
Working with password-protected documents can be frustrating, especially when you've forgotten the password or inherited a file without one. I've encountered this situation numerous times, both for my own sensitive files and when assisting colleagues. The inability to access critical information due to a lost password can halt productivity. Thankfully, specialized tools and techniques exist to help regain access.
This article will guide you through understanding how PDF passwords work, the different types of protection, and the most effective methods for recovering or removing them. Whether you're dealing with a simple password or a more complex encryption, there are solutions available.
Table of Contents
Understanding PDF Password Protection
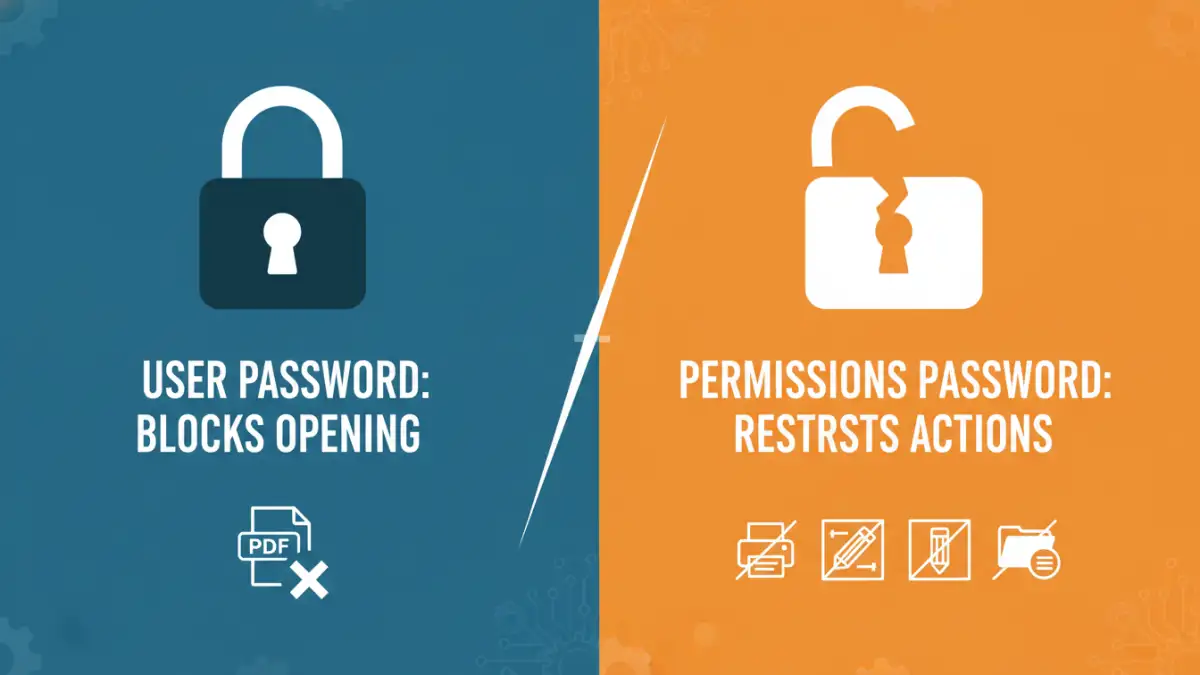
PDFs can be secured using two primary types of passwords: a user password (often called an owner password) and a master password (or permissions password). The distinction is crucial because it dictates the difficulty and methods involved in recovery. Understanding this difference is the first step in selecting the appropriate approach to unlock your file.
Key Concepts in PDF Security
A user password, when set, prevents the PDF from being opened or viewed without it. This is a strong form of encryption. A permissions password, on the other hand, allows the document to be opened but restricts actions like printing, copying text, or editing. Recovering a permissions password is generally much simpler than breaking user password encryption.
Types of PDF Passwords
When a PDF is password-protected, it's essential to know which type of password you're dealing with. This significantly impacts the recovery process. User passwords encrypt the entire document, making it unreadable without the correct key. Permissions passwords, while less restrictive for opening, still protect specific functionalities.
User vs. Permissions Passwords
The user password is the one that stops you from opening the PDF at all. It's typically implemented with strong encryption algorithms. The permissions password, conversely, is applied after the document is opened and controls what you can do with it, like printing, copying, or annotating. My experience shows that recovering permissions passwords is often a matter of a few clicks with the right tool, whereas user password recovery can be a more intensive process.
Methods for PDF Password Recovery
There are several ways to approach recovering a lost PDF password. The method you choose will depend on the type of password, the complexity of the encryption, and the tools you have available. For simple permissions passwords, browser-based tricks or specific online tools can work wonders. For more robust user password encryption, dedicated desktop software is usually necessary.
Browser-Based Workarounds (Permissions Passwords)
For PDFs protected only by a permissions password, a common workaround involves printing the document to a new PDF. You open the protected PDF, go to 'File' > 'Print', and then select 'Save as PDF' or 'Microsoft Print to PDF' as your printer. This process effectively strips the permissions, creating a new, unlocked PDF. This is a quick and free method, but it's ineffective against user passwords.
