processing, trigger a critical exploit, underscoring the need for careful validation during data parsing.
Mitigating Exploit Risks
Preventing these document security vulnerabilities requires a multi-layered approach, combining technical controls with user education. As an engineer, my focus is always on building robust systems, but I also emphasize the human element.
Robust Input Validation and Sanitization
The cornerstone of exploit prevention for structured documents is rigorous input validation and sanitization. Never trust input, even from seemingly internal sources. For XML, configure parsers to disable external entity resolution by default. For JSON, use schema validation to ensure data conforms to expected structures and types.
For any structured data, assume it's malicious until proven otherwise. Sanitize any embedded scripts, evaluate external references, and ensure all data types are strictly enforced. This proactive approach significantly reduces the attack surface.
Principle of Least Privilege
Apply the principle of least privilege to applications that process structured documents. If an application doesn't need to access the file system, network, or execute arbitrary code, its permissions should reflect that. Sandboxing document processing applications can contain potential exploits, limiting their damage.
Furthermore, consider user permissions. Users should not have elevated privileges when opening untrusted documents. This limits the potential impact if a document-borne exploit manages to bypass other security controls.
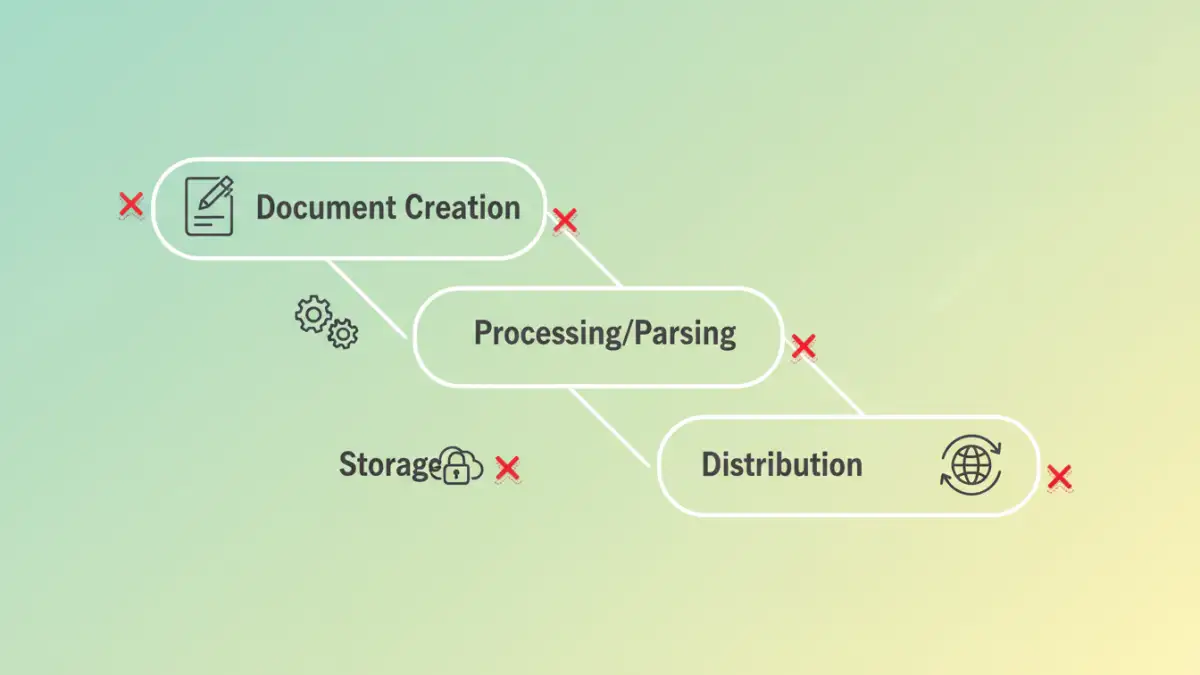
Building a Secure Document Lifecycle
Security isn't an afterthought; it needs to be integrated throughout the entire document lifecycle, from creation to archival. This holistic view helps address structured data risks at every stage.
Secure Configuration and Patch Management
Keep all software that processes structured documents – operating systems, office suites, XML parsers, PDF readers – up to date with the latest security patches. Many document security vulnerabilities are addressed in routine updates. Default configurations should prioritize security over convenience, disabling potentially dangerous features like auto-execution of macros.
Regular security audits of configurations can also help identify and rectify weaknesses before they are exploited. This proactive maintenance is fundamental to maintaining strong file format security.
User Education and Awareness
Finally, the human element is often the weakest link. Educating users about the dangers of opening untrusted documents, enabling macros, or clicking suspicious links is paramount. Regular security awareness training can significantly reduce the likelihood of successful social engineering attacks that leverage document-borne malware.
Foster a culture where users are encouraged to report suspicious documents rather than interacting with them. Tools and technology are vital, but a vigilant and informed workforce is perhaps the most effective layer of defense against data security threats.
Document Security Vulnerability & Mitigation Comparison
| Vulnerability Type | Common Attack Vector | Primary Mitigation Strategy | Impact if Exploited |
|---|---|---|---|
| Macro-Enabled Exploits | Malicious VBA code in Office files | Disable macros, educate users, use trusted locations | Ransomware, data theft, system compromise |
| XML External Entities (XXE) | External entity resolution in XML parsers | Disable external entity processing in parsers | Data disclosure, SSRF, DoS, arbitrary file read |
| Metadata Leaks | Hidden data in document properties | Metadata scrubbing, strict document creation policies | Information gathering, PII exposure, social engineering |
| Object Deserialization | Malicious serialized objects | Strict input validation, avoid untrusted deserialization | Remote Code Execution (RCE), privilege escalation |
| File Format Parsing Errors | Malformed or malformed file structures | Robust, secure parsing libraries, sandboxing | Application crashes, DoS, memory corruption |