Dedicated File Recovery Software
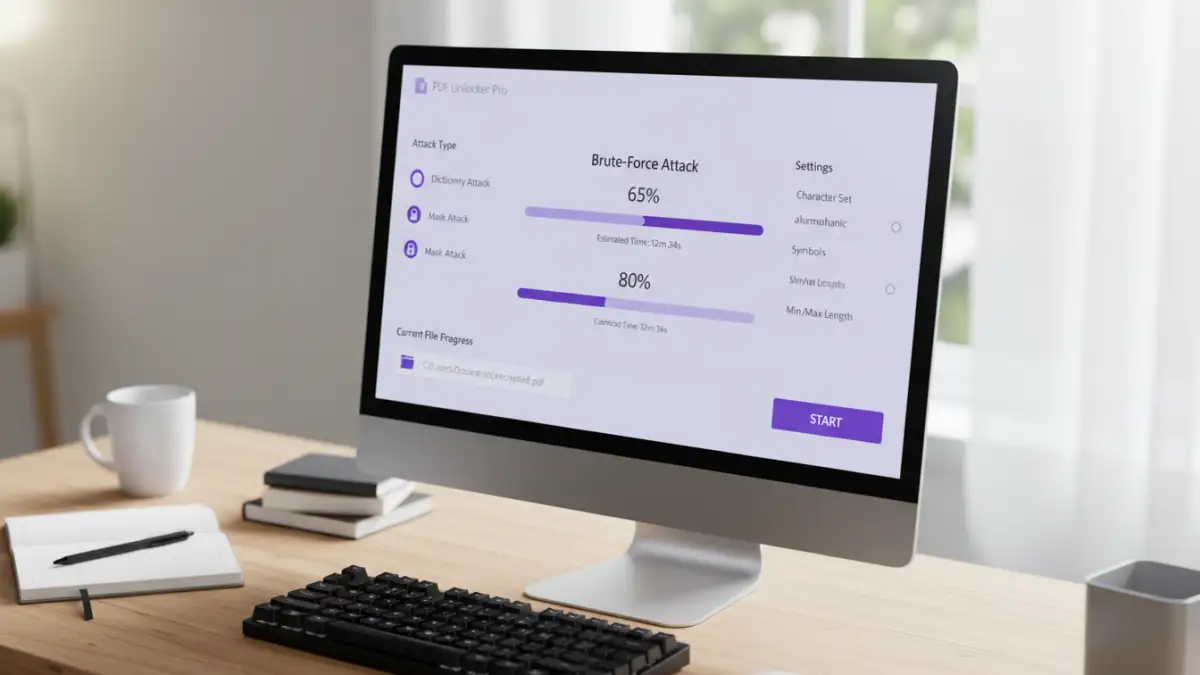
When a PDF is secured with a user password, brute-force attacks or dictionary attacks are often employed by specialized software. These programs attempt to guess the password by trying numerous combinations or common words. The effectiveness and speed of these tools depend on the password's complexity and the software's algorithms. This is where premium PDF password recovery software often shines, offering advanced features and faster processing speeds.
Choosing the Right Tool
Selecting the right software is critical for successful PDF password recovery. Factors to consider include the types of passwords the software can handle, its recovery speed, ease of use, and cost. Some tools offer advanced features like GPU acceleration for faster brute-force attacks or the ability to recover forgotten owner passwords.
Features to Look For
When evaluating a PDF password unlock tool, check if it supports various encryption standards (like 40-bit RC4, 128-bit RC4, AES-128, and AES-256). Look for options like dictionary attacks, brute-force attacks, and mask attacks, which allow you to customize the search. A user-friendly interface and good customer support are also valuable, especially when dealing with complex file recovery software.
Best Practices for Document Security
While recovering lost passwords is a useful skill, preventing the loss in the first place is always the better strategy. Implementing strong password management practices can save you a lot of trouble down the line. Regularly review your password security and update them as needed.
Secure Password Management
Use a reputable password manager to store and generate strong, unique passwords for all your sensitive documents. Avoid using easily guessable information like birthdays or common words. For critical documents, consider backing them up in multiple secure locations, but always ensure those backups are also adequately protected.
Comparison Table: PDF Password Recovery Methods
| Method | Type of Password Handled | Ease of Use | Speed | Cost | Notes |
|---|---|---|---|---|---|
| Browser Print-to-PDF | Permissions Password Only | Very Easy | Fast | Free | Creates a new, unlocked PDF. Doesn't work for user passwords. |
| Online PDF Unlock Tools | Permissions Password Mostly | Easy | Fast | Free/Freemium | Requires uploading file, potential privacy concerns. Limited functionality. |
| Desktop Software (e.g., Advanced PDF Password Recovery) | User & Permissions Passwords | Moderate to Complex | Variable (Slow to Fast) | Paid | Offers brute-force, dictionary, and mask attacks. Handles strong encryption. May require significant processing time. |
| Manual Brute-Force (Advanced Users) | User Password | Very Complex | Very Slow | Free (Software dependent) | Requires technical expertise and specialized tools. Highly time-consuming. |